Inside Amazon’s new data center network architecture: quasi random network topology and passive optical devices
Amazon Web Services (AWS) claims it recently achieved a major breakthrough in Data Center Network (DCN) architecture and has been quietly deploying the new technology in its data centers since late last year. Amazon detailed its new networking design in a paper published May 21st titled “RNG: Flat Data Center Networks at Scale.” RNG, or “resilient network graphs,” is built around a quasi-random topology and new passive optical hardware. It’s a “quasi-random” design that combines elements of traditional, structured data networks with the performance advantages of more random architectures.
The goal is to move off conventional hierarchical “fat-tree” designs toward a flatter, more mesh-like fabric that uses far fewer routers and switches, offers more parallel paths, and therefore delivers higher effective throughput at lower power and capex.
“By essentially flattening the network, we eliminated the bottlenecks that come with traditional networking designs,” Matt Rehder, vice president of AWS Network Engineering, said in an exclusive interview with WIRED. “We think we’re the only ones who have done this at scale. RNG is a great fit for our core demands, but AI training data patterns are far more coordinated and centrally orchestrated, so they don’t approximate a random graph.”
The fact that Amazon is using this in the real world is “remarkable,” said Brighten Godfrey, a computer science professor at the University of Illinois Urbana-Champaign and an expert in networking, who was not involved in Amazon’s research. Godfrey coauthored a seminal 2012 paper on random network graphs, which he says are a “mind-bending problem to solve, in general.”
Classic cloud DCNs use structured topologies (Clos/fat-tree) where paths are highly regular and layered (Top of Rack (ToR)–aggregation–core). By contrast, random-graph theory says the most efficient routing networks are flat random graphs: each node connects to a small random subset of others, creating many short, diverse paths and graceful degradation under failures. The problem has always been practical: random cabling at scale is unmanageable, and routing across a huge random graph is nontrivial.
AWS’s “quasi-random” design essentially mixes determinism with randomness: key structural elements are fixed to keep the cabling and deployment manageable, while enough randomness is retained in the interconnect pattern to get the performance and resilience benefits of random graphs. The physical enabler is a new passive optical device called a ShuffleBox that standardizes how switches connect and internally permutes links so that, when many ShuffleBoxes are wired together, the resulting global topology is quasi-random without having to hand-design every link.

Image Credit: Amazon
………………………………………………………………………………………………………………………….
Key architectural pieces and claimed gains:
AWS reports that RNG-based fabrics now serve as the default network architecture for most new AWS data centers, after initial deployments beginning in 2024. The company claims the design:
-
Uses roughly 69% fewer routers/switches than traditional fat-tree DCNs, because the network is flatter and relies more on passive optical fanout.
-
Delivers up to about 33% higher throughput, due to more independent paths and better load spreading.
-
Cuts network equipment power consumption by on the order of 40%, with associated reductions in cooling and operational overhead.
On the control-plane side, AWS developed a routing scheme called Spraypoint. Instead of always following a strict shortest path from source to destination, Spraypoint first “sprays” traffic randomly to neighbors, then directs it via preselected “waypoints” using more conventional shortest-path routing. This hybrid behavior exploits the quasi-random topology to open many more independent paths than standard ECMP-style shortest-path routing would, which in turn improves utilization and resilience under congestion or failures.
Strategic implications:
For AWS’s cloud and AI build-out, this is positioned as a foundational infrastructure advantage: higher bisection bandwidth and lower network energy per bit directly benefit large-scale AI training clusters, storage backends, and multi-tenant cloud workloads. Fewer active devices and more passive optics also translate into lower capex and opex at hyperscale, so AWS is framing this as both a performance and cost/sustainability play that could save billions of dollars and reduce CO₂ emissions over time.
From a networking-theory standpoint, this is notable as one of the first reported at-scale, production deployments of a flat random-graph-inspired topology in a hyperscale DCN, rather than a purely academic or lab system.
In a quasi-random topology like AWS’s RNG fabric, the impact on latency and jitter comes from three main effects: path length distribution, load spreading, and failure behavior.
Baseline latency: path lengths and device count:
In a traditional Clos/fat-tree, average latency is dominated by a fixed number of stages (ToR → agg → core → agg → ToR), so hop count is tightly controlled but you pay for many active devices. A quasi-random, flat graph replaces that rigid hierarchy with many short, irregular paths; on average, shortest paths between any two switches are similar or slightly shorter in hop count than in a fat-tree, and there are fewer active routers in the path because the architecture offloads fanout to passive optics. That tends to keep or slightly reduce median/mean latency per flow, especially under moderate load, because packets traverse fewer serialized queueing points even if the physical graph looks “messier.”
Jitter: congestion and path diversity:
Jitter is driven much more by variable queueing delay than by fixed propagation or serialization. In a quasi-random fabric with many alternate paths and a load-balancing scheme like Spraypoint (random spray + waypoint-based shortest paths), flows can be spread more evenly across the network, reducing hot spots and thus reducing the variance of queueing delay across packets. That can lower jitter compared with a Clos under the same aggregate load, because the system is less likely to funnel many flows through the same few congested uplinks or spine devices.
However, because the routing intentionally uses many different paths, per-flow packet reordering becomes more likely unless constrained by per-flow hashing or waypointing, which can show up as effective jitter at higher layers. AWS’s description of Spraypoint suggests they mitigate this by using waypoints and policy to preserve some path structure, so you get the diversity benefits without unconstrained per-packet spraying.
Under failure and high load:
Where quasi-random really helps latency/jitter is under failure and partial congestion. In a Clos, link or spine failures can force large sets of flows to converge on a smaller subset of remaining equal-cost paths, driving up queueing delay and jitter nonlinearly. In a resilient random-graph-style fabric, node/edge failures simply remove a few edges from a highly connected graph; there are typically many alternative short paths, so the increase in hop count and queueing pressure is smaller and more diffuse. That tends to keep tail latency and jitter (P99, P99.9) better behaved, even if median latency looks similar to a Clos at low load.
So, qualitatively: median latency is roughly comparable to a well-designed Clos, sometimes better due to fewer active stages; jitter and tail latency should improve under realistic, bursty load and failure scenarios, provided the routing stack is designed to limit packet reordering.
Summary and Conclusions:
Quasi-random data center topologies like AWS’s RNG fabric replace rigid Clos/fat-tree hierarchies with a flatter, graph-like network that preserves short path lengths while dramatically increasing path diversity, which tends to hold median latency roughly steady or slightly better by reducing the number of active, queueing devices per path and offloading fanout to passive optics. They primarily improve jitter and tail latency by spreading flows across many alternative routes so congestion is less concentrated, making queueing delays less bursty and keeping P99/P99.9 behavior more stable under failures and hot spots, provided the routing layer (for example, AWS’s Spraypoint approach) constrains packet reordering through way pointing or per-flow consistency.
In conclusion, quasi-random fabrics are less about shaving a few microseconds off baseline latency and more about delivering more predictable end-to-end performance—especially for east–west, latency-sensitive cloud and AI workloads—by trading rigid structure for statistically robust, highly connected graphs that degrade more gracefully when links, nodes, or traffic patterns become pathological.
…………………………………………………………………………………………………………………………………………………………………….
References:
https://arxiv.org/pdf/2604.15261
https://www.wired.com/story/amazon-aws-ceo-matt-garman-ai-agents/
AWS to deploy AI inference chips from Cerebras in its data centers; Anapurna Labs/Amazon in-house AI silicon products
Amazon’s Jeff Bezos at Italian Tech Week: “AI is a kind of industrial bubble”
Data Center Networking Market to grow at a CAGR of 6.22% during 2022-2027 to reach $35.6 billion by 2027
TMR: Data Center Networking Market sees shift to user-centric & data-oriented business + CoreSite DC Tour
Network X Americas: AT&T and Comcast reveal huge AI impact on network operations
Echoing a recent Cisco report, telecom leaders at the Network X Americas conference (held in Irving, TX last week) noted that AI is fundamentally shifting traffic patterns while having a very positive impact on network operations. With billions of connected sensors and devices (like autonomous vehicles generating 20GB of data per day), operators are forced to prioritize uplink capacity and low latency over traditional consumer downlink traffic.
AT&T’s network CTO, Yigal Elbaz, cited the robo-taxi as a bellwether for how AI is affecting network traffic. Each Waymo vehicle generates about 20 gigabytes of data per day, roughly 30 times the amount a typical mobile user consumes. Most of that traffic flows from the car to the cloud. “Every other week,” Elbaz noted, “a new flavor of a frontier AI model drops on us.”
“We already have about 700,000 changes on a daily basis in our network made by AI,” said Elbaz, noting that AT&T has built a proprietary foundation AI model because standard large language models (LLMs) don’t understand KPIs, network alarms or fiber deployment specifics. He cited a 20-25% cost reduction and 12-15% better results than general-purpose models.
In his keynote speech, Comcast EVP and Chief Network Officer Elad Nafshi described 200 edge compute centers capable of self-healing 77% of network events. He touted AI chipsets close enough to customers’ homes to pinpoint outside plant faults with 99.2% precision, and a partnership with Nvidia to push that edge platform further.
