cyber-security
Analysis & Implications of the Communications Cybersecurity Information Sharing and Analysis Center (C2 ISAC)
The Communications Cybersecurity Information Sharing and Analysis Center (C2 ISAC), announced today, is a private sector-only nonprofit dedicated to strengthening defenses across the U.S. telecommunications industry. The founding members of C2 ISAC are: AT&T, Charter Communications, Comcast, Cox Communications, Lumen Technologies, T-Mobile, Verizon, and Zayo. The board of the nonprofit organization will comprise the chief information and security officers from each of the eight network operators, led by AT&T CISO Rich Baich as chairman. “Cybersecurity threats are more sophisticated and persistent than ever,” Baich said.
The coalition represents a strategic imperative for major network operators to build a unified, rapid-response network to counter sophisticated, AI-driven infrastructure attacks and state-sponsored espionage. It is a meaningful structural change in how the U.S. telecom sector approaches cybersecurity—especially under pressure from increasingly coordinated, AI-enabled threats and nation-state activity.
Traditional ISACs (Information Sharing and Analysis Centers) already exist across sectors—financial services, energy, healthcare—but telecom has historically been more fragmented in how it shares threat intelligence. Operators often guarded incident data due to regulatory exposure, reputational risk, and competitive sensitivities.
C2 ISAC stands out because it is explicitly private-sector-led, rather than government-anchored or compliance-driven. It focuses on telecom infrastructure itself (RAN, core, transport, signaling systems), not just enterprise IT and aims for real-time operational coordination, not just periodic intelligence reports.
“We’re not going to be operating in silos when a potential event occurs. There’ll be information sharing across all that…[and] coordinated response based on that information sharing,” said Baich. “We could be sharing vulnerabilities that we find to be an issue. We could be sharing information related to different types of cyber techniques that are being utilized. Most importantly, though, it is having that trusted forum and the right relationships that someone can just make a phone call to get an answer,” he added.
In effect, it’s closer to a joint cyber defense grid for carriers than a passive information-sharing forum. Several converging pressures explain why this is happening now:
-
AI-enhanced attack capabilities: Adversaries are using AI for automated vulnerability discovery, polymorphic malware, and adaptive intrusion techniques targeting network infrastructure (e.g., signaling exploitation, orchestration layers, and cloud-native cores).
-
State-sponsored campaigns: Groups linked to China, Russia, Iran, and DPRK have increasingly targeted telecom networks for espionage, lawful intercept bypass, metadata harvesting, and potential pre-positioning for disruption.
-
Soft targets in telecom evolution: The shift to:
-
Virtualized RAN (vRAN)
-
Open RAN (multi-vendor complexity)
-
Cloud-native 5G cores
has expanded the attack surface dramatically, especially at APIs, orchestration layers, and inter-vendor interfaces.
-
-
Regulatory pressure without operational mechanisms: Governments (e.g., via CISA, FCC, NSA advisories) have been urging collaboration, but lacked a low-friction, operator-driven mechanism for tactical data exchange.
Key C2 ISAC functions include:
-
Real-time threat intelligence sharing
-
Indicators of compromise (IOCs)
-
Tactics, techniques, and procedures (TTPs)
-
Zero-day exploitation patterns in telecom-specific protocols (e.g., SS7, Diameter, 5G SBA interfaces)
-
-
Coordinated incident response
-
Rapid cross-operator alerts when an intrusion is detected
-
Shared mitigation playbooks (e.g., blocking malicious signaling traffic patterns)
-
Potential “collective defense” actions, like synchronized filtering or patch prioritization
-
-
Infrastructure-specific vulnerability tracking
-
Vendor equipment vulnerabilities (RAN, core, routers, optical transport)
-
Software supply chain risks (containers, orchestration stacks like Kubernetes in 5G cores)
-
-
Simulation and preparedness
-
Joint exercises for large-scale outages or cyber-physical attacks
-
Red-teaming of inter-operator dependencies (e.g., roaming, interconnect)
-
Why this matters strategically:
This is less about incremental improvement and more about closing a structural asymmetry:
-
Attackers collaborate and reuse tooling globally
-
Defenders (telecom operators) have historically operated in silos
C2 ISAC is an attempt to match attacker coordination with defender coordination, particularly in a sector that underpins:
-
National security communications
-
Critical infrastructure interconnectivity
-
Emergency services
-
Financial transaction networks
In that sense, telecom is closer to energy than to typical enterprise IT—and requires a sector-wide defense posture, not just firm-level security.
