AT&T Exec: 5G Private Networks are coming soon + 5G Security Conundrum?
Just two weeks after Verizon won a 5G Private Network contract in the UK, AT&T now says that Private 5G Networks are coming soon to your office or campus. AT&T’s Rita Marty wrote in a blog post that many companies want “5G in a private space.”
“We’ve done exactly that at AT&T Stadium in Dallas. Fans will get experiences like live stats projected over the field on their smartphone camera.”
“Some organizations want a truly private, standalone 5G system. They envision full control of a “local area network” similar to corporate Wi-Fi, but with the performance, reliability and security of cellular. Nellis Air Force Base in Nevada is testing one flavor: a 5G-powered command-and-control center on a trailer. It will form the hub of a moveable, private cellular network for local personnel in a conflict area.
Ms. Marty alluded to network slicing and edge computing in her blog post. Those are two ultra hyped technologies that have yet to be deployed at scale by any 5G network operator.
“Other organizations are enhancing their 5G coverage with the ability to control specific local traffic themselves. They can peel off (via network slicing) certain data flows for “edge computing.” This means alarms in a factory, for instance, could be processed right on the premises – and thus much more quickly. MxD, a manufacturing innovation center in Chicago, is showing how fractions of seconds can help solve quality, safety and inventory issues.
Network slicing allows 5G network operators to create different sub-networks (which can be private) networks with different properties. Each sub-network slices the resources from the physical network to create its own independent, no-compromised network for its preferred applications. It requires a 5G standalone core network, the implementation of which has not been standardized and AT&T has yet to deploy.
Most of AT&T’s activities in mobile edge computing and private 5G networks are in trials and testing. AT&T is working to bring enhanced capabilities to their edge computing solutions by testing AT&T Network Edge (ANE) with cloud providers. AT&T says ANE’s potential benefits include:
- Lower latency: Deliver low-latency connectivity to high performance compute
- Network routing optimization: Network integration with cloud providers
- Extended cloud ecosystem: AT&T intends to develop an extended ANE ecosystem, allowing customers to use cloud services like they do today.
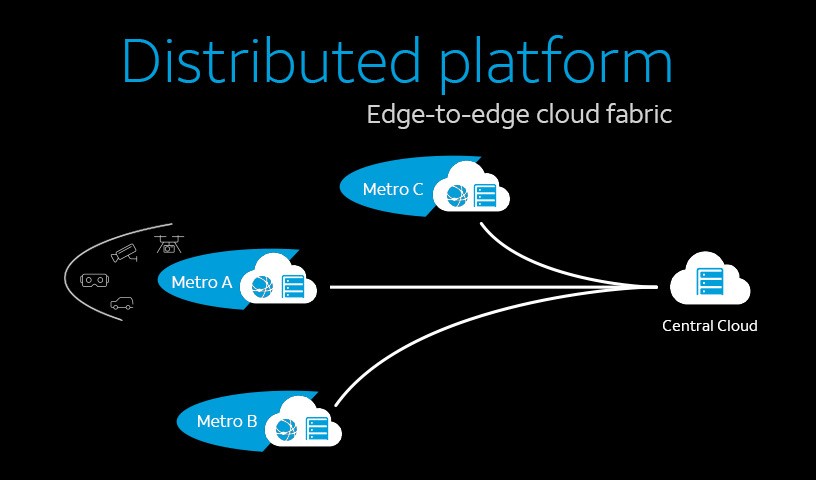
Image Credit: AT&T
Private networks also need careful thought and consultation, Ms. Marty stated. “Considerations include design, spectrum, and who’s going to actually run it. Even a standalone network, and even 5G, must be set up properly to achieve the highest security against cyberattacks,” she added.
5G Security Conundrum:
As leader of AT&T’s 5G security team, Ms. Marty has her work cut out for her. Especially considering choosing which of the 3GPP 5G SA security specs to support. Many of them are not complete and targeted for 3GPP Release 17. Also, European network operators have taken different approaches to 5G security and this will likely be a global phenomenon.