Nafshi highlighted the gap in network provider promises vs delivery with a hypothetical small-business use case example. A pizza shop operator, could materially change workflow and productivity if the service provider delivered an AI-enabled concierge—built on a task-optimized small language model—to manage order intake and customer interaction. In that scenario, the network evolves from a passive access pipe into an application-aware platform that augments business operations. The concept is credible from a technical standpoint, but remains largely theoretical until operators can effectively reach and educate SMB customers who still perceive connectivity as a fixed monthly expense.
Both AT&T and Comcast Israeli executives said this was more than modernization and discussed the changes in what a network does. The network is now a platform, not a pipe. Today’s network learns, adapts and increasingly acts on behalf of its customers. But I can’t help but wonder if the customers know… or if that network value will ever trickle down to the customers who need it most.
In a keynote panel session titled, ” Convergence in action – Competing, scaling and winning in the AI-driven connectivity market,” Josh Goodell, AT&T’s VP of Broadband and Converged Product Development, framed the company’s objective as becoming “the greatest simplifier of our customers’ lives” while instilling “connectivity confidence.” That positioning is notable for a sector that has historically under-communicated its value proposition beyond basic service metrics.
The broader industry narrative appears to be shifting. Historically, go-to-market strategies emphasized throughput benchmarks and promotional pricing. As Omdia’s Ruth Brown (panel session moderator) observed, packaging has been largely defensive, optimized around billing constructs rather than differentiated user experience. The emerging model instead centers on networks that operate contextually and autonomously—delivering value in ways that are largely invisible to the end user.
Derek Peterson, CTO of Boingo Wireless, articulated a parallel issue in venue networks, describing the “stadium problem.” Operators dimension infrastructure for peak ingress and then underutilize that capacity once users are inside the venue. The architectural question is no longer solely about capacity provisioning, but about service-layer innovation on top of that capacity. At Petco Park, Boingo leveraged existing network assets to enable pre-entry commerce, driving incremental revenue before fans pass through the gates. The infrastructure was not the constraint; the limiting factor was identifying and executing on higher-order use cases.
A similar disconnect persists in the industry’s framing of the digital divide. AT&T’s John Stankey and others have suggested the gap is nearing closure, citing expanded fiber footprints and fixed wireless access. While coverage metrics have improved, the divide has never been purely a function of infrastructure availability. Adoption is equally constrained by affordability and, critically, by perceived value. If connectivity continues to be positioned as a commoditized utility, the most economically vulnerable segments—those with the greatest need for digital enablement—remain the least likely to engage.
This is particularly relevant in an AI-driven economy. The users and small enterprises that could benefit most from intelligent, network-delivered services are often those least exposed to the evolving capabilities of the platform. The industry risks over-indexing on measurable deployment milestones while under-communicating the functional value of next-generation networks.
The Network X keynotes underscored that the technical roadmap is largely in place. Network operators are advancing toward networks capable of real-time traffic learning, proactive cybersecurity at the edge, and highly personalized in-home connectivity experiences. These capabilities represent a more compelling value proposition than traditional service tier comparisons.
However, the central challenge remains go-to-market execution. The industry has demonstrated that it can architect and deploy these capabilities at scale. It has yet to establish a clear, effective framework for articulating that value to end users and enterprises in a way that drives adoption.
As a final observation, the broader telecom ecosystem—illustrated by developments such as autonomous vehicle platforms—already depends on AI-enabled, highly distributed network intelligence. While the underlying infrastructure is incrementally aligning with these requirements, the industry dialogue around its broader economic and societal implications remains underdeveloped.
References:
Cisco report: Agentic AI to reshape WAN traffic, AI inference will be ~25% of total traffic by 2035
Will the wave of AI generated user-to/from-network traffic increase spectacularly as Cisco and Nokia predict?
Telecom operators investing in Agentic AI while Self Organizing Network AI market set for rapid growth
Analysis: Cisco, HPE/Juniper, and Nvidia network equipment for AI data centers
Cisco CEO sees great potential in AI data center connectivity, silicon, optics, and optical systems
The Financial Trap of Autonomous Networks: Scaling Agentic AI in the Telecom Core
Ericsson integrates Agentic AI into its NetCloud platform for self healing and autonomous 5G private networks
STL Partners webinar: Agentic AI needed for RAN autonomy & efficiency
Nokia to showcase agentic AI network slicing; Ericsson partners with Ookla to measure 5G network slicing performance
Agentic AI and the Future of Communications for Autonomous Vehicles (V2X)
Telecom data centers must be redesigned for the AI era with rack scale architectures, enhanced power & cooling requirements
Is the “far edge” a bridge to far to cross for AI inferencing? What about “Distributed AI Grids”?
T-Mobile US announces new broadband wireless and fiber targets, 5G-A with agentic AI and live voice call translation
Intel and AI chip startup SambaNova partner; SN50 AI inferencing chip max speed said to be 5X faster than competitive AI chips
CES 2025: Intel announces edge compute processors with AI inferencing capabilities
Hurricane Electric establishes carrier neutral PoP at Lincoln Data Centers, Nebraska
Fremont, CA headquartered Hurricane Electric is a leading Internet backbone [1.] and colocation provider specializing in colocation, dedicated servers, direct Internet connections and web hosting. Hurricane Electric operates its own global network, running multiple OC192s, OC48s and Gigabit Ethernet. The ISP offer the following services:
- IP Transit [2.]: Wholesale internet connectivity ranging from 100 Mbps to massive network speeds over IPv4 and IPv6.
- Colocation: Physical rack and cabinet space in their carrier-neutral data centers (primarily in Fremont and San Jose, California) for customer-owned servers.
- Dedicated Servers: Single-tenant servers for businesses seeking dedicated safety, hardware, and performance.
- Web Hosting: Virtual hosting accounts for running and maintaining websites.
Note 1. Hurricane Electric claims to have the world’s largest IPv6-native Internet backbone. President Mike Leber founded Hurricane Electric in a garage in 1994. Hurricane Electric now operates an international backbone network and owns several datacenters, including a new 200,000 square-foot Fremont 2 colocation facility.
Note 2. IP transit is a commercial, wholesale service where an upstream Internet Service Provider (ISP) allows network traffic to travel through its backbone infrastructure to reach the rest of the global internet
Image Credit: Hurricane Electric
………………………………………………………………………………………………………………………………………………………………
Today, the company announced that it has established a new Point of Presence (PoP) at Lincoln Data Centers. The new PoP is located at 206 South 13th Street, Lincoln NE.
Lincoln Data Centers provides a carrier-neutral interconnection and colocation environment purpose-built for organizations with expanding connectivity requirements. The facility combines diverse fiber infrastructure, access to regional and long-haul carriers, low-friction interconnection through meet-me-room capabilities, and flexible deployment options that support scalable growth. Positioned in the geographic center of the United States, Lincoln Data Centers serves as an efficient regional hub for enterprises, cloud platforms, content providers, and network operators seeking resilient, low-latency connectivity across the Midwest and beyond.
The central United States continues to play an increasingly important role in digital infrastructure development due to its geographic advantages, expanding fiber ecosystems, growing enterprise technology adoption, and proximity to major population and business centers. Nebraska’s favorable business environment and central location make Lincoln an attractive market for organizations seeking resilient, low-latency connectivity and diversified network routes.
The new PoP improves fault tolerance, load balancing, and congestion management for next-generation IP connectivity services throughout the region. Customers of Lincoln Data Centers can now access Hurricane Electric’s extensive IPv4 and IPv6 backbone through 100GE (100 Gigabit Ethernet), 10GE (10 Gigabit Ethernet), and GigE (1 Gigabit Ethernet) ports.
“We are pleased to expand Hurricane Electric’s presence in the Midwest with this new Point of Presence at Lincoln Data Centers,” said Mike Leber, President of Hurricane Electric. “Lincoln’s central location, strong business climate, and growing digital infrastructure ecosystem make it an ideal site to support customers requiring reliable, high-capacity Internet connectivity across the region.”
With this deployment, organizations in and around Lincoln can exchange IP traffic directly with Hurricane Electric’s vast global network, which supports more than 40,000 BGP sessions with over 10,500 networks across more than 320 major exchange points worldwide.
The addition of this PoP reflects Hurricane Electric’s ongoing investment in expanding connectivity throughout North America and its commitment to delivering low-latency, highly resilient Internet connectivity for enterprises, cloud providers, research institutions, content platforms, and service providers.
About Hurricane Electric:
Fremont, California-based Hurricane Electric operates its own global IPv4 and IPv6 network and is considered the largest IPv6 backbone in the world. Within its global network, Hurricane Electric is connected to more than 320 major exchange points and exchanges traffic directly with more than 10,500 different networks. Employing a resilient fiber-optic topology, Hurricane Electric has five redundant 100G paths crossing North America, four separate 100G paths between the U.S. and Europe, and 100G rings in Europe, Australia and Asia. Hurricane also has a ring around Africa, and a PoP in Auckland, NZ. Hurricane Electric offers IPv4 and IPv6 transit solutions over the same connection. Connection speeds available include 100GE (100 gigabits/second), 10GE, and gigabit ethernet. Additional information can be found at http://he.net.
