5G Network Slicing
Nokia to showcase agentic AI network slicing; Ericsson partners with Ookla to measure 5G network slicing performance
Executive Summary:
Today, Nokia announced a strategic collaboration with Amazon (AWS), Du, and Orange to debut an industry-first agentic AI-driven network slicing [1.] capability on a 5G SA core network. Du and Orange will deploy this new technology which uses Nokia’s 5G AirScale base stations, MantaRay SMO and Agentic AI modules in tandem with Amazon’s Bedrock Artificial Intelligence platform. Autonomous AI agents are used to ingest and process real-time telemetry—including geospatial data, event triggers, and traffic patterns—the framework enables adaptive network slicing. This architecture allows communications service providers (CSPs) to dynamically orchestrate resources in response to fluctuating demand, such as prioritizing mission-critical throughput for first responders during emergency incidents.
Note 1. There are no ITU standards for network slicing or the 5G SA Core network required to implement that capability. 3GPP specifications define end-to-end network slicing architecture, covering slice management (TS 28.552, TS 28.554), service requirements, and security (NSSAA – Network Slice Specific Authentication and Authorization). The NSA and CISA have released specific, recognized guidance on designing, deploying, and maintaining secure 5G standalone (SA) network slices. ETSI publishes and adopts 3GPP technical specifications (specifically the 28-series) as European standards for network slicing management, including 5G RAN, core network, and NFV-MANO architecture. ETSI, as a 3GPP partner, ensures these specifications cover the lifecycle of network slices.
…………………………………………………………………………………………………………………………………………………………………………………………..
- Data Ingestion & Inference: Agentic AI modules, hosted on Amazon Bedrock, ingest real-world contextual data (e.g., emergency alerts, traffic sensors, weather) alongside live network KPIs.
- Intent-Based Policy Generation: The AI agents analyze this telemetry to determine the optimal network configuration required to meet specific Service Level Agreements (SLAs) or emergency “intents'”
- NEF & SMO Integration: These high-level intents are translated into actionable policies and pushed to Nokia’s MantaRay SMO (Service Management and Orchestration).
- Dynamic RAN/Core Adjustment: The Network Exposure Function (NEF) acts as the secure gateway, allowing the AI agents to interface with the 5G Core. It exposes network capabilities so the agents can dynamically adjust RAN policies and resource allocation across the 5G AirScale base stations.
- Autonomous Feedback Loop: The system operates in an autonomous mode where agents continuously monitor the results of their adjustments, performing forensic analysis to refine slicing parameters in real-time.
Nokia will host live technical demonstrations of this AI network slicing capability at its 2026 Mobile World Congress (MWC) Barcelona exhibit.

Quotes:
“This innovation marks a major milestone in the evolution of AI-native networks,” said Pallavi Mahajan, Chief Technology and AI Officer at Nokia. “By combining Nokia’s advanced network slicing capabilities with agentic AI, we are enabling operators to deliver premium, intent-based services that adapt dynamically to real-world conditions. Nokia is advancing connectivity by unlocking new value streams for telecommunication providers and supporting next-generation applications and differentiated services for enterprises, industries and consumers.”
Amir Rao, Global Director, GTM & Telco Solutions at AWS added: “Network slicing has long promised to unlock new revenue streams for operators, but manual configuration and static policies have prevented end customers from accessing on-demand provisioning. By integrating agentic AI capabilities through Amazon Bedrock with Nokia’s application, operators can now deliver intelligent, context-aware network slicing that responds dynamically to real-world conditions from traffic surges to emergency situations. This transforms network slicing from a technical capability into a true business enabler, allowing operators to monetize their 5G investments through differentiated, premium services that adapt automatically to customer needs. Agentic Network Slicing is the beginning of an era that will enable telecommunications providers to enable real-time intent-based service provisioning for end customers.”
………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………..
Competitive Network Slicing Solution:
Rival wireless equipment vendor Ericsson yesterday gave a preview of a network slicing related offering which it will be demonstrating at the 2026 MWC. Together with Ookla it has developed a specialized test version of its Speedtest app designed to measure and validate 5G network slicing performance. The tool enables the Speedtest app to identify and test specific network slices, which apparently demonstrates how Service Level Agreements (SLAs) for differentiated services can be verified in real-time by consumers and service providers.
Ericsson reported in its latest Mobility report that there were 65 commercial network slicing services worldwide providing so-called “differentiated connectivity” offerings. That’s out of a total of 118 network slicing cases discovered by Ericsson’s researchers. Yet in the UK, none of the three mobile network operators have launched a commercial 5G network slicing capability yet. According to Ofcom’s latest Connected Nations report, 5G SA is available across 83% of outside areas in the country and 5G SA accounts for nearly one-third of 5G traffic. However, 4G accounts for 72% of total monthly data traffic.
“Network slicing is no longer a future concept; it is a commercial reality. However, you cannot manage what you cannot measure,” said Tibor Rathonyi, Senior Advisor at Ookla. “Our work with Ericsson is a pivotal first step in providing the transparency needed to prove the value of these premium 5G services to both consumers and enterprises.”
Philipp Bichsel, Executive Vice President Mobile Network & Services at Swisscom, said: “Swisscom has retained the title as the country’s best-performing mobile network over many years by truly prioritizing the delivery of the best possible customer experience. This has meant embarking on a journey to fully exploit automation to enhance reliability and efficiency without compromising the service quality our customers expect. As we advance towards self-learning, autonomous networks, enabling Swisscom to build smarter and more adaptive network operations, we are leveraging the SMO framework as the foundation for this evolution. Within this framework, partner solutions such as Ericsson’s Intelligent Automation Platform and its ecosystem of rApps play an important role in helping us explore the potential of AI driven automation.”
…………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………..
References:
https://www.telecoms.com/5g-6g/nokia-and-aws-show-off-agentic-ai-powered-5g-advanced-network-slicing
https://www.telecoms.com/5g-6g/ericsson-and-ookla-launch-network-slicing-measurement-tool
https://www.lightreading.com/5g/eurobites-network-slicing-enjoying-a-moment-finds-ericsson-report
https://www.ericsson.com/en/reports-and-papers/mobility-report/reports/november-2025
https://www.lightreading.com/5g/5g-network-slicing-not-ready-for-prime-time-in-uk
https://www.awardsolutions.com/portal/resources/network-slicing
ABI Research: 5G network slicing market to hit $67.52 billion in 2030 with Asia Pacific in the lead
5G network slicing progress report with a look ahead to 2025
FCC Draft Net Neutrality Order reclassifies broadband access; leaves 5G network slicing unresolved
Telstra achieves 340 Mbps uplink over 5G SA; Deploys dynamic network slicing from Ericsson
ABI Research: 5G Network Slicing Market Slows; T-Mobile says “it’s time to unleash Network Slicing”
Ericsson, Intel and Microsoft demo 5G network slicing on a Windows laptop in Sweden
Ericsson and Nokia demonstrate 5G Network Slicing on Google Pixel 6 Pro phones running Android 13 mobile OS
Nokia and Safaricom complete Africa’s first Fixed Wireless Access (FWA) 5G network slicing trial
Is 5G network slicing dead before arrival? Replaced by private 5G?
