Have we come full circle – from SD-WAN to SASE to SSE? MEF’s SD-WAN and SASE standards
Backgrounder – SD-WAN and SASE:
A software-defined wide area network (SD-WAN) uses software-defined network technology, mostly to communicate over the Internet using overlay tunnels which are encrypted when destined for internal organization locations. If standard tunnel setup and configuration messages are supported by all of the network hardware vendors, SD-WAN simplifies the management and operation of a WAN by decoupling the networking hardware from its control mechanism. This concept is similar to how software-defined networking implements virtualization technology to improve data center management and operation.[1] In practice, proprietary protocols are used to set up and manage an SD-WAN, meaning there is no decoupling of the hardware and its control mechanism.
A key application of SD-WAN is to allow companies to build higher-performance WANs using lower-cost and commercially available Internet access. That enables businesses to partially or wholly replace more expensive private WAN connection technologies such as MPLS. When SD-WAN traffic is carried over the Internet, there are no end-to-end performance guarantees. In sharp contrast, Carrier MPLS VPN WAN services are not carried as Internet traffic, but rather over carefully-controlled carrier capacity, and do come with an end-to-end performance guarantee.
Gartner’s 2022 SD-WAN Magic Quadrant report identified Cisco, Fortinet, VMware, Palo Alto Networks, Hewlett Packard Enterprise (HPE) Aruba, and Versa Networks as market leaders. The analyst firm estimates the top 10 vendors make up more than 80% of the market. To determine SD-WAN leaders, Gartner reviewed vendors’ product capabilities such as the ability to operate as a branch office router, and having a centralized management for devices, zero-touch configuration, and VPN with a basic firewall. The analyst firm also reviewed vendors’ business and financial performance based on their volume of customers, sites, and contracts.
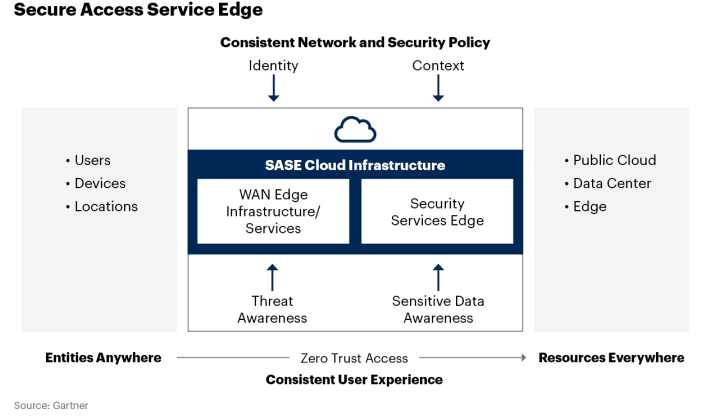
Gartner coined the acronym SASE (Secure Access Service Edge) in an August 2019 report The Future of Network Security in the Cloud and expanded its functionality in their 2021 Strategic Roadmap for SASE Convergence. SASE combines network security functions (such as SWG, CASB, FWaaS and ZTNA), with WAN capabilities (e.g. SD-WAN) to support businesses’ secure access needs. Previously, security for SD-WAN was an open, unresolved issue.
SASE is a holistic framework that brings security and networking connectivity together through a cloud-centric base. Businesses can save equipment, human and financial resources thanks to SASE’s underlying cloud design, and they can scale performance with minimal hardware needs.
Omdia Analyst Fernando Montenegro describes SASE as a “framework architecture, not a solution.”
MEF SD-WAN and SASE Standards:
In August 2019, the MEF published the industry’s first global standard defining an SD-WAN service and its service attributes. SD-WAN Service Attributes and Services (MEF 70). The MEF SD-WAN standard describes requirements for an application-aware, over-the-top WAN connectivity service that uses policies to determine how application flows are directed over multiple underlay networks irrespective of the underlay technologies or service providers who deliver them. However, it does not address interoperability because it does not specify either a UNI or NNI protocol stack.
MEF 70 defines:
- Service attributes that describe the externally visible behavior of an SD-WAN service as experienced by the subscriber.
- Rules associated with how traffic is handled.
- Key technical concepts and definitions like an SD-WAN UNI, the SD-WAN Edge, SD-WAN Tunnel Virtual Connections, SD-WAN Virtual Connection End Points, and Underlay Connectivity Services.