References:
Broadcom with Samsung Electronics: Integrated 5G and Wi-Fi 8 FWA Platform
Broadcom has announced a collaboration with Samsung Electronics Co., Ltd. to develop a reference platform for fixed wireless access (FWA) deployments, combining Broadcom’s BCM6776 Wi-Fi system-on-chip (SoC) with Samsung’s B1320 5G modem. The platform is designed to integrate 3GPP Release 17 5G connectivity with emerging IEEE 802.11bn (Wi-Fi 8) capabilities, supporting convergence between wide-area and local-area broadband technologies.
The reference design targets global FWA use cases, where operators seek to deliver high-throughput broadband services using 5G radio access in conjunction with advanced in-home wireless distribution. By aligning 5G and Wi-Fi 8 performance characteristics, the platform addresses requirements for sustained throughput, low latency, and reliability under variable radio conditions. The design also emphasizes scalability for high-volume deployments, with integration intended to reduce system complexity and cost.
The Broadcom BCM6776 is a tri-band Wi-Fi 8 SoC designed for residential and small enterprise access points. It integrates a quad-core Arm-based network processor with Wi-Fi 8 radio functionality in a single device. The SoC supports 2-stream operation with 40 MHz channels in the 2.4 GHz band, and 4-stream operation with up to 160 MHz channels in the 5 GHz and 6 GHz bands. This configuration enables multi-gigabit aggregate throughput while maintaining compatibility with evolving IEEE 802.11bn features.
Integration of compute and radio subsystems within a single SoC reduces bill of materials (BOM) requirements and simplifies hardware design. Power efficiency is also improved relative to prior architectures that relied on discrete components, supporting deployment in thermally constrained residential environments.

Image Credit: Broadcom
…………………………………………………………………………………………………………………………………………………
The Samsung B1320 modem is a 5 nm-class integrated 5G chipset compliant with 3GPP Release 17. It supports peak downlink throughput of up to 3.43 Gbps and uplink throughput of up to 1.17 Gbps, depending on deployment configuration. The modem incorporates a quad-core Arm CPU, RF transceiver, power management functions, and a global navigation satellite system (GNSS) receiver.
The platform further supports non-terrestrial network (NTN) operation, including both NR-NTN and NB-NTN modes, enabling compatibility with satellite-based extensions of 5G coverage.
The combined architecture is designed to sustain end-to-end throughput between the 5G access link and the in-home Wi-Fi network, minimizing bottlenecks between the wide-area and local domains. This is particularly relevant for FWA deployments, where performance is constrained by both radio access conditions and in-premises distribution efficiency.
By providing a pre-integrated reference design, the platform enables original equipment manufacturers (OEMs) and operators to accelerate development cycles and standardize system performance across deployments. This approach supports broader adoption of FWA as a complement to fixed broadband infrastructure, particularly in scenarios where fiber deployment is limited or economically constrained.
“At Computex 2026, we are highlighting that the future of home internet can be both accessible and affordable,” said Joonsuk Kim, Executive Vice President and Head of CP Development at Samsung Electronics. “This platform is designed to deliver reliable performance across a wide range of environments, helping operators bring high-quality connectivity experiences to subscribers.”
“Broadcom is proud to lead the Wi-Fi 8 transition alongside Samsung and our valued ODM partners,” said Vijay Nagarajan, Vice President of Marketing, Wireless and Broadband Communications Division at Broadcom. “This partnership is a game-changer for the FWA market. The combination of Wi-Fi 8 and 5G prioritizes coordinated reliability, giving operators a tool that delivers a consistent experience to every corner of the home.”
Product Features:
The Samsung B1320 is a broadband-optimized 5G platform with the following features:
- 3GPP Release 17
- 4Rx/2Tx radio chain support
- Power Class 1.5 support (TDD bands)
- LPDDR4x / LPDDR5x support
- 1.6 GHz quad-core ARM Cortex-A55 CPU
- 5 Gbps USXGMII, PCIe Gen 3, USB 2.0
- GNSS
- NR-NTN and NB-NTN support for n255 and n256 (L- and S-bands)
The Broadcom BCM6776 is a single-chip Wi-Fi SoC and multi-band radio supporting the following:
- High performance quad-core CPU complex
- Dedicated network processing engine freeing the CPU complex for operator-specific applications and utilities
- Integrated 2×2 2.4 GHz and 4×4 5 GHz and 6 GHz Wi-Fi 8 MAC/PHY/Radio functionality, simplifying system design and lowering cost
- On-chip 2.4 GHz power amplifiers (PAs) and support for third-generation digital pre-distortion for reduced external components and improved RF efficiency
- Versatile memory controller supporting DDR4, LPDDR4, DDR5, and LPDDR5
- Dual PCIe Gen3 controllers to enable simultaneous tri-band applications with a single additional chip
- Integrated multi-gig PHY
A Global Ecosystem of Support:
The launch is supported by the world’s leading original equipment manufacturers (OEMs), who are already integrating the B1320 / BCM6776 platform into their next-generation gateway portfolios.
“HUMAX Networks is delighted to pioneer the next-generation 5G CPE market alongside global technology leaders Broadcom and Samsung. At the recent MWC 2026, we successfully showcased the industry’s first Wi-Fi 8 solution, which integrates Samsung’s cutting-edge 5G technology with Broadcom’s next-generation silicon. Through our ongoing partnership, we remain committed to driving market innovation and consistently delivering top-tier experiences and innovative devices to our global customers,” said Jerry Lee, CEO of Humax Networks.
“We are delighted to collaborate with Broadcom and Samsung to develop our next generation Wi-Fi 8 gateway addressing MSO CBU/FWA market. This solution is capable of delivering a smarter, more secure, and future-ready network optimized solution to meet MSO/FWA customers’ increasing demands of cost competitive 5G NR connectivity,” said Johnson Hsu, SVP & GM of WNC’s Connectivity & Solutions BG.
Availability:
Global carrier trials and OEM sampling of the Samsung B1320 / Broadcom BCM6776 FWA platform are underway.
About Broadcom:
Broadcom Inc. (NASDAQ: AVGO) is a technology leader that designs, develops, and supplies semiconductors and infrastructure software for global organizations’ complex, mission-critical needs. Broadcom combines long-term R&D investment with superb execution to deliver the best technology, at scale. Broadcom is a Delaware corporation headquartered in Palo Alto, CA. For more information, visit www.broadcom.com.
Broadcom, the pulse logo, and Connecting everything are among the trademarks of Broadcom. The term “Broadcom” refers to Broadcom Inc., and/or its subsidiaries. Other trademarks are the property of their respective owners.
…………………………………………………………………………………………………………………..
References:
Extreme Networks deploys Wi‑Fi 7 (IEEE 802.11be) at University of Florida’s “Swamp”
Ookla: FWA Speed Test Results for big 3 U.S. Carriers & Wireless Connectivity Performance at Busy Airports
Aviat Networks and Intracom Telecom partner to deliver 5G mmWave FWA in North America
T-Mobile’s growth trajectory increases: 5G FWA, Metronet acquisition and MVNO deals with Charter & Comcast
Analysis: AT&T 1Q-2026 results: increased fiber penetration, FWA momentum, D2D deals, and mobile/home internet bundles
Latest Ericsson Mobility Report talks up 5G SA networks and FWA
Analysis: Broadcom’s end-to-end 50G PON Edge AI portfolio with WiFi 8 support
Broadcom has announced the BCM68850, a 50G ITU-T PON home gateway system-on-chip (SoC) that integrates a neural processing unit (NPU) and provides native support for emerging Wi-Fi 8 (IEEE 802.11bn) capabilities. The device extends the evolution of broadband access silicon toward higher-capacity passive optical network (PON) standards while maintaining alignment with next-generation in-home wireless technologies. Broadcom is currently sampling the BCM68850 and BCM55050 to its early access customers and partners. Please contact your local Broadcom sales representative for samples and pricing.
The integration of NPU functionality within the gateway reflects an architectural trend toward distributing compute resources closer to the network edge. This enables localized processing of AI-driven workloads within customer premises equipment (CPE), which can reduce upstream bandwidth demand and improve responsiveness for latency-sensitive applications.
Migration to 50G PON, as defined within ongoing ITU-T standardization efforts (e.g., Higher Speed PON), provides increased access capacity and improved latency characteristics relative to earlier generations such as XGS-PON. These enhancements support more deterministic service delivery, particularly in environments where traffic patterns are becoming increasingly burst-oriented and driven by compute-intensive applications.

Image Credit: ADTRAN
…………………………………………………………………………………………………………………………………………………………………………………………………………………………..
In residential networks, traffic is expected to increasingly consist of short-duration, high-throughput bursts associated with edge processing, real-time analytics, and interactive services. A 50G PON gateway can accommodate these patterns by transmitting high-density payloads over sub-millisecond intervals, after which shared channel resources are rapidly released for other users. This behavior contributes to improved utilization efficiency on shared fiber infrastructure.
Low-latency and low-jitter performance are important for emerging application classes, including distributed AI inference, synchronized edge workloads, and multi-stream ultra-high-definition media. These requirements extend across both the access network and the in-home wireless domain, reinforcing the need for coordinated evolution of PON and Wi-Fi technologies.