Implications for the telecom ecosystem:
-
Operators: Likely to gain faster detection and response capabilities, but must overcome internal legal/compliance barriers to share sensitive data.
-
Vendors (e.g., Ericsson, Nokia, Cisco): May face stronger pressure for rapid disclosure and coordinated patching, especially if vulnerabilities affect multiple operators simultaneously.
-
Cloud providers (AWS, Azure, Google Cloud): Become indirectly implicated, since 5G cores and network functions increasingly run on hyperscaler infrastructure.
-
Government: Even though this is private-sector-led, agencies like CISA and NSA will likely act as intelligence feeders and backstops, not primary coordinators.
Risks and limitations:
-
Trust barriers: Operators must be willing to share sensitive breach data quickly—historically a weak point.
-
Legal liability concerns: Information sharing can expose firms to regulatory or litigation risk unless protected.
-
Speed vs. accuracy trade-offs: Real-time sharing increases the risk of false positives propagating across networks.
-
Vendor opacity: If equipment/software vendors are slow or incomplete in disclosures, the ISAC’s effectiveness is constrained.
A useful analogy:
C2 ISAC aims to move telecom from a model of independent air traffic control towers to a shared radar network:
Each network operator still controls its own “airspace,” but now they can all see incoming threats earlier and coordinate responses before collisions—or attacks—propagate system-wide.
References:
https://www.lightreading.com/security/eight-big-us-telcos-join-forces-on-network-cybersecurity
Key Differences Between Network Cybersecurity and Control System Cybersecurity & Why It Matters
Cybersecurity threats in telecoms require protection of network infrastructure and availability
WSJ: T-Mobile hacked by cyber-espionage group linked to Chinese Intelligence agency
GSA Meetup: Cyber Security Continues as Major Obstacle for IoT Adoption
Demythifying Cyber security: IEEE ComSocSCV April 19th Meeting Summary
Key Differences Between Network Cybersecurity and Control System Cybersecurity & Why It Matters
By Joe Weiss with Alan J Weissberger
Introduction:
The Operational Technology (OT) [1.] cybersecurity [2.] community continues to ignore control system cyber-incidents [3.] – a governance failure masquerading as a vocabulary issue.
IT and OT network data breaches are documented in multiple sources such as the Verizon Data Breach Report, CISA documents, and others. Palo Alto Networks notes that nearly 70% of industrial firms had an OT cyber-attack last year. Those cyber-attacks were from data breaches – not always causing equipment damage.
Industrial organizations need an integrated and cyber resilient IT-OT framework to address this increasingly sophisticated threat landscape, but it appears they’re not well prepared to defend against network or control system cyberattacks.
Note 1. Operational Technology refers to the combination of hardware and software designed to directly monitor, control, and manage physical devices, industrial equipment, and critical processes.
Note 2. Cybersecurity can be defined as the practice of protecting people, systems and data from cyberattacks by using various technologies, processes and policies.
Note 3. Cyber-incidents are defined as electronic communications between systems that effects Confidentiality, Integrity, or Availability. This is an IT-centric definition because Safety is not addressed.
Image Credit: txOne Networks
There are two communities addressing cybersecurity:
- The more prevalent community is the one involved in data security. This includes IT and OT network security and is focused on data breaches.
- The second community is focused on engineering security. It is less well-known, but very critical. This discipline is focused on safety, reliability, and productivity.
Professor Ross Anderson stated in his seminal book, “Security Engineering: A Guide to Building Dependable Distributed Systems,” that security engineering is about building systems to remain dependable in the face of malice, error, or mischance.”
The culture gap between network security and engineering organizations will be addressed in the June 2026 issue of IEEE Computer magazine, “Packets and Process: What Network Security and Engineering Get Wrong About Each Other.”
Discussion:
The OT cybersecurity community’s mission is to focus on OT network cyber-attacks. However, its charter does not extend to malicious and unintentional control system cyber incidents involving process sensors, actuators, motors, turbines, transformers, etc.