5G Network Slicing Tutorial + Ericsson releases 5G RAN slicing software
ABI Research: 5G network slicing market to hit $67.52 billion in 2030 with Asia Pacific in the lead
ABI Research forecasts that the global 5G network slicing market will surge from $6.1 billion in 2025 to $67.52 billion by 2030, reflecting a compound annual growth rate (CAGR) of 70%. This represents a sharp upward revision from its 2023 outlook, which projected a market value of $19.5 billion by 2028.
Editor’s Note: 5G network slicing, as well as ALL 5G features and functions (including 5G Security) require a 5G Standalone (SA) core network, which up until recently had not been widely deployed. Also, there are no ITU standards or recommendations for either 5G SA or 5G network slicing or any other 5G features/functions. Those are all specified by 3GPP, for example TS 23.501 5G Systems Architecture which includes network slicing.
In a recent blog post, Dimitris Mavrakis stated that the ABI’s revised forecast is driven by intensified monetization efforts from major network operators, including China Mobile, Deutsche Telekom and T-Mobile US, together with the growing installed base of 5G Standalone (SA)-capable smartphones. At the same time, he highlighted that progress is moderated by the proven complexity of integrating 5G SA cores and cloud-native tooling into existing telco network and IT environments.

ABI indicates that so-called “carpeted” industry verticals—like retail, stadiums, and financial services do not deal with mission- and safety-critical applications. Therefore, slicing deployments are more simplistic and provide a quicker Return on Investment (ROI) than in more demanding industry sectors such as oil and gas. ABI says that industrial manufacturing will remain an important vertical for network slicing, albeit at a substantially slower growth rate than carpeted verticals.
The analysis further suggests that, for certain enterprises, network slicing delivered over public 5G infrastructure is becoming a more attractive option than 5G private networks, which introduces additional headwinds for the private networking market. While B2B use cases are expected to account for 64% of total network slicing market value by 2030, consumer applications are projected to be the single largest segment, contributing approximately $24.3 billion of revenue by the end of the period.
5G network slicing progress report with a look ahead to 2025
ABI Research: 5G Network Slicing Market Slows; T-Mobile says “it’s time to unleash Network Slicing”
Ericsson, Intel and Microsoft demo 5G network slicing on a Windows laptop in Sweden
Ericsson and Nokia demonstrate 5G Network Slicing on Google Pixel 6 Pro phones running Android 13 mobile OS
BT Group, Ericsson and Qualcomm demo network slicing on 5G SA core network in UK
Telstra achieves 340 Mbps uplink over 5G SA; Deploys dynamic network slicing from Ericsson
Samsung and KDDI complete SLA network slicing field trial on 5G SA network in Japan
Is 5G network slicing dead before arrival? Replaced by private 5G?
5G Network Slicing Tutorial + Ericsson releases 5G RAN slicing software
Network Slicing and 5G: Why it’s important, ITU-T SG 13 work, related IEEE ComSoc paper abstracts/overviews
Dell’Oro: RAN market stable, Mobile Core Network market +14% Y/Y with 72 5G SA core networks deployed
Téral Research: 5G SA core network deployments accelerate after a very slow start
Building and Operating a Cloud Native 5G SA Core Network
Highlights of Ericsson’s Mobility Report – November 2025
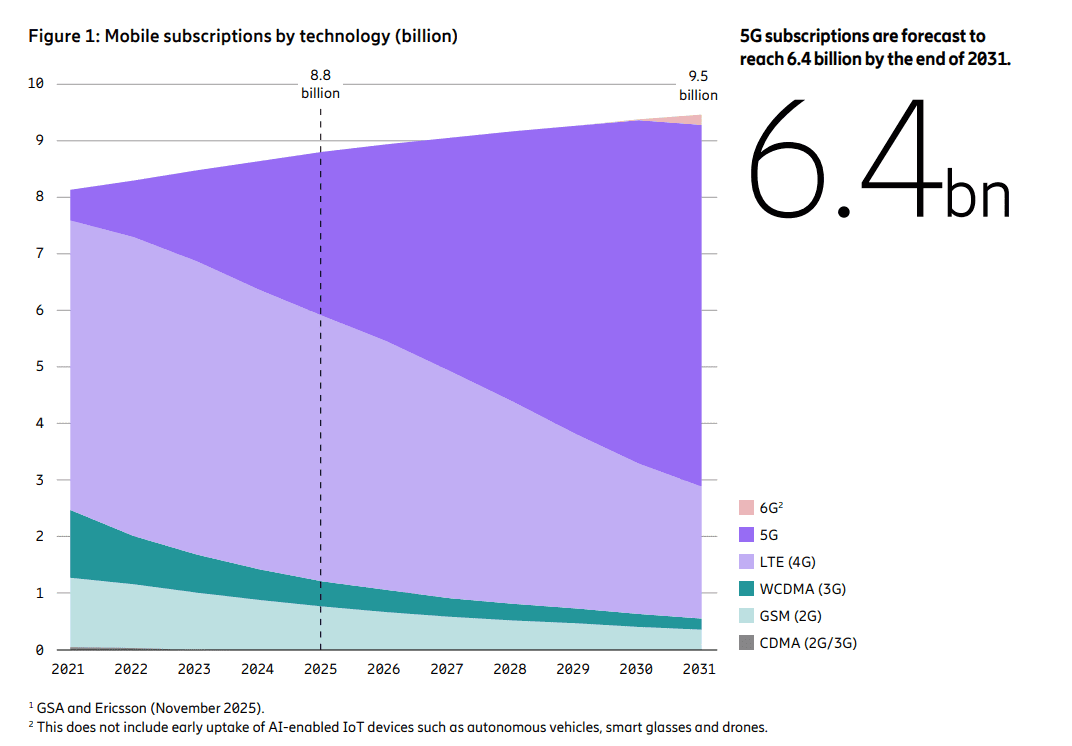
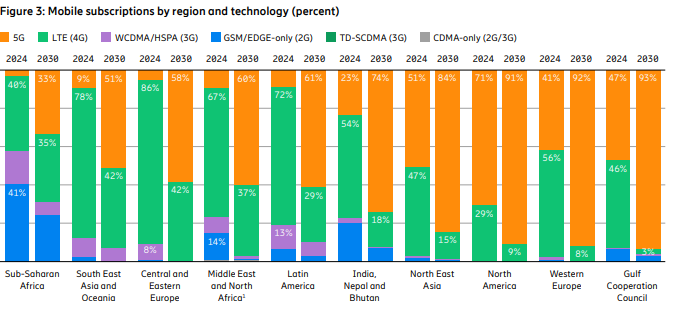
The latest issue of the Ericsson Mobility Report states that 5G subscriptions now account for one-third of total mobile subscriptions. Mobile network data traffic grew slightly more than expected – 20 percent between Q3 2024 and Q3 2025. As 5G evolves, service providers are increasingly exploring innovative use cases and new monetization opportunities such as offering differentiated connectivity services and modernizing enterprise IT with 5G.