From a deployment perspective, introduction of 50G-capable CPE provides operators with additional capacity headroom and supports alignment with future service requirements. Coupled with advancements in IEEE 802.11bn, this approach enables continued scaling of residential broadband performance while maintaining consistency across access and local network segments.
BCM68850 – 50G PON Edge AI Gateway SoC:
The BCM68850 is a standalone 50G PON Gateway SoC that provides an industry-standard ITU-T path for operators to future-proof their networks. The device features:
- High-Performance Application Engine: A dedicated CPU for third-party and operator applications leveraging industry available middleware.
- Integrated Neural Engine: A dedicated NPU that accelerates Edge AI inference, reducing cloud latency and enhancing data privacy by keeping sensitive information on premises.
- Symmetric 50G Performance: Delivers full 50G throughput to meet the insatiable appetite for reliable, multi-gigabit bandwidth.
- Wi-Fi 8 Ready: Native compatibility with Wi-Fi 8 standards to ensure the highest reliability and real-world consistency at the broadband edge.
- Intelligent Self-Healing: Enables operators to implement real-time anomaly detection and predictive bandwidth optimization, reducing OpEx and improving ARPU.
- Advanced Security: Incorporates enhanced security algorithms, including Post-Quantum Cryptography (PQC).
“The BCM68850 is a defining milestone for global fiber networks; we are reshaping the broadband edge as the central intelligence hub of the home,” said Philip Radtke, vice president of product marketing for Broadcom’s Wireless and Broadband Communications Division. “This flagship SoC joins our established lineup of NPU-accelerated fiber, cable, set-top box, and Wi-Fi solutions, ensuring operators can efficiently deploy edge-intelligent broadband regardless of the access medium and extend that intelligence all the way to the edge.”
“With ever increasing consumer and enterprise demand for bandwidth and ultra-reliable connectivity, operators are upgrading the Central Office and End Points with 50G PON capability. Next-generation solutions such as Broadcom’s BCM68850 SoC are critical to unlocking the value of this investment by future-proofing the network edge and ensuring high service levels at every node and premise,” said Jaimie Lenderman, practice leader for Optical, IP, and Broadband Infrastructure market research at Omdia.”By establishing a true end-to-end 50G pipe, operators can deliver the massive capacity and deterministic low latency required to support the rigors of the imminent Wi-Fi 8 deployment cycle.”
This end-to-end 50G offering completes the path from Broadcom’s BCM68660 OLT to the edge, providing a seamless and technically robust ecosystem comprising the BCM55050 ONT or the BCM68850 CPE gateway. This architecture introduces a new level of efficiency by optimizing CPU and memory resources for the AI era, ensuring that the home gateway can handle the massive data pipes required for the next decade of digital innovation.
About Broadcom:
Broadcom Inc. (NASDAQ: AVGO) is a technology leader that designs, develops, and supplies semiconductors and infrastructure software for global organizations’ complex, mission-critical needs. Broadcom combines long-term R&D investment with superb execution to deliver the best technology, at scale. Broadcom is a Delaware corporation headquartered in Palo Alto, CA. For more information, visit www.broadcom.com.
Broadcom, the pulse logo, and Connecting Everything are among the trademarks of Broadcom. The term “Broadcom” refers to Broadcom Inc., and/or its subsidiaries. Other trademarks are the property of their respective owners.
References:
https://www.broadcom.com/company/news/product-releases/64341
2026 Fiber Connect Keynote: “The Future of Fiber Optics: AI and the Quantum”
Nokia and Google Fiber trial 50G PON – first in the U.S.
HKT is first to deploy 50G PON technology in Hong Kong
Türk Telekom and ZTE trial 50G PON, but commercial deployment is not imminent
Ooredoo Qatar is first operator in the world to deploy 50G PON
Highlights of FiberConnect 2024: PON-related products dominate
Fiber Connect 2023: Telcos vs Cablecos; fiber symmetric speeds vs. DOCSIS 4.0?
Cisco report: Agentic AI to reshape WAN traffic, AI inference will be ~25% of total traffic by 2035
Executive Summary:
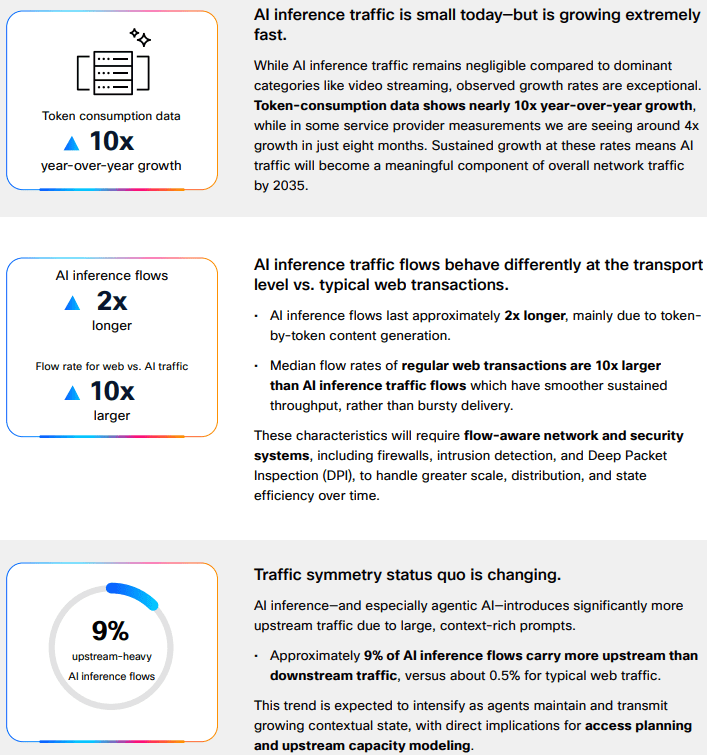
Consumer-driven AI traffic [1.] currently represents a marginal share of aggregate Internet traffic. However, accelerating adoption of agentic AI is expected to materially reshape traffic composition over the next decade. In its “AI Impact on Wide Area Networks” report, Cisco projects that AI will emerge as the dominant driver of network traffic growth. As consumer AI adoption approaches “near-universal usage,” AI and agentic AI are forecast to increase consumer-driven network traffic by approximately 6.6× by the mid-2030s (see chart below).
Cisco estimates that this AI expansion will account for roughly 63% of incremental traffic growth relative to non-AI scenarios. The study focuses specifically on WAN implications, rather than data center or GPU infrastructure, and provides guidance on network design and capacity planning. Methodologically, the report integrates real-world traffic observations (via Cisco Crosswork Assurance User Experience), third-party industry datasets, and controlled laboratory evaluations of AI agents to characterize how AI-generated traffic diverges from conventional web traffic patterns.
Token-consumption data shows nearly 10x year-over-year growth, while in some service provider measurements Cisco is seeing ~4x growth in just eight months. Sustained growth at these rates means AI traffic will become a meaningful component of overall network traffic by 2035.
Note 1. Consumer AI traffic has a few defining technical traits: it is still dominated by short text-based exchanges, but it is becoming more stateful, more upstream-heavy, and more latency-sensitive as users move from simple prompts to agentic workflows and multimodal interactions. Today’s consumer AI traffic is still overwhelmingly text-oriented, which is one reason the aggregate bandwidth impact remains modest despite rapid adoption. Comcast’s network observation is a useful real-world proxy: 97.1% of AI traffic was text-based, while images accounted for 2.6% and video only 0.3%. The key technical implication is that current traffic volumes are often limited more by conversation frequency and session behavior than by very large payloads, though that changes quickly as users adopt image, audio, and video generation.
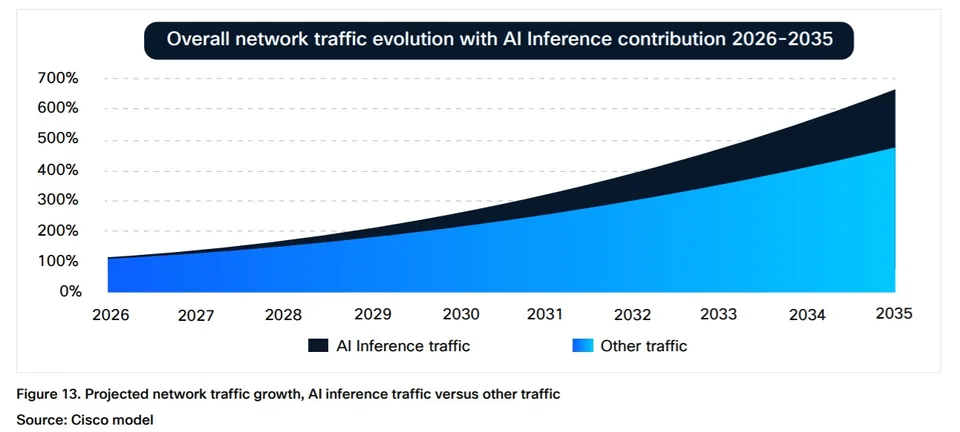
Although AI inference traffic is currently “negligible” relative to dominant categories such as video streaming, Cisco projects it will comprise approximately 25% of total network traffic by 2035 (see chart below). At that point, AI traffic is expected to represent a “meaningful component” of overall network load. Importantly, AI-generated traffic exhibits distinct characteristics: inference flows are approximately twice the duration of typical web transactions, demonstrate higher upstream bandwidth demand, and operate at “software speed” rather than human interaction rates.