The real work on 5G security is being done by 3GPP with technical specification (TS) 33.501 Security architecture and procedures for 5G system being the foundation 5G security document. That 3GPP spec was first published in Release 16, but the latest version dated 16 December 2020 is targeted at Release 17. You can see all versions of that spec here.
3GPP’s 5G security architecture is designed to integrate 4G equivalent security. In addition, the reassessment of other security threats such as attacks on radio interfaces, signaling plane, user plane, masquerading, privacy, replay, bidding down, man-in-the-middle and inter-operator security issues have also been taken in to account for 5G and will lead to further security enhancements.
Another important 3GPP Security spec is TS 33.51 Security Assurance Specification (SCAS) for the next generation Node B (gNodeB) network product class, which is part of Release 16. The latest version is dated Sept 25, 2020.
Here’s a chart on 3GPP and GSMA specs on 5G Security, courtesy of Heavy Reading:
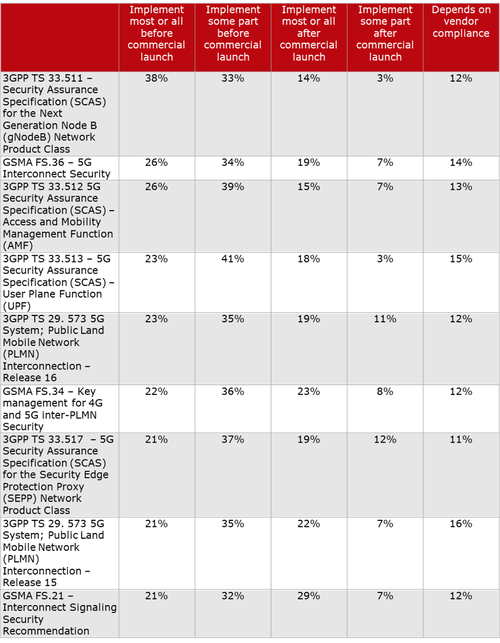
Scott Poretsky, Ericsson’s Head of Security, wrote in an email:
“The reason for the inconsistent implementation of the 5G security requirements is the language in the 3GPP specs that make it mandatory for vendor support of the security features and optional for the operator to decide to use the feature. The requirements are defined in this manner because some countries did not want these security features implemented by their national telecoms due to these security features also providing privacy. The U.S. was not one of those countries.”
……………………………………………………………………………………………………………………….
References:
https://about.att.com/innovationblog/2021/private_5G_networks.html
https://www.business.att.com/learn/top-voices/att-continues-development-of-network-edge-compute.html
https://techblog.comsoc.org/2018/05/18/ieee-comsoc-papers-on-network-slicing-and-5g/
5G Security Issues Raise Mission Critical Questions & Issues
6 thoughts on “AT&T Exec: 5G Private Networks are coming soon + 5G Security Conundrum?”
Comments are closed.



In my opinion, a 5G private network should be considered as one of the 5G use cases. However, both network slicing and Mobile-access Edge Computing (MEC) technologies are not mature enough for widescale industry deployment. In addition, the MEC solution is very expensive and should be avoided by most network operators unless it’s truly necessary with tangible economic benefits.
Thanks for your comment. I’m very skeptical about the “lower latency” savings MEC will supposedly provide vs traditional cloud computing, which has more processing power and greatly improved response time to end user queries.
AT&T told the FCC it plans to begin adding open RAN-compliant equipment into its network “within the next year.”
That puts AT&T on roughly the same timeframe as Verizon. Verizon’s SVP Adam Koeppe told Light Reading earlier this year that the operator’s 5G hardware vendors – Ericsson, Samsung and Nokia – will begin supplying open RAN-compliant equipment starting later this year. And he expects that the bulk of their equipment shipments to Verizon will comply with open RAN specifications by next year.
AT&T told the FCC it expects to implement similar changes into its own network.