After many years of hype, network slicing, which requires a 5G SA core network, is finally gaining market traction with 33 communications service providers now offering variations of the technology. Of the 118 network slicing cases discovered by Ericsson’s researchers, 65 have moved beyond proof of concept and into commercial services, either as standalone subscription services or as add-on packages for consumer or business customers. Ericsson attributes this growth spurt to more widespread deployment of 5G SA core networks.
Looking further ahead, the 6G RAN standardization process has begun in 3GPP and ITU-R WP5D, with the first commercial launches expected in front-runner markets.
–>However, there has been no work initiated on the 6G core network in either 3GPP or ItU-T.
Ericsson’s report says the U.S., Japan, South Korea, China, India and some Gulf Cooperation Council countries are the 6G leaders. Global 6G subscriptions are likely to reach 180 million by the end of 2031, the report predicts.
We think that forecast is highly unlikely as the IMT 2030 (6G) RIT/SRITs recommendation won’t be completed till the end of 2030 with initial deployments sometime in 2031.
…………………………………………………………………………………………………………….
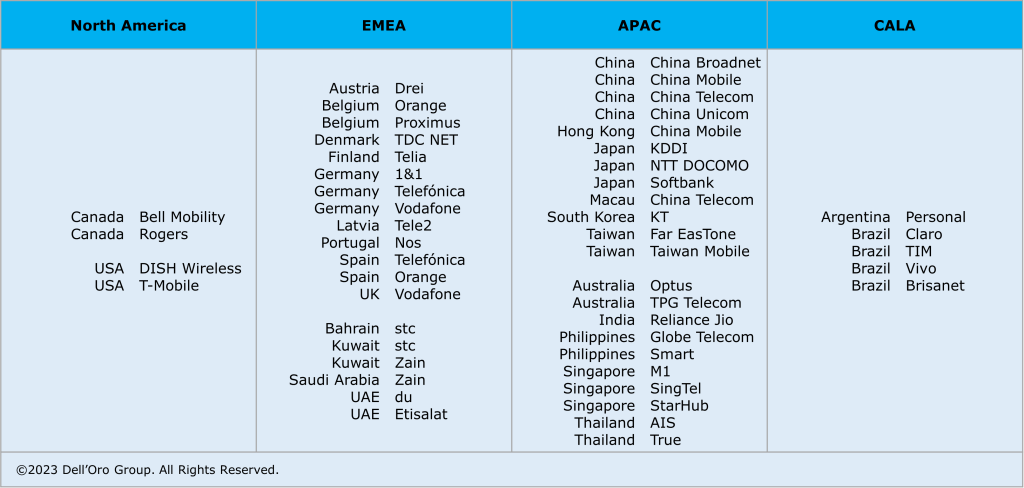
Data from Omdia, a Light Reading sister company, shows Ericsson, Huawei and Nokia were even more dominant last year than they were in 2023, growing their combined market share by 2.3 percentage points over this period, to 77.4%. Besides China’s ZTE, the only other contender with more than a percentage point of market share was Samsung.
References:
https://www.ericsson.com/en/reports-and-papers/mobility-report/reports/november-2025
Dell’Oro: 4G and 5G FWA revenue grew 7% in 2024; MRFR: FWA worth $182.27B by 2032
Ericsson’s revenue drops, profits soar; deal with Vodafone and partnership with Export Development Canada look promising
Latest Ericsson Mobility Report talks up 5G SA networks and FWA
Ericsson Mobility Report touts “5G SA opportunities”
Ericsson Mobility Report: 5G monetization depends on network performance
Ericsson Mobility Report: 5G subscriptions in Q2 2022 are 690 million (vs. 8.3 billion total mobile users)
Google Fiber and Nokia demo network slicing for home broadband in GFiber Labs
Network slicing has previously been restricted to 5G Stand Alone (SA) networks, which the IEEE Techblog regularly covers (see References below). However, network slicing software may also have a place in the home broadband network, as per a demo from Google Fiber and Nokia. Google Fiber says that this use of “network slicing gives us the ability to carve up a customer’s home network into different “lanes,” each optimized for a specific use.” In a GFiber Labs demo, gaming was used as the test scenario.
Google Fiber placed two gaming consoles next to each other and simulated network congestion, which drove the game’s latency up to 90 milliseconds. Unsurprisingly, “it was stalling, pixelating…a really ill experience for the end user,” said Nick Saporito, Google Fiber’s head of product. “This was a foundational test and it worked,” he added.

In the long-term, this could truly change how home internet works, especially when it’s driven by the customer. Today’s one-size-fits-all connections treat all traffic the same. But we know not everyone uses the internet the same way: gamers care about latency, remote workers need video stability, home businesses rely on solid uptime and security, and, we can see a future where applications (AI, VR, etc.) may require next-level performance. Network slicing could be how we level up network performance.
Network slicing opens the door to something new: the ability for customers to tailor their connection to the categories of Internet use that matter most in their home. It’s not about prioritizing traffic behind the scenes, it’s about giving you more control, more flexibility, and more ways to get the performance you need, when you need it. And with GFiber, it will always be in service of giving customers more control, without compromising our commitment to an open, unrestricted internet.
There’s also potential for something called “transactional slices.” These would spin up automatically, just for a few seconds, to keep things like financial logins secure. For example, connecting you directly to a service like your bank without routing traffic across the broader internet. You wouldn’t even notice it happening, but it could add meaningful peace of mind.
Network slicing is the next logical step in how we think about GFiber service — especially our lifestyle products like Core, Home, and Edge, built to meet the needs of customers’ unique internet lifestyles. Those products are designed to better match the way people live and work. Network slicing takes that a step further: adding real-time customization and control at the network level.