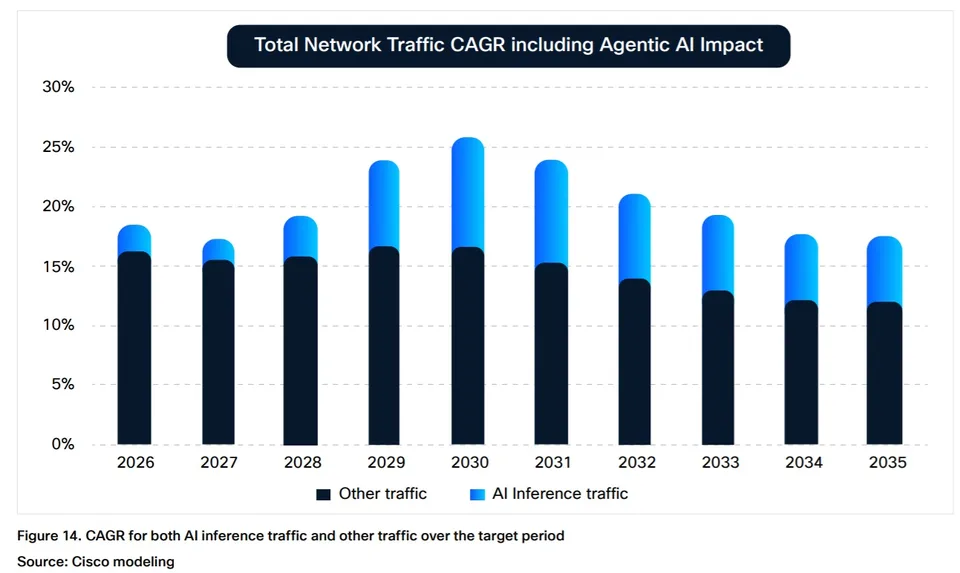
The emergence of AI agents as “power users” further amplifies these dynamics. Cisco notes that agent-executed tasks can generate up to 450% more traffic per task compared to human-driven interactions. This shift is expected to drive operator adoption of “flow-aware network and security systems” as traffic patterns become increasingly machine-driven and less predictable.
Cisco’s broader framing is that AI traffic “isn’t just adding traffic,” but is changing the shape of traffic, with inference flows running about twice as long as typical web transactions and, in some cases, generating up to 450% more traffic per task when an agent executes the workload. AI inference sessions tend to hold resources longer, create more sustained flows, and push operators to think in terms of flow-aware behavior rather than only peak-throughput sizing. Cisco also notes that about 9% of AI inference flows carry more upstream than downstream traffic, versus about 0.5% for typical web traffic, which is a meaningful shift for access and broadband networks. Cisco reports that approximately 9% of AI inference flows are upstream-dominant, compared to roughly 0.5% for traditional web traffic, with this divergence expected to widen alongside increased agentic AI utilization. In parallel, latency sensitivity is anticipated to become a more critical performance parameter for AI-driven applications.
Latency and symmetry:
AI traffic is also more sensitive to latency than many ordinary consumer web transactions because the user experience is often conversational and interactive, with the expectation of near-immediate turn-taking. Cisco describes AI inference as operating at “software speed” rather than human speed, which means small delays can be more noticeable and operationally important. At the same time, upstream demand becomes more significant because prompts, context, attachments, and agent-generated actions can increase return-path traffic, especially as multimodal inputs and agentic tool use expand.
Multimodal growth:
The biggest step-up in technical impact comes when consumer AI shifts from text-only prompting to multimodal generation and agent-driven workflows. In those cases, each task can involve multiple model calls, retrieval steps, tool invocations, and richer media payloads, which expands both flow count and bytes per session. Cisco’s study suggests that this is why AI traffic will increasingly require “flow-aware network and security systems,” because the traffic profile is not just larger, but structurally different from conventional browsing.
Infrastructure Implications:
“AI network traffic is already reshaping infrastructure needs. What we are seeing is clear: AI isn’t just adding traffic. It’s changing the shape of traffic,” Javier Antich, principal product management engineer in the CTO office of Cisco’s provider connectivity group, and Gurudatt Shenoy, SVP, product management, provider connectivity, explained in this blog post.
These shifts are beginning to influence access network evolution. Fiber networks already provide relatively symmetric throughput and low latency, while cable operators are advancing similar capabilities through DOCSIS upgrades. Mid-split and high-split architectures increase upstream spectrum allocation, enabling more balanced capacity profiles. Concurrently, Tier 1 operators such as Comcast and Charter Communications are introducing low-latency enhancements within DOCSIS networks.
Operational data reflects early-stage impacts. Comcast Chief Network Officer Elad Nafshi noted at the Cable Next-Gen event in March that approximately 97.1% of AI traffic on Comcast’s network remains text-based, with images accounting for 2.6% and video just 0.3%, indicating that bandwidth-intensive multimodal AI traffic has yet to scale materially.
Network design impact:
For broadband and access networks, the immediate engineering issues are upstream traffic capacity, queue behavior, and latency consistency rather than raw total throughput alone. Symmetry upgrades (such as DOCSIS mid-split and high-split for MSOs), along with low-latency capabilities, are relevant because consumer AI creates more return-path pressure and more time-sensitive sessions. In other words, the challenge is not simply to carry more bytes; it is to carry more interactive sessions with predictable performance, especially as multimodal and agentic usage scales.
………………………………………………………………………………………………………………………………………………………………………………………………………….
References:
Will the wave of AI generated user-to/from-network traffic increase spectacularly as Cisco and Nokia predict?
Telecom operators investing in Agentic AI while Self Organizing Network AI market set for rapid growth
Analysis: Cisco, HPE/Juniper, and Nvidia network equipment for AI data centers
Cisco CEO sees great potential in AI data center connectivity, silicon, optics, and optical systems
The Financial Trap of Autonomous Networks: Scaling Agentic AI in the Telecom Core
Ericsson integrates Agentic AI into its NetCloud platform for self healing and autonomous 5G private networks
STL Partners webinar: Agentic AI needed for RAN autonomy & efficiency
Nokia to showcase agentic AI network slicing; Ericsson partners with Ookla to measure 5G network slicing performance
Agentic AI and the Future of Communications for Autonomous Vehicles (V2X)
Telecom data centers must be redesigned for the AI era with rack scale architectures, enhanced power & cooling requirements
Is the “far edge” a bridge to far to cross for AI inferencing? What about “Distributed AI Grids”?
T-Mobile US announces new broadband wireless and fiber targets, 5G-A with agentic AI and live voice call translation
Intel and AI chip startup SambaNova partner; SN50 AI inferencing chip max speed said to be 5X faster than competitive AI chips
CES 2025: Intel announces edge compute processors with AI inferencing capabilities
Telecom data centers must be redesigned for the AI era with rack scale architectures, enhanced power & cooling requirements
- Gigawatt-Scale Power and Liquid Cooling: Next-generation AI clusters require unprecedented power density, often exceeding 40kW to 100kW per rack. Telcos cannot simply drop these into existing facilities; they require entirely new or heavily retrofitted data centers featuring advanced liquid cooling architectures to prevent thermal throttling.
- The Fragmented Edge vs. Centralized Fortresses: Operators are realizing that centralized hyperscale data centers (like AWS or Azure clusters in Virginia) cannot support latency-sensitive “Physical AI” or real-time agentic workflows. To make AI-native networking work, carriers must deploy high-density compute racks directly at the network edge, a highly complex and capital-intensive roll-out.
- Neutral Interconnection Hubs: Multi-cloud setups and distributed training workloads are putting immense pressure on backbones. The expansion rate of neutral interconnect hubs (like Equinix and Digital Realty) is directly gating how fast enterprises and telcos can orchestrate data between fragmented training clusters and edge inference nodes.
- Rack-scale architecture is rapidly emerging as the primary deployment unit as enterprises transition from discrete servers to fully integrated systems capable of supporting the power density, thermal constraints, and interconnect requirements of production-scale AI workloads.

Image Credit: AMD
……………………………………………………………………………………………………………………………………………………………………………………………
AI data centers supporting telecom networks require fundamentally different power and cooling infrastructure compared to legacy enterprise facilities. The transition to generative AI and real-time edge processing has pushed power density per rack from an average of 5–10 kW up to 40–100+ kW.
Dell Technologies Inc. has been strategically aligning its portfolio to this shift, and at Dell Technologies World 2026, the company introduced an expanded PowerRack portfolio that integrates compute, networking, and storage within a unified rack-scale platform. This evolution underscores a broader transition in system design priorities—from server-centric architectures to tightly coupled, rack-level systems—driven by the escalating demands of AI infrastructure. As Arun Narayanan, senior vice president of compute and networking product management at Dell, indicated, increasing power density and system complexity are making rack-level architectural optimization not just advantageous, but essential.