SD-WAN standardization offers numerous benefits that will help accelerate SD-WAN market growth while improving overall customer experience with hybrid networking solutions. Key benefits include:
- Enabling a wide range of ecosystem stakeholders to use the same terminology when buying, selling, assessing, deploying, and delivering SD-WAN services.
- Making it easier to interface policy with intelligent underlay connectivity services to provide a better end-to-end application experience with guaranteed service resiliency.
- Facilitating inclusion of SD-WAN services in standardized LSO architectures, thereby advancing efforts to orchestrate MEF 3.0 SD-WAN services across automated networks.
- Paving the way for creation and implementation of certified MEF 3.0 SD-WAN services, which will give users confidence that a service meets a fundamental set of requirements.
Last year MEF introduced an updated version of its SD-WAN standard, MEF 70.1, which added critical enhancements. MEF is also currently at work on version MEF W70.2 and MEF W119 Universal SD-WAN Edge, which will address the need for interoperability, among other things.
In December 2022, MEF published two Secure Access Service Edge (SASE) standards defining 1.] SASE service attributes, common definitions & a framework and 2.] a Zero Trust framework that together allow organizations to implement dynamic policy-based actions to secure network resources for faster decision making and implementation for enterprises. MEF’s SASE standard defines common terminology and service attributes which is critically important when buying, selling, and delivering SASE services. It also makes it easier to interface policy with security functions for cloud-based cybersecurity from anywhere. MEF’s Zero Trust framework defines service attributes to enable service providers to implement and deliver a broad range of services that comply with Zero Trust principles.
- SASE Service Attributes and Service Framework Standard: specifies service attributes to be agreed upon between a service provider and a subscriber for SASE services, including security functions, policies, and connectivity services. The standard defines the behaviors of the SASE service that are externally visible to the subscriber irrespective of the implementation of the service. A SASE service based upon the framework defined in the standard enables secure access and secure connectivity of users, devices, or applications to resources for the subscriber. MEF’s SASE standard (MEF 117) includes SASE service attributes and a SASE service framework.
- Zero Trust Framework for MEF Services: The new Zero Trust Framework for MEF Services (MEF 118) defines a framework and requirements of identity, authentication, policy management, and access control processes that are continuously and properly constituted, protected, and free from vulnerabilities when implemented and deployed. This framework also defines service attributes, which are agreed between a subscriber and service provider, to enable service providers to implement and deliver a broad range of services that comply with Zero Trust principles.
–>PLEASE SEE Pascal Menezes CTO of MEF COMMENTS BELOW THIS ARTICLE.
………………………………………………………………………………………………………………………………………………………………………………..
Enter SSE (Secure Service Edge):
In it’s above referenced 2021 report, Gartner defined SSE (Secure Service Edge) which is a separate entity that doesn’t include SD-WAN. “SSE is the security components of SASE focusing largely on the cloud access security broker, secure web gateway, and zero-trust network access products to enable secure use of the internet and cloud services for a hybrid workforce working from anywhere,” Gartner analyst Charlie Winckless told SDxCentral.
Telefónica tapped cloud security vendor Zscaler to develop a new managed SSE platform in a bid to address changing workforce dynamics and cloud consumption. The announcement illustrated a growing trend around the Gartner-coined product category, in which cloud security and SASE vendors alike announce “new” products and services around the buzzword.
But for the most part, these SSE products aren’t so much new as they’re rebranded and repackaged SASE services that’ve been stripped of their SD-WAN capabilities, if they ever had them in the first place. Zscaler’s SSE is built around the same Zscaler Internet Access and Zscaler Private Access products that, just a few months ago, it was calling SASE.
“The contrast is that SASE focuses on a user’s secure access needs as a part of the solution. SSE, on the other hand, mainly focuses on cloud-centric security services for the protection of users,” according to Juta Gurinaviciute, Forbes Councils Member and CTO for NordLayer, a remote access security provider. Gurinaviciute explained that SSE is SASE minus SD-WAN. SSE is essentially a way for enterprises to focus more on cloud-based security as a stepping stone to a full SASE service. She wrote:
As per Gartner’s suggestion, some companies may select a single-provider SASE offering, while others prefer partnered SD-WAN and SSE offerings from separate providers based on companies’ needs. Your business may have already invested in SD-WAN in advance. SSE would be a more meaningful choice in the short-term in such a case. If your company’s current setup doesn’t need SD-WAN, security may be a much more urgent requirement, in which case SSE would make more sense. Even if your organization only has a single regional branch or a simple branch, SSE may still be helpful.