Importantly, control system cyber incidents can be physics-related rather than network-related. The 2007 Aurora vulnerability test at the Idaho National Laboratory destroyed a 2 MW commercial diesel generator by remotely restarting the generator out- of-phase with the grid. This is a gap in protection of the electric grid and was addressed in the October 2025 IEEE Computer magazine article, “Physics-Based Cyberattacks Against Electric Power Grids and Alternating Current Equipment.”
Idaho National Laboratory ran the Aurora Generator Test in 2007 to demonstrate how a cyberattack could destroy physical components of the electric grid. The diesel generator used in the experiment beginning to smoke as shown below:
Aurora Generator Test. Image Credit: Wikipedia
Industry and government OT cybersecurity experts continue to downplay the threat of control system cyberattacks and ignore actual control system incidents that do not originate from OT networks by not calling them cyber-related.
There have been more than 20 million control system cyber incidents that have killed more than 30,000 people. Most of these incidents occurred below the IP-Ethernet layers where there is no cyber forensics nor cybersecurity training. As a result, the majority of these incidents were not identified as being cyber-related.
This indicates that control system cyber incidents that are not classified as IP-Ethernet incidents need their own classification as issues to be addressed by cybersecurity policy, especially for critical infrastructure where accidental and/or malicious cyber failures could result in widespread death and destruction.
Given the current geopolitical environment, nation-states are actively reassessing their capabilities to disrupt adversary infrastructure at scale. In this context, dismissing control system cyber incidents solely because they do not originate from traditional IP-based vectors introduces significant risk. Threat actors are increasingly targeting critical infrastructure and associated control systems—spanning both IT and OT domains—leveraging diverse attack surfaces beyond conventional network entry points.
A parallel issue within both the IT and OT security communities is the tendency to classify incidents as “cyber” only when malicious intent is confirmed. This narrow definition is problematic.
For example, the July 2024 CrowdStrike-related outage, which caused global operational disruptions, clearly met the functional criteria of a cyber-incident due to its systemic impact on networked systems. However, its non-malicious origin led some security governance bodies to exclude it from cyber incident classification. Such distinctions can undermine resilience planning, as they fail to account for the full spectrum of cyber-induced operational risk, including software supply chain failures and systemic misconfigurations.
ERPI Focus:
The European Risk Policy Institute (ERPI) was founded by the Australian Risk Policy Institute as part of the Global Risk Policy Network. EPRI Chairman wrote in a blog titled, “Control system cyber incidents and network breaches are apples and oranges”:
“From our ERPI / 3°C World SRP® perspective, Weiss is pointing at a governance failure masquerading as a vocabulary issue: if you define “cyber incident” through an IT breach lens, you will miss (or dismiss) the incidents that actually move risk —those that degrade continuity lifelines by disrupting physical processes. He makes the case that control-system cyber incidents include electronic/automation failures across sensor signals, control logic, firmware and field device communications, and that many are non-malicious yet still produce loss of view, loss of control, equipment damage, and safety/environmental consequences.
What matters strategically is the reporting and response architecture. Breach-centric metrics (and the cultural reflex that “no attack = no incident”) bias organizations toward under-detection, weak root-cause discipline, and false trend comparisons—exactly when coupled infrastructures are most fragile and repair cycles are tight. Weiss’s bridge condition is practical: align engineering and security on a shared incident definition, and train both communities in control-system incident reality so that operational anomalies are treated as cyber-relevant signals, not “maintenance noise.”
If you’re responsible for critical infrastructure, this is a reminder to recalibrate your incident taxonomy and your board narrative: the control-room outcome is the headline, and the network story is only one possible path to it.”
The Crucial Importance of Process Sensors:
Process sensors represent the biggest gap between data security and engineering security. Perplexity.ai explains this gap in detail -see below, but first we distinguish between data security and engineering security:
- Data security focuses on IP-native devices such as firewalls, routers, switches, etc.
- Engineering security should be focused on engineering devices and equipment that could cause equipment damage and deaths but have no cybersecurity, authentication, or cyber forensics. This includes process sensors, actuators, motors, transformers, inverters, etc. However, that focus is often not achieved.
Perplexity.ai on the Data vs. Information Security Gap:
Process sensors sit at the junction of physical process integrity and digital telemetry, so they expose a gap that neither data security teams nor engineering security teams fully own today. In practice, security teams tend to focus on protecting data pipelines, identities, and networks, while engineering teams focus on measurement accuracy, calibration, availability, and safety; the sensor itself often falls between those disciplines.