“Go back two years ago, the largest, most powerful rack was 80 kilowatts,” Narayanan said. “Come to Vera Rubin, you’re going to get racks of 235 kilowatts, and then get to the next generation of Rubin Ultra and Kyber, you’re going to very quickly get to one megawatt racks. You have to fundamentally redesign everything from power distribution to cooling.”
-
- Medium-Voltage Power Distribution: Traditional facilities step utility power down to 480V AC far from the rack. High-density AI data centers run medium-voltage or power directly down to the row or container level before stepping down. This minimizes conduction losses through the heavy copper busbars.
- The Move to 48V DC Busbars: Within the server chassis, power shelf architectures are shifting from traditional 12V DC distribution to DC busbars. A delivery architecture reduces the current required to deliver the same wattage by a factor of four. Resistive power loss occurs when electrical energy is converted into heat due to the inherent opposition to current flow in a conductor. The formula (P{loss} = I^2 R dictates that this power dissipation is highly sensitive to current changes. Therefore, cutting the current to one-fourth reduces internal rack heat and conduction power losses by 93.75%
- Grid Interconnection and Substation Constraints: A single rack-scale AI cluster (such as a cluster of 32 or 64 interconnected nodes) can easily pull 2 to 3 Megawatts (MW). Operators are bypassing traditional local distribution grids entirely. They are building dedicated on-site substations tied directly to transmission-level lines to guarantee upstream capacity.
[ Liquid Cooling Architectures for AI Racks ]
┌───────────────────────────┐ ┌───────────────────────────┐
│ Direct-to-Chip │ │ Immersion Cooling │
├───────────────────────────┤ ├───────────────────────────┤
│ Closed loop micro-channels│ │ Entire server submerged │
│ bolted directly onto GPUs │ │ in dielectric fluid tank │
│ │ │ │
│ [ GPU ] ──► [ Liquid] │ │ ┌───┐ ┌───┐ ┌───┐ │
│ Cold Plate Coolant │ │ │GPU│ │CPU│ │RAM│ │
│ Circuit Circuit │ │ └───┴─┴───┴─┴───┘ │
└───────────────────────────┘ └───────────────────────────┘
-
- Direct-to-Chip (Cold Plate) Cooling: This is the primary architecture for 2026 deployments. A closed-loop copper block with micro-channels is bolted directly onto high-thermal-flux components like the GPU or CPU. A specialized dielectric or water-glycol fluid circulates through the block. This absorbs heat directly from the silicon via conduction and pumps it away to a secondary heat exchanger.
- Immersion Cooling (Single-Phase and Two-Phase):
-
- Single-Phase: The entire server blade is submerged in a bath of non-conductive, hydrocarbon- or synthetic-based dielectric fluid. The fluid circulates through the chassis via natural convection or pumps to remove heat.
- Two-Phase: The dielectric fluid has a low boiling point (\(50^{\circ }\text{C}\)). The heat from the chips boils the fluid into a vapor. The vapor rises to a condenser coil at the top of the sealed tank, condenses back into liquid, and falls back into the pool. This utilizes the latent heat of vaporization, making it highly efficient.
-
- Cooling Distribution Units (CDUs): High-density loops rely on CDUs to act as the barrier between the internal facility water loops (which can be lower quality) and the ultra-pure, treated water circuit flowing directly through the server cold plates.
References:
China vs U.S.: Race to Generate Power for AI Data Centers as Electricity Demand Soars
Big tech spending on AI data centers and infrastructure vs the fiber optic buildout during the dot-com boom (& bust)
Will billions of dollars big tech is spending on Gen AI data centers produce a decent ROI?
AWS to deploy AI inference chips from Cerebras in its data centers; Anapurna Labs/Amazon in-house AI silicon products
Analysis: Cisco, HPE/Juniper, and Nvidia network equipment for AI data centers
Networking chips and modules for AI data centers: Infiniband, Ultra Ethernet, Optical Connections
Lumen Technologies to connect Prometheus Hyperscale’s energy efficient AI data centers
Tutorial: LEO Satellite Internet connectivity, D2D, and major providers
Satellite Orbits:
Satellite connectivity operates across three orbital tiers:
- Geostationary (GEO) satellites have been the dominant platform for decades, powering telecommunications, TV broadcasting, weather forecasting, military surveillance, rural internet, and satellite phones. Positioned 36,000 kilometres above the equator, a single GEO satellite covers nearly a third of the planet, but the distance creates a 500–700 millisecond signal delay that makes video calls and real-time services impractical. Each satellite is roughly the size of a school bus and requires its own rocket launch.
- Medium Earth Orbit (MEO) satellites sit between 2,000 and 36,000 kilometres above Earth’s surface, with a latency of 70–120 milliseconds. The satellites range from car-sized to van-sized, with a few deployable per launch. MEO satellites are used for GPS and other global navigation systems but have never played a significant role in consumer connectivity.
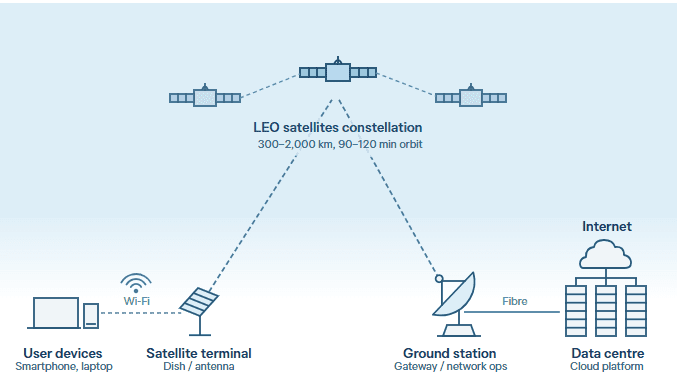
- Low Earth Orbit (LEO) satellites sit at just 300 to 2,000 kilometres above Earth’s surface, bringing latency down to 20–50 milliseconds — on par with home broadband. Their small, flat-panel design, roughly the size of a dining table, allows dozens to be stacked into a single rocket, significantly lowering the cost per satellite. Modern LEO constellations also link satellites directly via laser, forming a mesh network in space. Instead of every signal bouncing through a fixed ground gateway, data travels between satellites and descends at the nearest point, allowing LEO signals to reach oceans, disaster zones, and remote communities that no ground infrastructure will ever serve.
LEO satellites sit between 300 and 2,000 kilometres above Earth, completing an orbit every 90 to 120 minutes and covering different parts of the globe as they move. They communicate with ground stations or through inter-satellite links that relay data between satellites. Supporting infrastructure includes gateway stations, network operation centers, and data centers that manage satellite movements, route traffic, and maintain service reliability. For users, accessing LEO services requires a small satellite terminal — typically a dish — with power and a subscription plan. As shown in the figure below, users connect to a local Wi-Fi network linked to the dish. Data is transmitted to LEO satellites, relayed to a ground station, and then routed through fiber-optic networks to data centers or cloud platforms. The process is reversed for the return signal, completing the connection in milliseconds.
Importantly, LEO satellites are revolutionizing Direct-to-Device (D2D) communications by acting as cell towers in space, allowing standard, unmodified smartphones and IoT sensors to connect seamlessly without terrestrial infrastructure. By utilizing standard mobile-carrier spectrums or dedicated satellite bands, these fast-moving satellites bypass localized coverage gaps to provide ubiquitous, text, voice, and data services in remote, rural, and maritime areas, as well as critical backup during disasters.
LEO satellite internet functional block diagram:
………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………….
Regulatory approval is central to LEO satellite deployment. Providers must typically obtain spectrum licenses, comply with national rules for ground infrastructure, and secure approval for service provision. Requirements vary widely across jurisdictions — from registration to multi-stage authorization processes. Competition from incumbent internet service providers may constrain market entry and expansion. As a result, services may be restricted or delayed even where technical coverage exists.
LEO connectivity also has practical limitations. Terminals require an unobstructed view of the sky, making installation easier in open areas but more difficult in dense urban environments where buildings or trees block the signal. Tropical downpours, heavy rain, or storms can cause signal attenuation and reduce throughput. Compared with terrestrial systems such as fibre-optic or mobile networks, LEO services may deliver less consistent performance, particularly in urban areas, and speeds can drop during peak demand.
Providers of LEO satellite connectivity:
The global space economy is projected to reach US$1.8 trillion by 2035, driven largely by LEO constellations. However, value creation is likely to be concentrated among a small number of providers controlling key parts of the value chain, Financial barriers to entry remain significant, varying depending on mission scope and technical ambition. Amazon Leo (formerly Project Kuiper) will cost more than US$10 billion, while full deployment of SpaceX’s Starlink is estimated at US $20–30 billion.
A mix of private and state-backed operators is developing LEO constellations with different strategies in satellite numbers, coverage, and target markets. Chinese-backed LEO operators GuoWang and Qianfan represent a strategic shift, both advancing rapidly towards full operation with a dual mandate of serving domestic communications and extending broadband connectivity across the Indo-Pacific and beyond. Their emergence could reshape strategic choices for governments in the region.