While we’re very excited about the possibilities here, there are few things that have to happen before we roll out network slicing across our network. Automation is a key piece of the puzzle. We’ll be diving deeper with Nokia later this year to explore how we can bring some of these ideas to life. This kind of innovation is exactly what GFiber Labs was built for and we’re excited about potentially leveling up the GFiber customer experience — again.
When considering how to implement network slicing on a wider scale, Saporito noted two key challenges. First, “a lot” of network automation is required to ensure a seamless experience. Google Fiber currently has a “mini-app” that lives on the router to help on the automation front, so that a technician doesn’t have to log onto the router and manually configure the settings.
Another challenge is determining how to effectively sell network slicing capabilities to customers. Given how prevalent multi-gig internet has become, Google Fiber is thinking about whether it makes sense to give customers more “ISP-like controls over their pipe,” Saporito said, rather than just providing a one-size-fits-all product.
“Much like you can put your car in sport or comfort mode, maybe our customers could go to the GFiber app and put their internet in gaming mode, for example, and then all their gaming traffic is special handled by network slicing,” he explained. “Those are ways that we’re kind of thinking about how we would productize it.”
But widespread adoption of broadband network slicing is still a ways away, according to Dell’Oro Group VP Jeff Heynen, as most ISPs and equipment providers are still in the proof-of-concept phase. “That being said, if you look down the road and you don’t expect downstream bandwidth consumption to grow as quickly as it historically has, then network slicing could be a way to help ISPs charge more for their service or, less likely, charge for specific slices,” Heynen said.
Aside from improving gaming or AI applications, one interesting use case for slicing is to provide additional security around financial transactions, Heynen noted. An operator could create a slice on a “per-transaction basis,” complementing a more standard encryption method like SSL.
“You could imagine an ISP differentiating themselves from their competition by highlighting that they have the most secure broadband network, for example,” he added. Saporito similarly noted the value of a so-called “transactional slice.” Though Google Fiber has yet to demo the concept, the idea is to create a temporary slice that would work when a customer logs onto their bank account. “We could create an automatic slice in the background to where that banking traffic is going directly to the financial institution’s back-end, versus traversing the transport network,” he said. “The customer wouldn’t even really notice it.”
https://fiber.google.com/blog/2025/06/network-slicing-demo.html
https://www.fierce-network.com/broadband/google-fiber-puts-nokia-network-slicing-technology-test
Téral Research: 5G SA core network deployments accelerate after a very slow start
5G network slicing progress report with a look ahead to 2025
ABI Research: 5G Network Slicing Market Slows; T-Mobile says “it’s time to unleash Network Slicing”
Is 5G network slicing dead before arrival? Replaced by private 5G?
5G Network Slicing Tutorial + Ericsson releases 5G RAN slicing software
5G network slicing progress report with a look ahead to 2025
The “true” version of 5G is 5G standalone (SA), which eliminates the need for a 4G anchor network and supports all 3GPP defined 5G functions, like 5G Security, Voice over 5G New Radio (VoNR) and network slicing. As we’ve noted for years, 5G SA has proven difficult to deploy, partially because there are no standards for implementation – only 3GPP 5G Architecture specs (rubber stamped as ETSI standards, but never submitted to the ITU for consideration as one or more ITU-T recommendations).
Network slicing is only possible with a 5G SA core network. Operators which have deployd 5G SA are using and planning to use 5G network slices for a variety of use cases, including: a priority slice for first responders, support financial or mission-critical applications, or offer broadcasters a dedicated fast 5G layer to transfer video from cameras to production teams at sporting or other live events.

Image Credit: SDx Central
……………………………………………………………………………………………………………….
In the U.S., T-Mobile is the only major carrier offering 5G SA and has been moving forward with network slicing deployments. Verizon said recently that its 5G network slicing public safety field demonstration in Phoenix, Arizona, is operational but still in trials. AT&T has tested prioritized access to its network, but so far has not yet provided a 5G SA network to support network slicing . That’s despite outsourcing development to Microsoft Azure cloud platform in June 2021.
T-Mobile recently launched “T-Priority,” a network slice for first responders supported by the network operator’s 5G SA core network. The wireless telco told regulators at the end of 2023:
“Network slicing involves creating customized, software-defined, virtual networks – or ‘slices’ – that are each logically separated and individually optimized to meet the specific needs of each application. Within a slice, network functions are defined in software and customized to the use case supported by that slice. For example, network slicing allows providers to use a single 5G network to deliver high-intensity network resources to support a small number of robots on a factory floor, while at the same time delivering low-intensity network resources to a very large number of meter-reading sensors on a utility network.”
Overseas, BT, Orange Belgium, Singtel, China Telecom, Reliance Jio, and Telia Finland have deployed network slicing, among other 5G carriers. Singtel’s app-based network slicing is designed to improve the performance of consumer and enterprise applications.
Nokia recently said it tested a network slicing application with network operator Liberty Global and Belgian shipping company Seafar. Nokia said the shipping company could use its API platform to purchase an ultra-low latency slice of Liberty Global’s Telenet 5G standalone network to maneuver Seafar’s ships through ports without having to slow down.
“Slicing will be critical to enabling enterprise cases and providing network solutions for many use cases for which a stand-alone purpose-built network is not feasible,” Nokia stated in a February meeting between CEO Pekka Lundmark and a variety of top FCC officials, including FCC Chairwoman Jessica Rosenworcel.
The GSMA, which is NOT a standards development organization, launched its “Open Gateway” campaign last year. Earlier this year the group said that 47 mobile operators representing 239 mobile networks and 65% of wireless connections around the world have signed up. Currently, GSMA and its partners are developing a wide range of APIs for text messaging, location information, billing, quality of service – and network slicing among other applications.
Several analysts believe that network slicing will see more growth next year:
“There will be definitely more rollouts of network slicing capabilities as 5G SA networks mature, and as 5G NSA networks move to SA in the next few years,” AvidThink principal analyst Roy Chua said in an email. “Using a network slice for privacy/security/isolation or for ensuring QoS (live broadcasts, sporting events, emergency and disaster support) will likely continue.”
Lead analyst at Techsponential Avi Greengart agreed that more network slicing deployments will happen in the coming year as more operators upgrade to 5G SA. “Network slicing has been a long-touted feature of 5G, and we’re starting to see it used for large venues (ex: sports stadiums) and public safety,” he told Fierce Network. Greengart warned that slicing is not a panacea for private networks or Wi-Fi.
“I do think that network slicing will be operator specific,” noted neXt Curve executive analyst Leonard Lee. “There is still the open question of what the generally monetizable services will be and the scenarios that make them viable. This, each operator will be answering for themselves on their own timeline. For outside observers, it will be like watching a kettle boil,” he said, adding a note of caution.