Process sensors are not just data endpoints; they are safety- and control-relevant instruments whose outputs can drive operators, PLCs, DCS logic, and downstream automation. If a sensor is spoofed, degraded, miscalibrated, or manipulated, the result is not only bad data but potentially unsafe or physically damaging control actions.
Traditional data security assumes the main problem is confidentiality, integrity, and availability of information in transit or at rest. But process sensors often use legacy field protocols, serial links, gateways, or embedded devices that were engineered for function and reliability rather than cryptographic assurance, making them difficult to secure using conventional enterprise controls.
Engineering security is usually optimized for process correctness, alarms, redundancy, and fail-safe behavior, not adversarial manipulation of the measurement layer. That means the sensor may be treated as trustworthy instrumentation, even though compromised or false sensor data can undermine control logic, operator decisions, and safety systems.
The core mismatch: The real issue is that data security protects the pipeline, while engineering security protects the process, but process sensors belong to both domains. Because ownership is split, sensor trust, authentication, anomaly detection, and physical tamper resistance are often addressed inconsistently or not at all, creating a blind spot at the boundary between cyber and physical risk.
Highlights of Sensors Converge Conference Presentation:
To address these important issues and gaps, I will be presenting at the Sensors Converge conference in Santa Clara, CA on May 7, 2026. The title of my talk is, “Process Sensor Monitoring for Cybersecurity, Reliability, and Safety.” The presentation will include the following topics:
- Process sensors (Level 0 devices) are inherently cyber vulnerable yet remain largely unrecognized by cybersecurity organizations.
- Process sensor incidents, both malicious and unintentional, have caused catastrophic and fatal cyber/operational events across multiple sectors, but were not identified as being cyber-related.
- Fatalities have occurred in every decade since the 1980s, including this decade.
- Monitoring process sensors at the physics level can materially improve reliability, safety, and cybersecurity.
- A discussion of what a process sensor cybersecurity program should include and what organizations should be involved.
- The implications of process sensors which are not cyber-secure, because they don’t meet U.S. and/or EU cybersecurity requirements.
Nation-state actors, including Russia, China, and Iran, understand Level 0 cyber deficiencies. In sharp contrast, most cyber defenders do not and won’t identify process sensor incidents as being cyber-related. This gap helps explain why process sensor cybersecurity remains largely absent from OT security forums and RSA Conference discussions. It may also explain why government OT cybersecurity advisories don’t include insecure Level 0 devices, even though process sensors provide the trusted input to controllers and SCADA/DCS systems.
Conclusions:
Network cybersecurity functions across IT and OT domains, and control system engineering organizations, operate with fundamentally different objectives, taxonomies, and thresholds for identifying and classifying cyber incidents. This divergence has led to a persistent disconnect in how incidents affecting control systems are recognized and addressed within broader network security governance frameworks. Dismissing control system cyber events because they fall outside narrow, IT-centric definitions is not merely a semantic issue—it reflects a structural governance gap with direct implications for critical infrastructure resilience.
To address this, industry and government stakeholders must converge on a harmonized definition of cyber incidents that encompasses both network-centric and control system–centric perspectives. This alignment should be supported by cross-domain training, ensuring that both network security practitioners and engineering teams possess sufficient understanding of control system architectures, threat models, and failure modes. Without such integration, efforts to compare incident frequency, severity, and systemic impact across IT networks and control systems will remain inconsistent and misleading. More critically, this fragmentation will continue to obscure systemic risk, leaving essential infrastructure sectors exposed to increasingly sophisticated and multi-domain cyber threats.
About Joe Weiss:

Joe Weiss is an expert on control system cyber security. He authored the 2010 book, “Protecting Industrial Control Systems from Electronic Threats.”
Joe is an ISA Fellow, Emeritus Managing Director of ISA99, an IEEE Senior Member, has patents on instrumentation, control systems, and OT networks. He is a professional engineer with CISM and CRISC certifications and is a member of Control Process Automation Hall of Fame.