Considering all of these reasons, SASE, the implementation of which may seem challenging and daunting for security professionals, can be done much faster with SSE adaptation first. The journey can be completed much more smoothly using this option, and SSE may benefit a wide range of companies that need robust protection.
“I think everybody’s really excited about SASE because enterprises keep asking about it,” Omdia Analyst Adeline Phua told Light Reading in a recent podcast. “It’s got so much buzz in the market.” However, Phua found that excitement about SASE/SSE hasn’t necessarily equated to mass adoption of the service. “We’re thinking that maybe adoption is really hitting that tipping point, only to find out when we talk to service providers and to enterprises that the adoption is really not there yet,” she added.
A Dell’Oro group July 2022 report found that the SSE market grew 40% year-over-year to more than $800 million in the first quarter. A December report noted that SSE achieved its tenth consecutive quarter of sequential revenue expansion in 3Q-2022. Dell’Oro’s Director of Network Security, SASE, and SD-WAN Mauricio Sanchez said the strong growth is a testament to more enterprises preferring cloud-delivered security over traditional on-premises solutions. Sanchez told SDX Central: “The growth factors that have existed largely since the pandemic started are still with us. That’s the shift to hybrid work, the shift of workloads to the cloud, and the importance of the digital experience.”
While Dell’Oro forecasts the overall SASE market to grow to $8 B for the full year 2023, an Omdia survey found that SD-WAN is only expected to achieve 87% market penetration at the end of 2023. Omdia’ Phua says that enterprises which are using SD-WAN aren’t deploying it at all their sites. Part of the problem stems from supply chain challenges triggered by COVID-19 which have resulted in a shortage of products and SD-WAN deployment delays.
Where service providers can make progress in assisting their enterprise customers’ adoption of SASE is by providing it as a managed service with significant value add “on top of just the staff, the platform itself,” explained Omdia’s Fernando Montenegro. That might look like providing more visibility into network health and potential security threats.
Phua echoed Montenegro’s assessment: “Service providers will still need to keep looking out for new innovations and what else can we onboard to make sure that is a more complete solution for the enterprise customers. So there’s still a lot of way to go in terms of this journey.”
References:
https://en.wikipedia.org/wiki/SD-WAN#
https://www.gartner.com/en/documents/3957375
https://www.gartner.com/en/documents/3999828
https://www.lightreading.com/sd-wan/looking-ahead-sase-is-too-messy/a/d-id/782090?
Dell’Oro: SASE Market grew 33% in 2022; forecast to hit $8B in 2023
Gartner: SASE tops Gartner list of 6 trends impacting Infrastructure & Operations over next 12 to 18 months
Dell’Oro: Secure Access Service Edge (SASE) market to hit $13B by 2026; Gartner forecasts $14.7B by 2025; Omdia bullish on security
Enterprises Deploy SD-WAN but Integrated Security Needed
MEF survey reveals top SD-WAN and SASE challenges
MEF New Standards for SD-WAN Services; SASE Work Program
Shift from SDN to SD-WANs to SASE Explained; Network Virtualization’s important role
6 thoughts on “Have we come full circle – from SD-WAN to SASE to SSE? MEF’s SD-WAN and SASE standards”
Comments are closed.



Yes we are addressing SD-WAN interoperability with a new specification coming out called MEF W119. It is in working draft status and ETA plans for standardization is in the second half of 2023. MEF W119 is about a Universal SD-WAN Edge that allows interoperability with vendor-proprietary SD-WAN Edges. This standard when released defines Universal SD-WAN Edge and specifies requirements for interoperability between a vendor-proprietary SD-WAN Edge and implementations of the Universal SD-WAN Edge. A Universal SD-WAN Edge can participate as an SD-WAN Edge in a MEF-compliant SD-WAN Service (as specified in MEF 70.1 with SD-WAN Edges provided by other vendors that meet the requirements specified herein.
The Universal SD-WAN Edge included in this specification covers the following interoperability :
Universal Management Plane
Universal Control Plane Function
Universal Data Plane
Subscriber Routing Function
Fault Monitoring and Detection
Performance Monitoring
Telemetry operation
Some of these functions, as described, are required to be supported in both the Universal SD-WAN Edge and the interconnected vendor-proprietary SD-WAN Edges and service constructs. Other functions are required in the Universal SD-WAN Edge only.