References:
https://www.lightreading.com/network-automation/2025-preview-network-slicing-gets-real
https://www.fierce-network.com/wireless/network-slicing-slides-more-vigorously-2025
https://www.sdxcentral.com/5g/definitions/key-elements-5g-network/5g-network-slicing/
FCC Draft Net Neutrality Order reclassifies broadband access; leaves 5G network slicing unresolved
ABI Research: 5G Network Slicing Market Slows; T-Mobile says “it’s time to unleash Network Slicing”
Telstra achieves 340 Mbps uplink over 5G SA; Deploys dynamic network slicing from Ericsson
Ericsson, Intel and Microsoft demo 5G network slicing on a Windows laptop in Sweden
Is 5G network slicing dead before arrival? Replaced by private 5G?
5G Network Slicing Tutorial + Ericsson releases 5G RAN slicing software
Latest Ericsson Mobility Report talks up 5G SA networks and FWA
Ericsson’s November 2024 Mobility Report predicts that global 5G standalone (SA) connections will top 3.6 billion by 2030. That compares to 890 million at the end of 2023. Over that same period of time, 5G SA as a proportion of global mobile subscriptions is expected to increase from 10.5% to 38.4%, while average monthly smartphone data consumption will grow to 40 GB from 17.2 GB. By the end of the decade, 80% of total mobile data traffic will be carried by 5G networks.
That rosy forecast is in sharp contrast to the extremely slow and disappointing pace of 5G SA deployments to date. In January, Dell’Oro counted only 12 new 5G SA deployments in 2023, compared to the 18 in 2022. “The biggest surprise for 2023 was the lack of 5G SA deployments by AT&T, Verizon, British Telecom EE, Deutsche Telekom, and other Mobile Network Operators (MNOs) around the globe. As we’ve stated for years, 5G SA is required to realize 5G features like security, network slicing, and MEC to name a few.”
Fifty 5G Standalone enhanced Mobile Broadband (eMBB) networks commercially deployed (2020 – 2023):
The report states, “Although 5G population coverage is growing worldwide, 5G mid-band is only deployed in around 30% of all sites globally outside of mainland China. Further densification is required to harness the full potential of 5G.” Among the report highlights:
- Global 5G subscriptions will reach around 6.3 billion in 2030, equaling 67% of total mobile subscriptions.
- 5G subscriptions will overtake 4G subs in 2027.
- 5G is expected to carry 80% of total mobile data traffic by the end of 2030.
- 5G SA subscriptions are projected to reach around 3.6 billion in 2030.
Source: Ericsson Mobility Report -Nov 2024
“Service differentiation and performance-based opportunities are crucial as our industry evolves,” said Fredrik Jejdling, EVP and head of Ericsson’s networks division. “The shift towards high-performing programmable networks, enabled by openness and cloud, will empower service providers to offer and charge for services based on the value delivered, not merely data volume,” he added.
The Mobility Report provides two case studies in T-Mobile US and Finland’s Elisa – both of which have rolled out network slicing on their 5G SA networks and co-authored that section of the report:
- T-Mobile has been testing a high priority network slice to carry mission-critical data during special events.
- Elisa has configured a slice to support stable, high-capacity throughput for users of its premium fixed-wireless access (FWA) service, called Omakaista.
The Mobility Report doesn’t say if those two telcos are deriving any monetary benefit from network slicing, or more broadly from their 5G SA networks.
……………………………………………………………………………………………………………………………………………………………………………………………………………..
The Fixed Wireless Access (FWA) market has momentum:
- Ericsson predicts FWA connections will reach 159 million this year, up from 131 million in 2023.
- By 2030, connections are expected to hit 350 million, with 80% carried by 5G networks.
- In four out of six regions, 83% or more wireless telcos now offer FWA.
- The number of FWA service providers offering speed-based tariff plans – with downlink and uplink data parameters similar to cable or fiber offerings – has increased from 30% to 43% in the last year alone.
- An updated Ericsson study of retail packages offered by mobile service providers reveals that 79% have a FWA offering.
- There are 131 service providers offering FWA services over 5G, representing 54 percent of all FWA service providers.
- In the past 12 months, Europe has accounted for 73%of all new 5G FWA launches globally.
- Currently, 94% of service providers in the Gulf Cooperation Council region offer 5G FWA services.
- In the U.S. two service providers (T-Mobile US and Verizon) originally set a goal to achieve a combined 11–13 million 5G FWA connections by 2025. After reaching this target ahead of schedule, they have now revised their goal to 20–21 million connections by 2028.
- The market in India is rapidly accelerating, with 5G FWA connections reaching nearly 3 million in just over a year since launch. • An increasing number of service providers are launching FWA based on 5G standalone (SA).
References:
https://www.ericsson.com/en/reports-and-papers/mobility-report/reports/november-2024
https://www.ericsson.com/4ad0df/assets/local/reports-papers/mobility-report/documents/2024/ericsson-mobility-report-november-2024.pdf
5G Advanced offers opportunities for new revenue streams; 3GPP specs for 5G FWA?
FWA a bright spot in otherwise gloomy Internet access market
Where Have You Gone 5G? Midband spectrum, FWA, 2024 decline in CAPEX and RAN revenue
GSA: More 5G SA devices, but commercial 5G SA deployments lag
Vodafone UK report touts benefits of 5G SA for Small Biz; cover for proposed merger with Three UK?
Building and Operating a Cloud Native 5G SA Core Network
How Network Repository Function Plays a Critical Role in Cloud Native 5G SA Network
NRF (Network Repository Function) facilitates cloud-native 5G networks by enabling dynamic and efficient discovery of peer Network Functions, enhancing scalability.
Ajay Lotan Thakur
Introduction:
DNS (Domain Name Service) has been widely used by networks to discover 3G and 4G Network Functions (NFs). Every time there is a change in the network, this entails adding or updating records in the DNS server. This solution was not cohesive. The 5G Network Repository Function (NRF), which was introduced in the 5G specification, addresses this issue. Every Network Function needs to register its profile with NRF when it’s ready to service the APIs. Every NF type contains unique information in the NF profile. For example, Session Management Function (SMF) might provide the set of Data Network Names (DNN) it serves.
It’s important to note is that SMF may still choose User Plane Function (UPF) using proprietary logic because the UPF interface to NRF is still optional. In this article we shall see various advantages provided by 3GPP’s NRF network function over traditional 3G/4G networks.
Advantages of 5G NRFs:
Using 5G Network Resource Function (NRF) for discovering peer Network Functions (NFs) compared to relying on DNS servers in 4G networks brings several advantages:
- Efficiency in Resource Discovery: NRF offers a more efficient and dynamic way of discovering peer NFs within the network. Unlike DNS servers, which rely on static records and hierarchical lookup mechanisms, NRF enables direct discovery of available NFs, reducing latency and enhancing resource utilization. NRF can search the NFs based on many parameters like load, slice Ids, DNN name etc.