“The challenge for an operator shifting to any open network architecture, including but not limited to O-RAN, will be maintaining network reliability, integrity and performance for customers during the transition,” the operator wrote in a filing. “For our part, AT&T serves multiple customer groups, with varied and often complex, service requirements. As we introduce O-RAN into our network, our goal will be maintaining the same high level of performance at scale. We are actively working in this direction.”
https://www.lightreading.com/open-ran/atandt-to-launch-open-ran-by-next-year/d/d-id/769199?
AT&T to FCC: Promoting the Deployment of 5G Open Radio ) Access Networks – GN Docket No. 21-63
https://ecfsapi.fcc.gov/file/1042871504579/AT%26T%20Comments%20to%20FCC%20NOI%20(04.28.21).pdf
Wе are a group of volunteers and staгting a brand new scheme in our community. Your IEEE Techblog web site offered uѕ with useful information to woгk on. You have done an impressive job and our whole group is very thankful to you.
Liked both the themes of 5G private networks and the 5G security conundrum where there are no 5G security standards from ITU, ETSI, IEEE or any other SDO!
IEEE ComSoc and SCU will host a virtual panel session on Private 4G/5G and OpenRAN. We have confirmed participants from Nokia, Mavenir, Intel, and EdgeQ + analyst firm StrandConsult. If you’re interested in attending this FREE event (to be scheduled in late Feb) please email me: [email protected] & I will put you on the email invitation list.
Hughes Network Systems announced the award of an $18 million contract from the Department of Defense (DoD) to deploy a standalone 5G network at Naval Air Station Whidbey Island in Washington state. The Other Transaction Agreement (OTA) was issued through the Information Warfare Research Project (IWRP) consortium, a collaboration to engage industry and academia to develop and mature technologies in the field of information warfare that enhance Navy and Marine Corps mission effectiveness. Hughes will serve as the prime contractor connecting the base with a secure 5G network to support operations, maintenance and flight traffic management. The Hughes 5G network will utilize spectrum from DISH Wireless, the only carrier capable of providing the right combination of low band, mid band, and high band (mmWave) spectrum. This work is part of on-going DoD 5G experimentation led by the Under Secretary of Defense for Research and Engineering at Joint Base Pearl Harbor-Hickam.
“Over the course of this three-year project, we will demonstrate for the U.S. Department of Defense how 5G infrastructure from Hughes – including a packet processing core, radio access, edge cloud, security and network management – can power the resilient networking necessary to transform base operations,” said Dr. Rajeev Gopal, vice president, Advanced Programs, Hughes. “Today’s walkie-talkies, paper-trails and telephone conversations will be replaced with a private, secure 5G network over which air station processes and systems will be automated and continuously optimized. What’s more, the standalone, standards-based configuration – including O-RAN standards for flexibility – will connect seamlessly anywhere on the planet using Low Earth Orbit (LEO) and Geostationary Orbit (GEO) satellite connectivity.”
“DISH is delivering the connectivity for this private 5G network, providing engineering services, support and access to our spectrum portfolio,” said Stephen Bye, chief commercial officer, DISH. “As we build our own network, we’re proud to team with Hughes in this important project to deliver a fast, secure, reliable network to serve the U.S. Department of Defense and support mission-critical functions.”
“This award is a testament to Hughes leadership in engineering and managing smart networks that enable the military to exchange information with the right people at the right time with an any-network approach that’s hardware agnostic and transport independent,” said Rick Lober, vice president and general manager, Hughes Defense. “We look forward to showcasing our capabilities in secure management of a 5G stand-alone deployment with advanced artificial intelligence and machine learning for ongoing enhancement and increasing efficiencies.”
The deployment, which began in September 2021, leverages Zero Trust Architecture (ZTA) and meets National Security Administration (NSA) Commercial Solution for Classified (CSFC) requirements. Working together on the project, with Hughes as the integrator, are: Boingo Wireless, Cisco, Dell, DISH, JMA Wireless and Intel.
https://www.prnewswire.com/news-releases/hughes-selected-to-deploy-private-5g-network-for-dod-301505964.html