Also MEF did publish version 2 of the original MEF SD-WAN standard service definition which is called 70.1 . It can be found here https://www.mef.net/resources/mef-70-1-sd-wan-service-attributes-and-service-framework/ We are already working on version 3 which should also be available onetime 2023 2nd half timed with Universal SD-WAN MEF W119
From SDxCentral:
Analysts expect that Secure access service edge (SASE) total worldwide end-user spending will reach $9.2 billion in 2023, marking a 39% increase from 2022.
Gartner, who coined the acronym, also announced its single-vendor SASE leaders. The firm’s definition specifies that a complete SASE offering combines network edge capabilities like SD-WAN, and a set of cloud-centric security service edge (SSE) capabilities, including secure web access gateway (SWG), cloud access security broker (CASB), firewall-as-a-service (FWaaS), and zero-trust network access (ZTNA).
While many vendors still can only supply components of SASE, Gartner recognized nine that offer complete solutions with both networking and SSE capabilities – Cato Networks, Cisco, Citrix, Forcepoint, Fortinet, Netskope, Palo Alto Networks, Versa Networks, and VMware.
Executives from these companies gave SDxCentral their predictions for what 2023 has in store for the SASE market and technologies:
Shlomo Kramer, CEO, Cato Networks
“Just as COVID caused a massive acceleration in digital transformation projects, the recession will accelerate security consolidation. Numerous studies indicate that enterprises maintain dozens of security tools. And with so many security tools, controls are fragmented resulting in reduced visibility; operational overhead increases with the need for extra personnel and skills to master the various tools; and gaps between tools are created leaving the cracks through which attackers can infiltrate. Most companies (75%) expect to reduce the number of security vendors they use, replacing them with one, converged security platform.
Due to recessionary factors, IT staff will be pressured more than ever to do more with less, accelerating the move toward ‘as-a-service’ models. Numerous reports indicate that this recession will be unusual, not marked by the unemployment typical of a recession. But if layoffs are not part of the recession-coping toolbox, organizations will need to find other ways to reduce costs. Adoption of as-a-service models enables IT teams to tap expertise and tools that otherwise would be difficult to onboard.”
Jim Fulton, VP of Product, Forcepoint
“Organizations will further optimize their networking and security for the merging hybrid workforce, and SASE will continue its move into the mainstream as the architecture of choice for those initiatives.
The distinction between single-vendor SASE solutions (SD-WAN and SSE from the same vendor) versus separate SD-WAN and SSE providers will become more prominent as organizations look for ways to simplify their operations during an economic downturn. We will see organizations continue to consolidate vendors and demand platforms that are geared toward reducing the operational burden on security and networking teams, especially during a rocky economy.
Replacing VPNs with ZTNA will accelerate as organizations look to reduce costs and boost control over access to business resources. The role of data security in SASE will continue to grow as organizations realize that it’s not enough to protect how users get to the web, cloud, and private apps. Keeping control of what they do with data after they get there is just as important.”
Nirav Shah, VP of Products, Fortinet
“As the SASE market matures, CIOs will increasingly stop looking at SASE in a silo and examine it as part of their entire infrastructure. We don’t see a cloud-only world in the future, likewise we don’t see an on-premises-only world. SASE is an important cloud-delivered architecture for securing remote access, but it’s important to look at the reality of how most enterprises are building hybrid networks to meet their business needs. That means building a SASE architecture – what is essentially the convergence of cloud-delivered networking and security technologies – with products that are able to seamlessly integrate with each other and with converged on-premises solutions. This ensures enterprises preserve their existing on-premises investments (including SD-WAN investments), and prevents having to completely re-architect everything you already have deployed.
Thinking that convergence only needs to be in the cloud or convergence only needs to be on-premises when you have a hybrid network is not the right way to think – you need both. Many organizations today struggle with complexity because they have taken a piecemeal approach, using disparate tools from multiple vendors to support their security and connectivity needs at headquarters, branch offices, and remote workforce. In 2023, we’ll see more and more CIOs prioritizing consolidation by choosing solutions that can seamlessly integrate across both cloud and on-prem to ensure consistent security and a consistent user experience no matter where users or applications are distributed. We see this same trend manifesting in how CIOs are evaluating ZTNA solutions.”
