Understanding security threats for telco edge and private 5G networks
Author: Adil Baghir (edited by Alan J Weissberger)
Introduction:
Telcos and enterprises realize the need to move toward the network edge to deploy cloud-like solutions to leverage the massive advances in transmission offered by 5G. Benefits such as speed, low latency, and capacity will drive major transformation for telcos and enterprises, opening new revenue opportunities from new business models. We’ll examine several 5G deployment scenarios and security threats in this article.
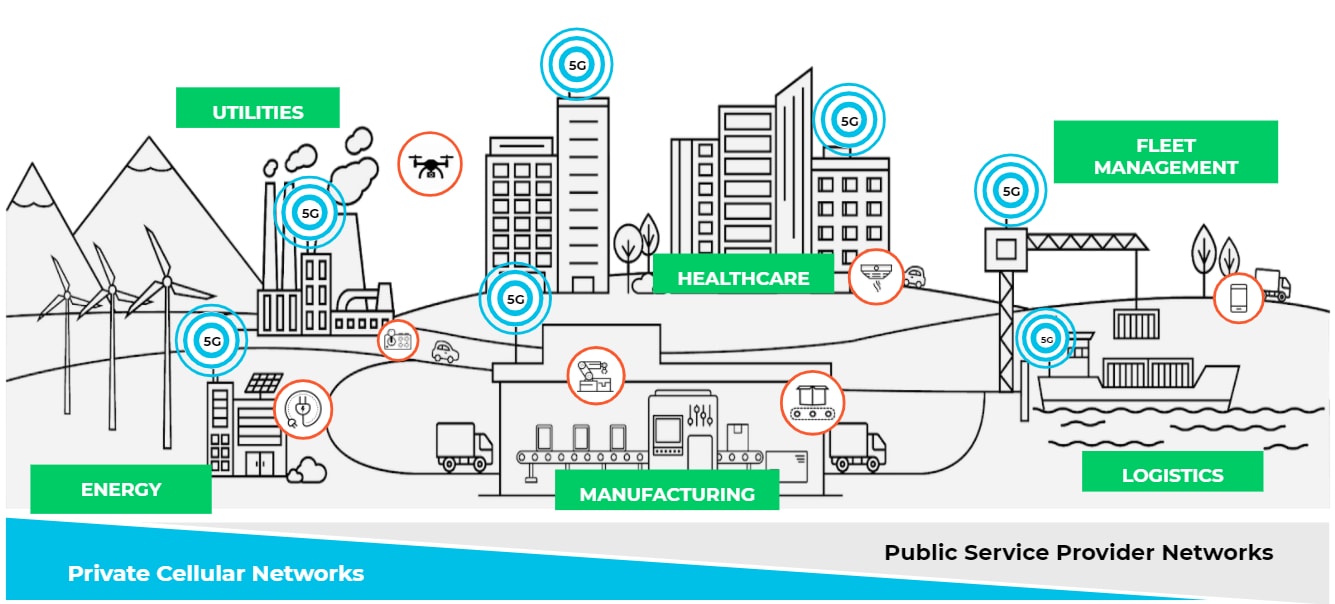
Image Credit: Palo Alto Networks
……………………………………………………………………………………………………………………………………………………………………….
Discussion:
Telcos and enterprises are exploring new use cases by deploying edge clouds and bringing content and applications closer to the users and billions of IoT devices to meet the low-latency requirements. The Ericsson 2022 Mobility Report forecasts that over 30 billion Internet of Things (IoT) devices will be connected by 2027.
The 5G core network functions could be deployed as a microservice in a private data centre of the communications service provider (CSP) and enterprise network or in a public cloud (like AT&T-Microsoft Azure and Dish Network-Amazon AWS).
The shift to the edge and deploying telco cloud edge services and enterprise hybrid private 5G networks introduce new security threats associated with the 5G and edge deployment.
Even though there are security risks with 3G/4G, these risks are mainly associated with external attacks. However, with 5G/MEC/IoT architecture, these risks become more serious. 5G core and edge sites can be attacked from the internal network in an “inside-to-outside” approach. Considering that 5G provides high-speed internet broadband, connecting a massive number of consumer and IoT devices, this can be viewed as a new point of attack for the 5G cloud edge architecture.