Where LEO satellite delivers:
LEO satellites are not a universal solution to connectivity gaps, nor a replacement for terrestrial networks. In most countries, fibre-optic and mobile infrastructure will remain the primary source of broadband connectivity. Their value lies in specific contexts: serving remote communities beyond the economic reach of terrestrial investment; providing resilient backup when ground networks fail; and supporting connectivity where no viable alternative exists.
LEO satellites are increasingly used to enhance resilience in countries with extensive fiber-optic networks or high exposure to natural disasters. They can provide automatic failover — near instantaneous transition to a standby system — during submarine cable outages, power failures, or other disruptions, maintaining communications and supporting emergency response. In December 2024, earthquakes in Vanuatu disrupted contact with national disaster authorities until Starlink was activated. In April 2025, a blackout in Spain and Portugal cut power to thousands of mobile towers, halving terrestrial network capacity — Starlink maintained connectivity via ground stations in Italy.
The main advantage is network independence: LEO satellites operate separately from terrestrial infrastructure and continue functioning when ground systems fail. Integrating LEO satellites into national disaster frameworks, rather than relying on ad hoc deployment, would maximize resilience.
………………………………………………………………………………………………………………………………………………………………………………………………………………….
References:
https://www.telecoms.com/satellite/satellite-disruption-how-leo-and-d2d-are-impacting-telecoms
Analyst firms wide forecasts for the LEO satellite direct-to-device (D2D) market
Analysis: SpaceX FCC filing to launch up to 1M LEO satellites for solar powered AI data centers in space
Blue Origin announces TeraWave – satellite internet rival for Starlink and Amazon Leo
Open Cosmos introduces global space-based LEO satellite service for IoT monitoring
China ITU filing to put ~200K satellites in low earth orbit while FCC authorizes 7.5K additional Starlink LEO satellites
Amazon Leo (formerly Project Kuiper) unveils satellite broadband for enterprises; Competitive analysis with Starlink
GEO satellite internet from HughesNet and Viasat can’t compete with LEO Starlink in speed or latency
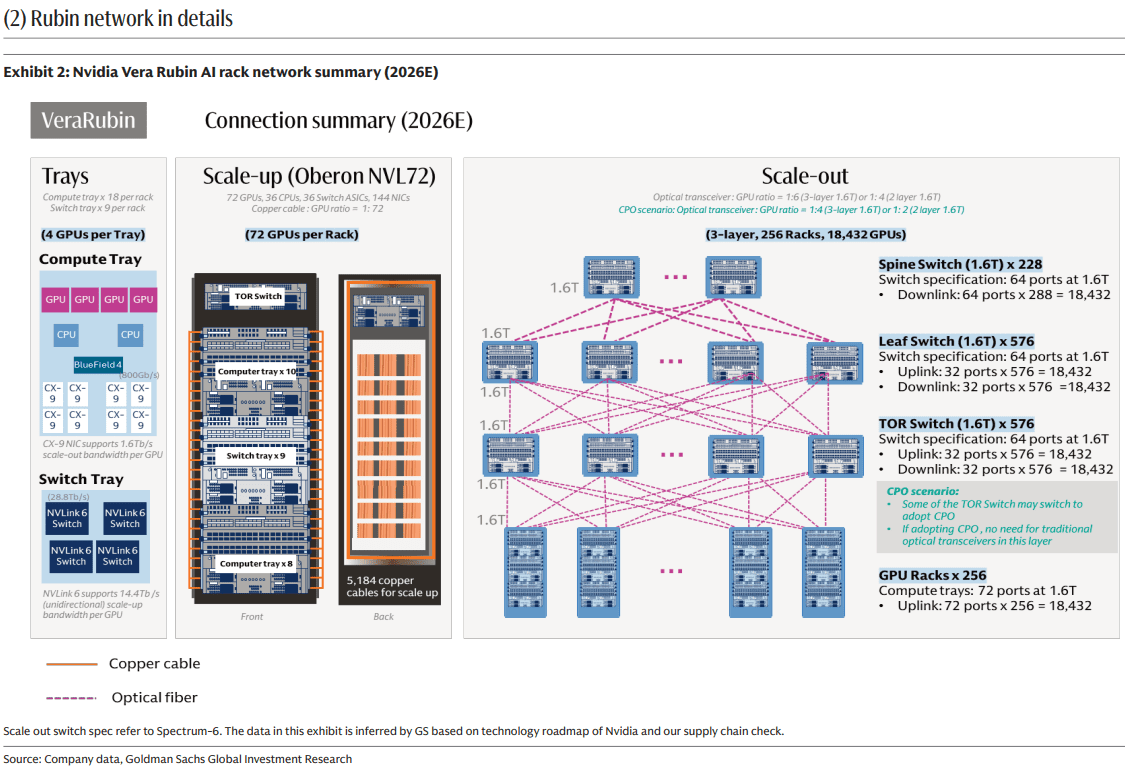
Goldman Sachs report: Optical Networking is the next mega trend in AI infrastructure
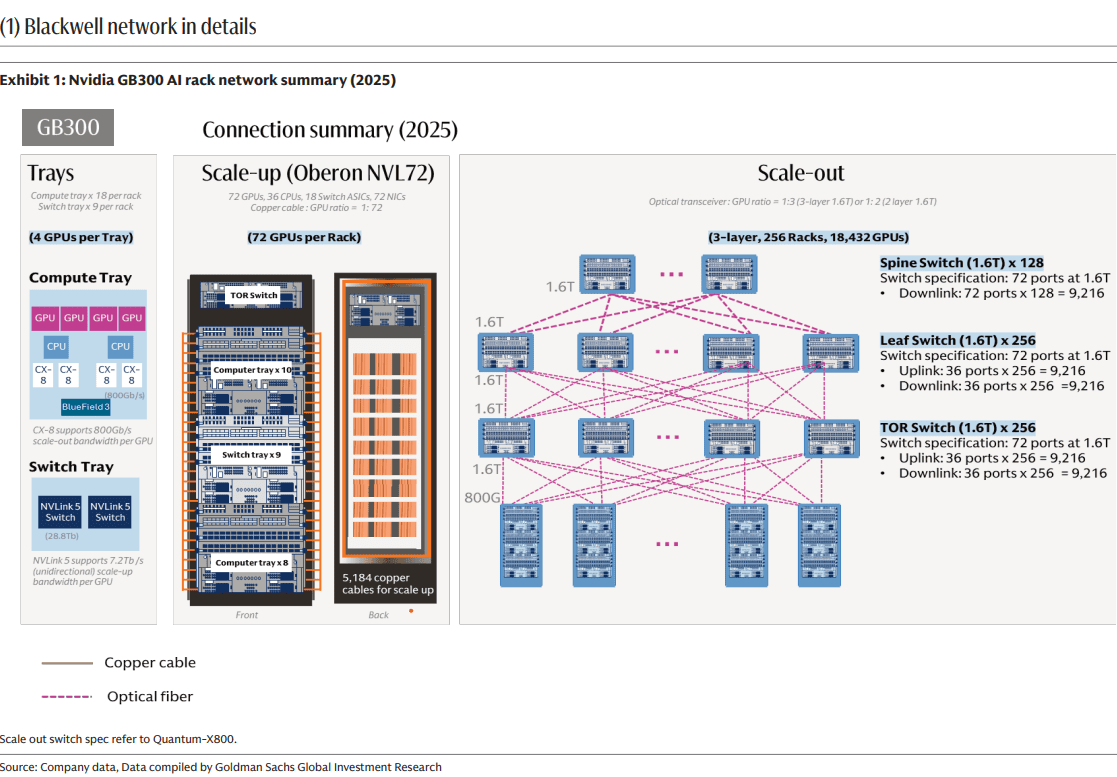
Goldman Sachs analysts forecast a $154billion opportunity in optical networking driven by skyrocketing capacity demands from hyperscale cloud and AI workloads. Carriers and vendors are integrating 10GbE edge networking and AI-RAN (Artificial Intelligence Radio Access Network) trials on live 5G networks.
Goldman argues that AI infrastructure is creating a networking bottleneck phase, where optical interconnects become essential to connect more chips, keep latency low, and let AI clusters scale efficiently. The total optical networking market forecast 9x increase to $154 billion is due to both scale-up and scale-out AI data center architectures grow.
AI compute gains are no longer just about faster GPU and HBM chips; they depend on moving data fast enough between chips, racks, and super-nodes. Goldman Sachs emphasizes that networking now “unlocks computing capability” by enabling seamless exchange across multiple AI chips, which is exactly where copper-based links start to fall short. That makes fiber-optic connectivity, pluggable optics, and co-packaged optics central to the next phase of AI build-out. The report splits opportunity across scale-up and scale-out networking, plus component categories such as copper cables, pluggable optical modules, CPO, and PCB midplanes.
External coverage of this report says Goldman Sachs sees scale-up as the larger pool, about $106 billion or 69% of the $154 billion TAM, while CPO could represent about $91 billion or 59% of the total, assuming 29% penetration in scale-out networking. In practical terms, the report is signaling that the highest-value optical opportunity sits inside tightly coupled AI systems, not just in long-haul or metro transport.
………………………………………………………………………………………………………………………………………………………………………………………….