Naveen Palavalli, VP of Product GTM Strategy, Netskope
“2022 was a challenging year for many organizations, but many are anticipating that 2023 will see continued economic headwinds. As a result, organizations will be looking especially close at how SASE can enable them to continue growing in an optimized, efficient manner. SASE features a number of consolidation and cost-savings benefits, and these will likely feature more heavily in business cases presented to the CIO and executive decision makers, in addition to traditional SASE value drivers like superior user experience or comprehensive security.
Another trend we will see more of in 2023 is the increased adoption of single-vendor SASE solutions by larger organizations. Until recently, these organizations looked primarily at dual-vendor SASE solutions based upon mature, trusted, cloud security platforms and established SD- WAN offerings. However, as complete, robust single-vendor solutions emerge that match or exceed the functionality of their dual-vendor counterparts, these will increase in popularity and market acceptance over the course of the year.
Finally, in 2023, organizations will look to apply some of the evolutionary principles introduced by ZTNA – a fundamental part of SASE – and apply them to the LAN. ZTNA provided remote workers with faster, more secure access to private applications.”
Kumar Ramachandran, SVP Products – Network Security, Palo Alto Networks
“With the recent emergence of multiple single-vendor SASE offerings, these solutions will become preferred over multi-vendor solutions (a.k.a. mix-and-match SASE). This will be driven by increased awareness of the shortcomings of mix- and-match SASE and new capabilities coming from more advanced single-vendor solutions.
Since its introduction earlier this year, ZTNA 2.0 has been gaining traction amongst security-minded early adopters. We expect ZTNA 2.0 to go mainstream in 2023.
The convergence of networking and security solutions, combined with AI and ML, will enable IT teams to predict and resolve issues with applications, networks, and security posture before they cause business disruptions. These cutting-edge capabilities will drive increased productivity and enable IT organizations to go from a reactive to a proactive posture.”
Kelly Ahuja, CEO, Versa Networks
“While the market was initially driven by remote user access to cloud workloads, SASE has emerged as the technology to protect and connect across the entire enterprise footprint. Enterprises are seeking extensible solutions as opposed to point products or technologies that they must integrate themselves. In 2023, SASE solutions that protect enterprise resources while delivering the optimal user/device-to-app or app-to-app experience, simplify policy definition, and add lifecycle management will emerge and establish themselves as the way of future.
SASE has quickly evolved from a set of discrete technologies or functions to a future state blueprint for integrating security and networking. Early adopter enterprises have started their journey to this future state and are charting the course to nirvana. Lessons learned from these early adopters will drive the strategy of the late majority. Their choice of a platform approach versus a portfolio approach will be driven by cost, agility, and operational flexibility. The market opportunity is bigger than it has ever been.”
Karl Brown, Senior Director, VMware
“Enterprise lines of business and operational technology teams are developing new applications or modernizing legacy applications to meet their business objectives. These new applications will collect and process volumes of ephemeral data from a large number and wide array of devices in near real-time. This volume of data and requirements for low latency will mean backhauling data to a cloud or traditional data center is not economically or technically feasible. Thus, requirements for SD-WAN and SASE will expand to encompass several factors.
Connectivity to the edge: Much like connectivity to the cloud, applications at the edge will require a low-latency, secure, and resilient network infrastructure. Further, many new intelligent endpoints will require 5G or 4G LTE LAN connectivity for enhanced mobility, coverage, performance, and reliability.
Compute at the edge: Applications at the edge will require compute capabilities. Deploying dedicated servers is not feasible in many locations because they add to the operational burden while posing security risks. Instead, enterprises should look for SD-WAN and SASE solutions that can host edge applications.
Intelligence about the edge: An understanding of application performance at the edge requires AI-assisted tools given the large volume of endpoints and the increased number of workloads. Therefore AIOps-based functionality is a requirement for SD-WAN and SASE management to function optimally.”
Citrix responded to SDxCentral saying they will be less focused on SASE moving forward, but “rather SSE which is more applicable to their portfolio.” Cisco did not respond to request for comment before publication.
https://www.sdxcentral.com/articles/interview/top-sase-execs-make-2023-predictions/2023/01/
Security Service Edge vs. SASE: What Is the Difference?
Secure Access Service Edge (SASE) is a category of networking solutions defined by Gartner in 2019, which combines traditional network security functions with wide area networking (WAN) capabilities. The goal of SASE is to provide secure and reliable connectivity for users and devices, regardless of their location or the type of network they are connected to.