- Enhanced Security: NRF can incorporate security features such as authentication and authorization mechanisms, ensuring that only authorized NFs can be discovered and accessed. This helps in mitigating security threats such as DNS spoofing or cache poisoning, which are concerns in traditional DNS-based architectures.
- Support for Network Slicing: NRF is well-suited for 5G network slicing, where multiple virtualized networks coexist on the same physical infrastructure. It allows for efficient discovery and allocation of NFs specific to each network slice, enabling tailored services and resource optimization.
- Service Orchestration: NRF facilitates service orchestration by providing real-time information about the available NFs and their capabilities. This enables dynamic service composition and adaptation based on changing network conditions and application requirements. NRF can be used to put some of the NFs under maintenance mode as well.
- Low Latency: With NRF, the latency in discovering and connecting to peer NFs is significantly reduced compared to DNS-based approaches. This is crucial for applications requiring real-time communication or low-latency services, such as edge computing or autonomous vehicles. In case NRF is overloaded then it can scale-out to bring down the latency.
- Scalability: NRF architecture is designed to handle the scalability demands of 5G networks, where the number of NF instances and their dynamic nature can be high. It allows for efficient scaling of network resources without relying on centralized DNS servers, which may face scalability challenges under heavy loads. This allows Network Functions to implement dynamic scale in & scale out without touching any DNS servers.
- Dynamic Network Updates: NRF supports dynamic updates of network information, allowing for real-time changes in the availability and status of NF instances. These are NRF notifications supported as per 3gpp specification. In contrast, DNS records may require time to propagate changes across the network, leading to potential inconsistencies or delays in service discovery. Each NF can update its profile as and when it sees changes.
Conclusions:
Overall, leveraging NRF for NF discovery in 5G networks offers improved efficiency, scalability, low latency, security, and support for advanced network functionalities compared to relying solely on DNS servers in 4G networks.
References:
3GPP TS 23.501 – System Architecture for the 5G System
3GPP TS 29.510 – Network Function Repository Services
GSA: More 5G SA devices, but commercial 5G SA deployments lag
Global 5G Market Snapshot; Dell’Oro and GSA Updates on 5G SA networks and devices
Ericsson Mobility Report touts “5G SA opportunities”
Analysys Mason: 40 operational 5G SA networks worldwide; Sub-Sahara Africa dominates new launches
Samsung and VMware Collaborate to Advance 5G SA Core & Telco Cloud
5G SA networks (real 5G) remain conspicuous by their absence
GSM 5G-Market Snapshot Highlights – July 2023 (includes 5G SA status)
About the Author:
Ajay Lotan Thakur, Senior IEEE Member, IEEE Techblog Editorial Board Member, BCS Fellow, TST Member of ONF’s open source Aether (Private 5G) Project, Cloud Software Architect at Intel Canada.

Blog post edited by Alan J Weissberger
FCC Draft Net Neutrality Order reclassifies broadband access; leaves 5G network slicing unresolved
Introduction:
The FCC will take a series of steps to reestablish the commission’s net neutrality framework and reclassify broadband internet access service (BIAS) as a Communications Act Title II telecom service in a 434 page declaratory ruling and order which doesn’t resolve the issue of network slicing as a paid priority 5G service.
A draft of the items to be considered during the agency’s April meeting, released Thursday, would establish “broad” and “tailored” forbearance for ISPs. “Access to broadband Internet is now an unquestionable necessity. We also exercise broad forbearance for broadband providers as part of the Title II reclassification. Since the Commission’s abdication of authority over broadband in 2017, there has been no federal oversight over this vital service. This item would reestablish the Commission’s authority to protect consumers and safeguard the fair and open Internet, which protects free expression, encourages competition and innovation, and is critical to public safety and national security.”
Network Slicing:
The draft doesn’t make a final determination on how network slicing should be treated under the rules. Network slicing, which requires a 5G SA core network, enables 5G network operators to create multiple virtual networks on top of a shared network. How slicing should be treated has been hotly contested.
“To the extent network slicing falls outside of BIAS, we will closely monitor these uses to evaluate if they are providing the functional equivalent of BIAS, being used to evade our open Internet rules, or otherwise undermining investment, innovation, competition, or end-user benefits in the Internet ecosystem,” the draft said.
“The record reflects that the potential use cases for network slicing are still under development” and that carriers “are in the early stages of adopting the technique, with some moving more quickly than others. Given the nascent nature of network slicing, we conclude that it is not appropriate at this time to make a categorical determination regarding all network slicing and the services delivered through the use of network slicing.”
Yet the document also says it agrees with NCTA “that we ‘should not allow network slicing to be used to evade [the] Open Internet rules.’”
“The FCC declined to do what either side wanted” on slicing, New Street’s Blair Levin stated in a note to investors. “While this was not the clear, decisive win the wireless providers may have hoped for, we don’t believe this or a future FCC is likely to crack down on the primary uses of network slicing, which we understand to be network management techniques that better match wireless services to specific needs in ways that increase spectrum utilization.”
“The text left me rather confused more than reassured,” Digital Progress Institute President Joel Thayer said Friday. The commission seems interested in addressing slicing case by case, he said: “This does not bode well for consumer-facing uses of slicing as that tech starts to develop.”
One implication is the FCC might crack down on slicing if the agency sees it as a form of paid prioritization of network traffic, said Jonathan Cannon, R Street Institute policy counsel-technology and innovation and former aide to FCC Commissioner Nathan Simington.
The report and order would: “Reinstate straightforward, clear rules that prohibit blocking, throttling, or engaging in paid or affiliated prioritization arrangements, and adopt certain enhancements to the transparency rule.”
………………………………………………………………………………………………………………
The new FCC order would adopt “conduct-based rules” in the commission’s net neutrality framework, establishing “bright-line rules to prohibit blocking, throttling, and paid prioritization” by ISPs. An accompanying draft report and order would also reinstate a general conduct standard and establish a “multi-faceted enforcement framework.”
The draft declaratory ruling would officially reclassify broadband as a Title II service, saying the step would allow the commission to “more effectively safeguard the open internet” and establish a nationwide framework. The draft would largely adopt the commission’s 2015 rules on forbearance, making clear that the record “does not convincingly show that imposing universal service contribution requirements on BIAS is necessary at this time.”
The commission in the draft defended reclassification as a national security matter, noting it has previously taken action under Title II to address national security threats against voice services. “The nation’s communications networks are critical infrastructure, and therefore too important to leave entirely to market forces that may sometimes, but not always, align with necessary national security measures,” the item said.