Such massive transformation forces telcos and enterprises are deploying cloud edge and private 5G services to rethink their security and network protection. There are many challenges in how telcos and enterprises deploy security solutions today as they cannot provide integrated 5G core and security solutions to adapt with cloud-edge use cases. For example, moving to the edge will require a low footprint, automation, scaling and simplified lifecycle management (LCM). Given the increase in the number of edge sites deployed, it will be very complex to manage and scale different security solutions manually. The typical deployments of security solutions are not optimised for distributed and cloud-edge architectures.
The impact of security compromise on an operator or enterprise edge network could be massive because edge sites usually have less capacity than core sites and host mission-critical applications to accommodate low latency requirements, including IoT use cases. For example, a 10/20G volumetric DDoS attack could have a major impact on the network availability and low-latency requirements, and it would lead to a critical service interruption and result in brand damage.
The shift to cloud and edge for telcos and enterprises is an evolved approach to deploying and delivering services and solutions, and introducing a more dynamic environment. The security measures in place today are not aligned with the cloud-edge requirements for the footprint for physical security solutions, increasing number of edge sites, cloud-native strategy and other required capabilities to improve TCO.
DDoS-based IoT Botnet
Most IoT devices have limited computing resources to provide security functionality and typically are not securely coded. MOZI is an example of a DDoS-focused IoT botnet that utilises a large set of remote code executions (RCEs) to leverage common vulnerabilities and exposures (CVEs) in IoT devices for infection. These devices include network gateways, CCTVs, DVRs, etc. Once the IoT device is successfully infected, the botnet uses protocols/apps, such as TCP/UDP/HTTP, to send and receive configuration updates and attack commands. Eventually, the infected IoT nodes begin generating attack traffic, leading to a massive and sudden spike in UDP traffic going back and forth with peer-to-peer networks. Such volumetric attacks from compromised IoT devices will make it very challenging to guarantee a level of service and maintain low-latency requirements.
Even though it’s always recommended to keep the IoT devices running the latest firmware with all the necessary security patches applied. However, we can’t rely entirely on securing or updating IoT devices. Therefore the network should also be equipped with modern security solutions like DDoS baselining techniques to see anomalous behaviour versus historical norms, and AI/ML techniques, for detection and zero-day attack prevention.
Mobile Edge Cloud and Private 5G Requires New Security Approaches
Security for mobile cloud edge and enterprise hybrid private 5G must be measured carefully to align with the new and increasing security threats. This requires securing the mobile core infrastructure and modern network protection to deliver mission-critical applications while maintaining low latency requirements. Ultimately, this will help telcos and enterprises achieve their desired business outcomes.
In addition, the security implementation for telcos should consider security-as-a-service so that operators may offer secure IoT services leveraging network slicing and provide the flexibility for end customers to manage their security policies with complete network isolation. This requires security integration with the 5G ecosystems to ensure subscriber and device awareness for more agile security control.
Enterprises that deploy private 5G networks may lack the telco experience and knowledge to secure that mobile infrastructure. They might rely entirely on the MNO or their mobile network equipment providers (NEPs) to ensure the infrastructure is fully secured and protected. However, enterprises must extend their network and IT security standards and take all the necessary considerations when they move their critical systems and applications to the edge.
Although 5G comes with embedded security standards, it also introduces potential security risks associated with the deployment model and communications systems. In this post, I have focused on one of the security risks associated with 5G deployment: a DDoS-based IoT botnet. In Part II, I will cover other potential security areas:
- 5G deployment in Hyperscale Cloud Providers (HCP)
- HTTP/2 and exposure of API
- Inert-PLMN
Resources:
Threat Intelligence Report, A10 Global State of DDoS Weapons, H1 2021
Ericsson 2022 Mobility Report, June 2022
Evolving 5G Security for the Cloud, 5G Americas White Paper, Sept 2022
One thought on “Understanding security threats for telco edge and private 5G networks”
Comments are closed.



Cyberattacks are becoming more frequent and more expensive. Tal Liani of BofA Global Research highlights trends such as digitalization, hybrid work, and the transition to public cloud which have increased the attack vector across organizations’ networks. This year, 83% of organizations have experienced multiple breaches, and the average remediation cost was $9.4mn in 1H22, a 4% y/y increase on top of the 13% seen in 2020.