Goldman projects the following:
- Dollar content increase by 16x / 45x in Scale Out / Scale Up per computing unit from GB300 NVL72 (per computing unit means 72 GPUs per rack to reach NVL72) to Rubin Ultra NVL576 (per computing unit means 72 GPUs per rack, and 8 racks together to reach NVL576), with opportunities across pluggable optical modules, optical engines in CPO, copper cables, and PCB midplanes.
- A 13x larger addressable market for optical modules / optical engines expanding from scale out (e.g. GB300 NVL72) to scale up (e.g. Nvidia Rubin Ultra [1.] NVL576 level 2 scale up via CPO) per computing unit. n
- A 10x larger value market for pluggable optical modules in scale out per computing unit from GB300 NVL72 to Rubin Ultra NVL576, even with a 29% CPO penetration rate. The numbers of pluggable optical module (1.6T equivalent) per computing unit would increase from 216 units in GB300 NVL72 to 2.5k units in Rubin Ultra NVL576.
Note 1. Nvidia Rubin Ultra is a flagship, next-generation AI and high-performance computing (HPC) processor succeeding the standard Rubin architecture. Scheduled to debut in late 2027, it utilizes massive multi-die chiplet designs and unprecedented memory configurations to power the next wave of generative and agentic AI.
………………………………………………………………………………………………………………………………………………………………………….
Market Forecasts:
The investment bank expects the aggregate dollar content per computing unit across scale up and scale out to increase by 29x from US$315k in GB300 NVL72 to US$9.4bn in Rubin Ultra NVL576, and assuming the numbers of racks through the full product cycle are 48k racks for GB300 NVL72, and 16.5k computing units for Rubin Ultra NVL576, the aggregate value TAM across scale up and scale out would increase by 9x from US$15bn in GB300 NVL72 (mainly in 2026) to US$154bn in Rubin Ultra NVL576 (mainly in 2028).
Among the US$154bn value TAM, 69% goes to scale up, or US$106bn, and CPO contributes US$91bn, or 59% of the US$154bn value TAM, assuming CPO at 29% penetration rate in scale out.
For network architects, the important takeaway is that AI clusters are becoming optics-heavy at more layers of the network stack, not just at the edge of the rack. The likely winners are suppliers that can reduce power, improve density, and simplify packaging for very high-bandwidth links, especially around CPO and advanced pluggables. This is less a story about traditional telecom optics and more about datacenter interconnects optimized for GPU fabrics and AI training/inference throughput.
The most consistently cited “top beneficiaries” are Coherent, Lumentum, and Fabrinet. These companies sit close to the core optical component modules and manufacturing layers that scale with higher AI interconnect demand. That makes them the most straightforward proxies for the forecasted optics expansion. The report’s thesis favors companies with strong exposure to high-end optical transport, coherent optics, and data-center interconnect rather than the broader optical networking/PON equipment companies like Ciena, Nokia/Infinera, Cisco/Acacia, ADVA, or Calix.
Conclusions:
Strategically, Goldman Sachs maintains that optical networking is no longer a niche enabling layer; it is becoming a core enabler of AI capex scaling. That shifts investor attention toward optical component vendors, silicon photonics, transceiver suppliers, and adjacent packaging ecosystems. The report’s core message is simple: as AI clusters grow, the network fabric becomes a first-order constraint, and optics are the most likely answer.
References:
2026 Fiber Connect Keynote: “The Future of Fiber Optics: AI and the Quantum”
How will fiber and equipment vendors meet the increased demand for fiber optics in 2026 due to AI data center buildouts?
Big Fiber’s $250M financing deal to buildout dark fiber routes for AI Data Center expansion
Analysis: Fiber Broadband Association (FBA) whitepaper: Upgrading MSO Networks to Fiber to the Home (FTTH): A Technical Perspective
Fiber Optic Boost: Corning and Meta in multiyear $6 billion deal to accelerate U.S data center buildout
Fiber Optic Networks & Subsea Cable Systems as the foundation for AI and Cloud services
AI infrastructure investments drive demand for Ciena’s products including 800G coherent optics
DriveNets and Ciena Complete Joint Testing of 400G ZR/ZR+ optics for Network Cloud Platform
Inside Nokia’s new AI Networking Innovation Lab
- Silicon & Compute: Collaborating with AMD to optimize enterprise AI workloads alongside Nokia data center switches.
- Testing & Infrastructure: Partnering with Keysight Technologies to emulate workloads across Ultra Ethernet Consortium (UEC) and RoCEv2 transports.
- Hardware & Servers: Integrating high-performance platforms from Lenovo and Supermicro.
- Data Storage & Cloud: Working with Weka and cloud builders like Nscale to eliminate storage bottlenecks during heavy computational training.

Nokia’s AI Networking Innovation Lab is built upon three fundamental pillars: Technology Innovation, Ecosystem Collaboration, and Validation. Image credit: Nokia
………………………………………………………………………………………………………………….
Technology Innovation: The lab provides a dedicated space for AI partners to experiment with next-gen solutions across the entire networking stack – driving emerging standards forward with pioneering approaches to new protocols, switching silicon, congestion control, real-time telemetry, and automation.
“Partnering with Nokia in the AI Networking Innovation Lab has enabled us to benchmark and optimize AI networks under real-world conditions…Together, we are helping accelerate AI network adoption by giving operators and hyperscalers the validated insights needed for confident, large-scale deployment.”
Ecosystem Collaboration: True progress depends on a strong ecosystem of technology providers – silicon manufacturers, GPU developers, system, storage and test vendors, and cloud platforms – that work together to create highly-compatible AI-ready solutions. This facilitates joint testing for interoperability, improves integration, and ensures roadmaps are aligned across different hardware, software, and orchestration layers.
Travis Karr, Corporate Vice President, HPC and Sovereign AI at AMD believes customer collaboration and an open ecosystem are fundamental to accelerating AI innovation:
“By co-developing solutions with partners, such as Nokia in their AI networking innovation lab, we ensure our AMD enterprise AI solutions are tested with Nokia data center switches on real-world workloads and network demands. An open, standards-driven approach empowers customers to integrate seamlessly across heterogeneous environments, avoiding lock-in and fostering industry-wide advancement in AI.”
Validation: This positions the lab as the testing ground for Nokia Validated Designs, where customers and partners rigorously validate multi-vendor data center architectures under authentic AI training and inference workloads. By testing failure scenarios, congestion behavior, and operational automation, the lab turns NVDs into proven, deployable solutions — enabling predictable performance, faster deployment, and reduced operational complexity and risk for organizations navigating the AI era.
Arno van Huyssteen, Vice President of Global Telecommunications for Nscale:
“Nokia is a strategic networking partner for Nscale as we build towards AI Grid, and the engineering rigour behind their Validated Designs reflects the kind of innovation needed to enable next-generation AI infrastructure. The depth of hardware, software and failure testing behind those blueprints is what will give operators the confidence to deploy complex AI environments faster, with fewer integration risks and less operational disruption. We’re excited to collaborate in the AI Networking Innovation Lab to help push the boundaries of AI-native networking and validate the next generation of solutions before they reach production.”
A primary focal point inside the lab is managing data center congestion. Unlike traditional cloud traffic, back-end AI networks feature high-density data synchronization across massive GPU clusters. The lab uses advanced automation, AIOps, and lossless Ethernet solutions—such as the Nokia 7220 IXR-H6 switches—to handle these intense uplink and synchronization demands safely.
The AI Networking Innovation Lab supports Nokia’s broader strategy to accelerate the next era of AI-driven connectivity. As demand for AI infrastructure continues to grow, data center networking has become one of the most critical foundations of the global AI ecosystem. Through this investment, Nokia is strengthening its capabilities in AI and cloud infrastructure while advancing its vision of AI-native networking.
Rudy Hoebeke, Vice President of Software Product Management at Nokia:
“The launch of Nokia’s AI Networking Innovation Lab marks a major milestone in our commitment to drive the next era of AI-native connectivity. As the industry continues to evolve with solutions like scale-across and AI-Grid, this lab is poised to accelerate AI networking technology that will not only support but optimize these emerging industry offerings. This center gives our customers and partners early access to new technologies, deeper collaboration with the world’s leading AI ecosystem players, and the confidence that their networks are validated under more realistic AI conditions. By accelerating innovation and reducing deployment risks, we’re enabling the industry to deliver faster, more reliable, and more sustainable AI experiences to people and businesses everywhere.”
………………………………………………………………………………………………………………………
References:
Analysis: Nokia’s strong growth in Optical Networks and AI network infrastructure
Orange, Nokia, Nvidia, and Intel debate: ASICs vs. GPUs vs. General-Purpose CPUs for RAN Baseband Processing
Nokia’s AI Applications Study: “Physical AI” may require RAN redesign to support high‑volume, low‑latency uplink traffic
Australia’s NBN and Nokia demonstrate multi-generation optical technologies concurrently over existing FTTP infrastructure
Nokia to showcase agentic AI network slicing; Ericsson partners with Ookla to measure 5G network slicing performance
Tampnet to expand 5G offshore connectivity in the Gulf of Mexico using Nokia AirScale 5G radios
Dell’Oro: Analysis of the Nokia-NVIDIA-partnership on AI RAN