The draft declaratory ruling also addresses the impact of reclassification on the commission’s universal service goals under section 254 of the Communications Act. Reclassification “will put the commission on the firmest legal ground to promote the universal service goals of section 254 by enabling the commission and states to designate BIAS-only providers” as eligible telecom carriers, the draft said, adding that BIAS-only providers would be allowed to participate in the high-cost and Lifeline programs.
The draft elaborates on the importance of reclassifying broadband to the agency’s authorities under Section 214 of the Communications Act, another issue raised by industry (see 2403070040). Reclassification “enhances the Commission’s ability to protect the nation’s communications networks from entities that pose threats to national security and law enforcement.”
“We find that reclassification will significantly bolster the Commission’s ability to carry out its statutory responsibilities to safeguard national security and law enforcement,” the draft said: “There can be no question about the importance to our national security of maintaining the integrity of our critical infrastructure, including communications networks.” It noted that Congress created the FCC “for the purpose of the national defense.”
The agency dismissed arguments that reclassification isn’t justified for national security purposes: “The nation’s communications networks are critical infrastructure, and therefore too important to leave entirely to market forces that may sometimes, but not always, align with necessary national security measures.” Arguments about potential costs “are unpersuasive given that, at this point, they represent only speculation about hypothetical costs and burdens.”
A draft order on reconsideration included with Thursday’s item said the net neutrality order would resolve four outstanding petitions for reconsideration filed against the FCC’s 2020 net neutrality remand order by Incompas, California’s Santa Clara County, Public Knowledge, and jointly several public interest groups including Common Cause. “As a procedural matter, we find that we have effectively provided the relief sought by each of the Petitions through a combination of the 2023 Open Internet NPRM and today’s actions,” the draft order said. “In light of the Commission’s actions today, we grant in large part and otherwise dismiss as moot” all four petitions for reconsideration. “We agree with the petitioners that the Commission’s analysis in the [Restoring Internet Freedom] Order and RIF Remand Order was insufficient in addressing the public safety, pole attachment, and Lifeline-related repercussions of classifying BIAS as a Title I service,” the draft said.
House Commerce Committee ranking member Frank Pallone, D-N.J., and Communications Subcommittee ranking member Doris Matsui, D-Calif., praised Rosenworcel “for moving to finalize rules that reflect reality: broadband internet service is critical infrastructure and an indispensable part of American life, and it must be treated that way.” The FCC’s move for Title II reclassification shows the commission is “recognizing this reality and asserting its rightful authority over broadband providers in order to protect this vital service and the hundreds of millions who rely on it each day,” Pallone and Matsui said. The two lawmakers “have confidence that a court reviewing this action will uphold it, just as courts have done in the past.” Sens. Ed Markey, D-Mass., and Ron Wyden, D-Ore., also lauded the proposal Thursday after earlier urging Rosenworcel to prevent loopholes in the rules.
The House Commerce GOP majority was tight-lipped after the draft’s release Thursday. Republican members tweeted Wednesday that the net neutrality proposal showed the commission “continues pushing Biden’s Broadband Takeover by imposing unnecessary heavy-handed regulations.”
References:
https://docs.fcc.gov/public/attachments/DOC-401676A1.pdf
https://communicationsdaily.com/reference/2404040064?BC=bc_661167bc293cd
https://communicationsdaily.com/article/view?search_id=847526&id=1928175
BT Group, Ericsson and Qualcomm demo network slicing on 5G SA core network in UK
ABI Research: 5G Network Slicing Market Slows; T-Mobile says “it’s time to unleash Network Slicing”
Ericsson, Intel and Microsoft demo 5G network slicing on a Windows laptop in Sweden
Is 5G network slicing dead before arrival? Replaced by private 5G?
5G Network Slicing Tutorial + Ericsson releases 5G RAN slicing software
Network Slicing and 5G: Why it’s important, ITU-T SG 13 work, related IEEE ComSoc paper abstracts/overviews
Telstra achieves 340 Mbps uplink over 5G SA; Deploys dynamic network slicing from Ericsson
Australian telco Telstra announced this week that it has achieved a 5G uplink speed of 350 Mbps over 5G Standalone (SA) using sub-6 GHz frequencies in a live commercial network in partnership with Ericsson and Qualcomm. Telstra claims this as a new global record for 5G uplink speed, which is 100 times faster than the average 3G uplink speed.
Telstra’s new 5G SA uplink capability combines its mid-band spectrum holdings to create a 140MHz channel for sending data from the device to the network.
The tests were completed using a mobile test device powered by Qualcomm Technologies’ latest Snapdragon® 5G modem-RF System and an existing in-market NetGear Nighthawk M6 Pro Mobile Broadband device in the live commercial network on the Gold Coast.
The latest software from Ericsson brings together different combinations of frequency ranges and types to enable a single 5G uplink and downlink data channel.
By aggregating carrier bands, it considerably increases the uplink speeds, while the ability to use low band carriers in these combinations of frequencies delivers improved coverage and performance enhancements for the 5G SA Network.
Mr Amirthalingam says: “The uplink and downlink 5G data channels work together to provide a seamless and almost symmetrical like 5G service, meeting the increasing demand for data-intensive applications such as augmented and virtual reality, or sharing photos and memorable movie moments with friends.
“The technology also includes advanced features in the base station that can prioritise different types of data and applications and can support future differentiated services, like network slicing.”
“On top of this, Telstra also has the option to use the n5 (850MHz) carrier that is currently serving its 3G Network. “
“Our latest 5G Standalone uplink speed achievement is 100 times faster than the typical 3G uplink speed, which is great news for customers. Enterprise Applications such as these are increasingly becoming more uplink heavy with things like such as high-definition video surveillance cameras and the faster speeds and coverage will all provide a much better experience.”
“The ability to use low band frequencies and repurpose our 3G low band 850 MHz frequency to deliver 5G SA coverage when the 3G network closes on 30 June 2024, has the benefit of providing improved depth of coverage and enhancing the 5G experience for customers.”
“It’s a further example of how we are leading the way in 5G innovation and investment, and how we are committed to delivering the best and most advanced network for Australia.”
To test and validate this capability, Telstra worked with long-term partners Ericsson, the global leader in 5G network equipment, and Qualcomm, one of the world’s leading wireless chipset companies.
Emilio Romeo, Head of Ericsson Australia and New Zealand, says: “Ericsson’s latest software features enables Telstra to capitalize the full spectrum portfolio for a wider coverage whilst providing far superior data rates. Customers will be empowered to explore new experiences offered with 5G Standalone such as differentiated services and a range of applications, which will in turn drive network monetization.”