Gartner defines SASE as a cloud-delivered, network security as a service platform that provides secure network connectivity and network security functions in a unified offering, delivered through a common infrastructure and management. SASE combines network security functions, such as zero trust networking, firewalls, and intrusion prevention systems (IPS), with cloud-based networking services like SD-WAN (software-defined wide area networking) and internet connectivity.
……………………………………………………………………..
Secure Services Edge (SSE) is a set of integrated, cloud-delivered secure services that use identities and policies to establish secure connections between authenticated users and business resources. First introduced by Gartner in 2021, SSE is a security category that will secure connectivity in the future of hybrid environments and remote work.
As more employees work outside corporate boundaries, SaaS applications become the norm, and applications move to the public cloud, organizations cannot continue to backhaul user traffic to corporate networks. Many IT organizations are replacing their existing network security appliances, such as firewalls, VPN gateway appliances, and web gateways, with cloud-based options that can better protect data, provide a better user experience, and reduce costs.
SSE platforms provide cloud services that extend secure connectivity to user locations, without connecting users to corporate networks, exposing IT infrastructure to the public internet, or requiring complex network segmentation. Instead, SSE allows IT to provide secure access from anywhere to on-premise applications, secure access to the internet, and fast access to the cloud and SaaS applications.
………………………………………………………………………………………..
Security Service Edge vs. SASE: What Is the Difference?
The main difference between Secure Access Service Edge (SASE) and Security Service Edge (SSE) is the focus of the solutions. SASE combines traditional network security functions with wide area networking (WAN) capabilities, while SSE focuses specifically on security functions.
SASE solutions are designed to provide secure and reliable connectivity for users and devices, regardless of their location or the type of network they are connected to. This can include traditional networking functions like VPNs and SD-WAN (software-defined wide area networking), as well as security functions like firewalls, intrusion prevention systems (IPS), and other controls. SASE solutions are often used by organizations with remote and hybrid workforces to ensure secure access to corporate resources and protect against cyber threats.
https://wire19.com/security-service-edge-vs-sase-difference/
I found Your SD-WAN article by chance and was pleasantly surprised. I had no idea there was so much written about SD-WANs. I am grateful for this and related IEEE Techblog articles. They have opened my eyes to how this technology can help network providers.
Also Read my article on SD-WAN and How Banking & Financial sector uses SDWAN and Cyber Hygiene for Startups
From Fierce Telecom January 12, 2023:
Randy Anders is VP of North American sales with HughesNet for Business. He said HughesNet has been providing SD-WAN to enterprise customers for several years, using its GEO satellite connectivity.
The company works with VMware, Cisco Meraki and Fortinet for the SD-WAN technology.
“We have over 52,000 SD-WAN locations and over 100 customers in the U.S. over retail, healthcare, banking, energy, restaurants and government customers,” said Anders. For instance, it connects about 2,000 gas stations in far-flung locations with SD-WAN.
He did concede that with GEO “you have the latency issue because the satellite is so much further from earth” than with LEO. But HughesNet and its partners use compression software “to make the user experience better.”
Hughes is also establishing a partnership with the LEO satellite company OneWeb. Together they’ll be able to provide LEO and GEO connectivity to suit a customer’s specific needs.
“We’ve been involved with OneWeb for a few years,” said Anders. “We’ve actually done deals where they bought 10,000 of our electronically steerable antennas.”
There’s a huge difference in the number of satellites needed for GEO as opposed to LEO.
Starlink has more than 3,000 satellites in orbit and has recently received FCC approval to launch 7,500 more. As if that’s not enough Starlink wants to launch about 20,000 more on top of that.
In comparison, Hughes needs only a handful of satellites — it uses a few of its own and has hosted payloads on a few others.
The FCC is very concerned about space debris from all the companies that are entering the satellite business.
RELATED: How does SpaceX remove old, obsolete satellites from space?
SpaceX has developed technology that can control the de-orbiting of its satellites once they reach the end of their life. Once the satellites de-orbit, they pass through the earth’s atmosphere and burn up.
But it’s different for GEO satellites. First, there are far fewer of them. Once they reach the end of their life, they move out of their operating orbit and drift further out into space.
https://www.fiercetelecom.com/telecom/hughes-geo-satellites-can-do-sd-wan-too