References:
https://www.paloaltonetworks.com/resources/research/state-of-ot-security-report
OT Cybersecurity: The Guide to Securing Industrial Systems
Verizon Business sees escalating risks in mobile and IoT security
Anthropic’s Project Glasswing aims to reshape IT cybersecurity
Emerging Cybersecurity Risks in Modern Manufacturing Factory Networks
Cybersecurity threats in telecoms require protection of network infrastructure and availability
StrandConsult Analysis: European Commission second 5G Cybersecurity Toolbox report
IEEE/SCU SoE Virtual Event: May 26, 2022- Critical Cybersecurity Issues for Cellular Networks (3G/4G, 5G), IoT, and Cloud Resident Data Centers
Cisco CEO sees great potential in AI data center connectivity, silicon, optics, and optical systems
It’s no surprise to IEEE Techblog readers that Cisco’s networking business – still its biggest unit, generating nearly half its total sales – reported <$6.9 billion in revenue for the three-month period ending in January (Cisco’s second fiscal quarter). That was down 3% compared with the same quarter the year before. For its first half year, networking sales dropped 14% year-over-year, to about $13.6 billion.
However, total second-quarter revenues grew 9% year-over-year, to just less than $14 billion, boosted by the Splunk (security company) acquisition in March 2024. Thanks to that deal, Cisco’s security revenues more than doubled for the first half, to about $4.1 billion. But net income fell 8%, to roughly $2.4 billion, due partly to higher costs for research and development, as well as sales and marketing expenses.
Cisco groused about an “inventory correction” as networking customers digested stock they had already bought, but that surely is not the case now as that inventory has been worked off by its customers (ISPs, telcos, enterprise & government end users). Cisco CFO Richard Scott Herren now says “The demand that we’re seeing today a function of extended lead times like we saw a couple of years ago. That’s not the case. Our lead times are not extending.”
Currently, Cisco firmly believes that Ethernet connectivity sales to owners of AI data centers is an “emerging opportunity.” That refers to Cisco’s data center switching solutions for “web-scale” and enterprise customer intra-data center communications. The company’s AI strategy is described here.

Image Courtesy of Cisco Systems
………………………………………………………………………………………………………………………………………
AI investments “will lead to our networking equipment being combined with Nvidia GPUs, and that’s how we’ll accomplish that in the future,” CEO Chuck Robbins told industry analysts on a call to discuss second-quarter results, according to a Motley Fool transcript. “There’s so much change going on right now from a technology perspective that there’s both excitement about the opportunity, and candidly, there’s a little bit of fear of slowing down too much and letting your competition get too much ahead of you. So, we saw solid demand,” he said.
However, Cisco will face mighty competition in that space.
- Nokia is targeting the same opportunity and last month said it would spend an additional €100 million (US$104 million) on its Internet Protocol unit annually with the goal of generating another €1 billion ($1.04 billion) in data center revenues by 2028.
- Arista Networks is another rival in this market, selling high performance Ethernet switches to cloud service providers like Microsoft.
- Nvidia, whose $7 billion acquisition of Mellanox in 2019 gave it effective control of InfiniBand, an alternative to Ethernet that had represented the main option for connecting GPU clusters when analysts published research on the topic in August 2023. Just as important, the Mellanox division of Nvidia also is a leader in Ethernet connectivity within data centers as described in this IEEE Techblog post.
- Juniper Networks (being acquired by HPC) is also focusing on networking the AI data center as per a white paper you can download after filling out this form.
During the Q & A, Robbins elaborated: “On the $700 million in AI orders, it’s a combination of systems, silicon, optics, and optical systems. And I think if you break it down, it’s about half is in silicon and systems. And it continues to accelerate. And I’d say the teams have done a great job on the silicon front. We’ve invested heavily in more resources there. The team is running parallel development efforts for multiple chips that are staggered in their time frames. They’ve worked hard. They were increasing the yield, which is a positive thing. And so, we feel good about it, but it’s a combination of all those things that we’re selling to the customers.”
…………………………………………………………………………………………………………………………………………………………………………………………
Enterprise AI:
“What we’re seeing on the enterprise side relative to AI is it’s still — customers are still in the very early days, and they all realize they need to figure out exactly what their use cases are. We’re starting to see some spending though on specific AI-driven infrastructure. And we think as we get AI pods out there — we got Hyperfabric coming. We got AI defense coming.