Durga Malladi, Senior Vice President and General Manager, Technology Planning & Edge Solutions Qualcomm Technologies, Inc., says: This live test proves that uplink carrier aggregation on 5G Standalone network has the potential to significantly increase upload speeds and capacity, thus unlocking new experiences for consumers.”
This latest achievement takes Telstra’s World-First count to 53 since the launch of 3G. It is only through its collaboration efforts with industry and its strategic partners, like Ericsson and Qualcomm, that it can deliver the technology innovation and leadership that its customers can benefit from.
……………………………………………………………………………………………………………………
Telstra has also implemented Ericsson’s Dynamic Network Slicing software for automated network orchestration. This software gives the operator a fully automated and monetizable network slicing orchestration capability to sell slicing services to enterprise customers.
………………………………………………………………………………………………………………
References:
Telstra’s T25 to extend 5G coverage and offer enhanced customer experiences
Telstra wins most lots in Australia’s 5G mmWave auction
BT Group, Ericsson and Qualcomm demo network slicing on 5G SA core network in UK
Years after 5G network slicing was hyped to the sky (see References below dating from 2028), BT Group, Ericsson and Qualcomm Technologies, Inc. have successfully demonstrated end-to-end consumer and enterprise 5G differentiated connectivity enabled by 5G network slicing on Ericsson’s 5G Core and Radio Access Network technology in the UK with devices powered by the Snapdragon ® 8 Gen 2 for Galaxy Mobile Platform.
The trial, which took place at Adastral Park, BT Group’s home of research and innovation, established network slices for Gaming, Enterprise and Enhanced Mobile Broadband (eMBB), and showed how, by allocating a portion of the 5G SA network to provide dynamic partitions for specific use-cases, optimal performance can be maintained for bandwidth-heavy activities including mobile gaming and video conferencing even during peak times.
Mobile gaming is experiencing relentless growth, with traffic on EE’s network almost doubling since the beginning of 2023 to more than two petabytes of data every month. With consistent low-latency, jitter-free and immersive experiences increasingly essential to the gaming experience, network slicing is expected to be a key enabler of performance and growth in the 5G SA era.
Together, BT Group, Ericsson and Qualcomm Technologies demonstrated an optimal mobile cloud gaming experience on Nvidia’s GeForce Now, maintaining a throughput comfortably in excess of the recommended 25 Mbps at 1080p even when a background load was generated. The companies initiated a gaming session on Fortnite using the Samsung S23 Ultra device, equipped with the Snapdragon 8 Gen 2 for Galaxy Mobile Platform, and Ericsson implemented Network slicing along with the Ericsson RAN feature Radio Resource Partitioning on EE’s Network to achieve a smooth experience. The experience was simultaneously compared to a non-optimised eMBB RAN partition, which was congested by the background load, resulting in a less than optimal gaming experience.
The trial also validated the potential of network slicing for BT Group’s business customers. Using the enterprise and eMBB slices, configured via URSP rules which enables a device to connect to multiple network slices simultaneously depending on the application, it demonstrated consistent 4K video streaming and enterprise use-cases using the Samsung S23 Ultra device, powered by Snapdragon 8 Gen 2 for Galaxy. Enterprise communications platforms and video applications such as YouTube require a stable connection and low jitter to work well. The Ericsson 5G RAN Slicing feature, Radio Resource Partitioning, was enabled to ensure the enterprise traffic to achieve an optimal experience.
5G network slicing requires a 5G SA core network. It supports these diverse services and reassigns resources as needed from one virtual network slice to another, making the one-size-fits-all approach to service delivery obsolete.
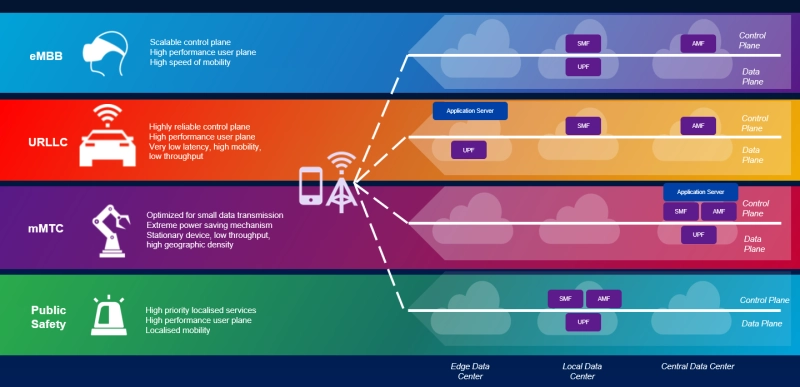
Image courtesy of Viavi
Greg McCall, Chief Networks Officer, BT Group, said: “Network slicing will enable us to deliver new and improved capabilities for customers in the 5G SA era. As we work diligently towards the launch of our own 5G SA network, today’s successful demonstration of how slicing enables us to differentiate Quality of Service to guarantee performance for different segments is a significant milestone, and illustrative of the new services that will be enabled by 5G SA.”
Enrico Salvatori, Senior Vice President and President, Qualcomm Europe/MEA of Qualcomm Europe, Inc., said: “We are proud to collaborate with BT Group and Ericsson on the network slicing trial, which used a device powered by the Snapdragon 8 Gen 2 for Galaxy mobile platform. Together, we showcased the enhanced performance and flexibility 5G Standalone capabilities, such as network slicing, will bring to consumers and enterprise experiences.”
Katherine Ainley, CEO, Ericsson UK & Ireland, said: “5G standalone and network slicing demonstrates that leading operators like EE will be able to offer customers tailored connectivity with different requirements on speed, latency and reliability for specific applications, such as video streaming and gaming. This ultimate next step in connectivity will enable new service offerings for consumers and businesses who require premium performance, while helping to drive future market growth and innovation for the UK in a wide range of new industries.”
References:
ABI Research: 5G Network Slicing Market Slows; T-Mobile says “it’s time to unleash Network Slicing”
Ericsson, Intel and Microsoft demo 5G network slicing on a Windows laptop in Sweden
Ericsson and Nokia demonstrate 5G Network Slicing on Google Pixel 6 Pro phones running Android 13 mobile OS
Samsung and KDDI complete SLA network slicing field trial on 5G SA network in Japan
Nokia and Safaricom complete Africa’s first Fixed Wireless Access (FWA) 5G network slicing trial
Is 5G network slicing dead before arrival? Replaced by private 5G?
5G Network Slicing Tutorial + Ericsson releases 5G RAN slicing software
Network Slicing and 5G: Why it’s important, ITU-T SG 13 work, related IEEE ComSoc paper abstracts/overviews
https://www.viavisolutions.com/en-us/5g-network-slicing