We have Hypershield in the market. And we got this new DPU switch, they are all going to be a part of the infrastructure to support these AI applications. So, we’re beginning to see it happen, but I think it’s also really important to understand that as the enterprises leverage their private data, their proprietary data, and they’ll do some training on that and then they’ll run inference obviously against that. We believe that opportunity is an order of magnitude higher than what we’ve seen in training today. We’re going to continue to innovate and build capabilities to put ourselves in a better position to be a real beneficiary as this continues to accelerate. But as of today, we feel like we’re in pretty good shape.”
“If you look at AI defense with the AI Summit that we did recently, there’s — I think there’s about 20-some-odd customers who are interested in going to proof of concept with us right now on it. We had almost half the Fortune 100 there for that event. So, I feel good about where we are. It will turn into greater demand as we just continue to scale these products.”
Telco use of AI Edge Applications:
“We see some of the European network operators are looking at delivering AI as a service,” said Robbins. “We see a lot of them planning for AI edge applications that are sitting at the edge of their networks that they’re managing for customers.”
,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,………………………………………………
Cisco raised its guidance and now expects revenues for the full year of between $56 billion and $56.5 billion, up from its earlier range of $55.3 billion to $56.3 billion.
,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,,………………………………………………
References:
https://www.cisco.com/site/uk/en/solutions/artificial-intelligence/index.html
https://www.juniper.net/content/dam/www/assets/white-papers/us/en/networking-the-ai-data-center.pdf
Nokia selects Intel’s Justin Hotard as new CEO to increase growth in IP networking and data center connections
Initiatives and Analysis: Nokia focuses on data centers as its top growth market
Nvidia enters Data Center Ethernet market with its Spectrum-X networking platform
Aftermath of Salt Typhoon cyberattack: How to secure U.S. telecom networks?
Salt Typhoon Attack: On December 4, 2024, a top U.S. security agency representative confirmed reports that foreign actors, state-sponsored by the People’s Republic of China, infiltrated at least eight U.S. communications companies, compromising sensitive systems and exposing vulnerabilities in critical telecommunications infrastructure. This was part of a massive espionage campaign that has affected dozens of countries. Salt Typhoon has targeted telcos in dozens of countries for upward of two years, officials added.
Dated legacy network equipment and years of mergers and acquisitions are likely impeding the ability of telecommunications providers to prevent China inspired cyber-attacks. Until telecom operators fully secure their networks, China will keep finding ways to come back in, officials have warned.
- On Thursday, FCC chair Jessica Rosenworcel proposed a new annual certification requirement for telecom companies to prove they have an up-to-date cybersecurity risk management plan. More below.
- Senior Cybersecurity and Infrastructure Security Agency and FBI officials confirmed Tuesday that U.S. telcos are still struggling to keep the China-backed hackers out of their networks — and they have no timeline for when total eviction is possible.
FCC Chair Jessica Rosenworcel suggested ‘telecom carriers’ raise their network security methods and procedures: “The cybersecurity of our nation’s communications critical infrastructure is essential to promoting national security, public safety, and economic security,” said Rosenworcel. “As technology continues to advance, so does the capabilities of adversaries, which means the U.S. must adapt and reinforce our defenses. “While the Commission’s counterparts in the intelligence community are determining the scope and impact of the Salt Typhoon attack, we need to put in place a modern framework to help companies secure their networks and better prevent and respond to cyberattacks in the future.”
Rosenworcel’s plan is to make U.S. telcos submit some kind of annual certification to the FCC, proving their cybersecurity measures are up to scratch. The clear inference from the attack itself and all the subsequent attempts to shut the stable door after the horse has bolted is that those efforts currently fall short of the mark. Understandably, none of the specific deficiencies have been publicly detailed.
These proposed FCC measures have been made available to the five members of the Commission. They may choose to vote on them at any moment. If adopted, the Declaratory Ruling would take effect immediately. The Notice of Proposed Rulemaking, if adopted, would open for public comment the cybersecurity compliance framework, which is part of a broader effort to secure the nation’s communications infrastructure.
The FCC press release refers to a recent WSJ report based on an unpublished briefing from U.S. national security adviser Anne Neuberger, in which she detailed the scale of the Salt Typhoon attack. “The Chinese compromised private companies, exploiting vulnerabilities in their systems as part of a global Chinese campaign that’s affected dozens of countries around the world,” she was quoted as saying.
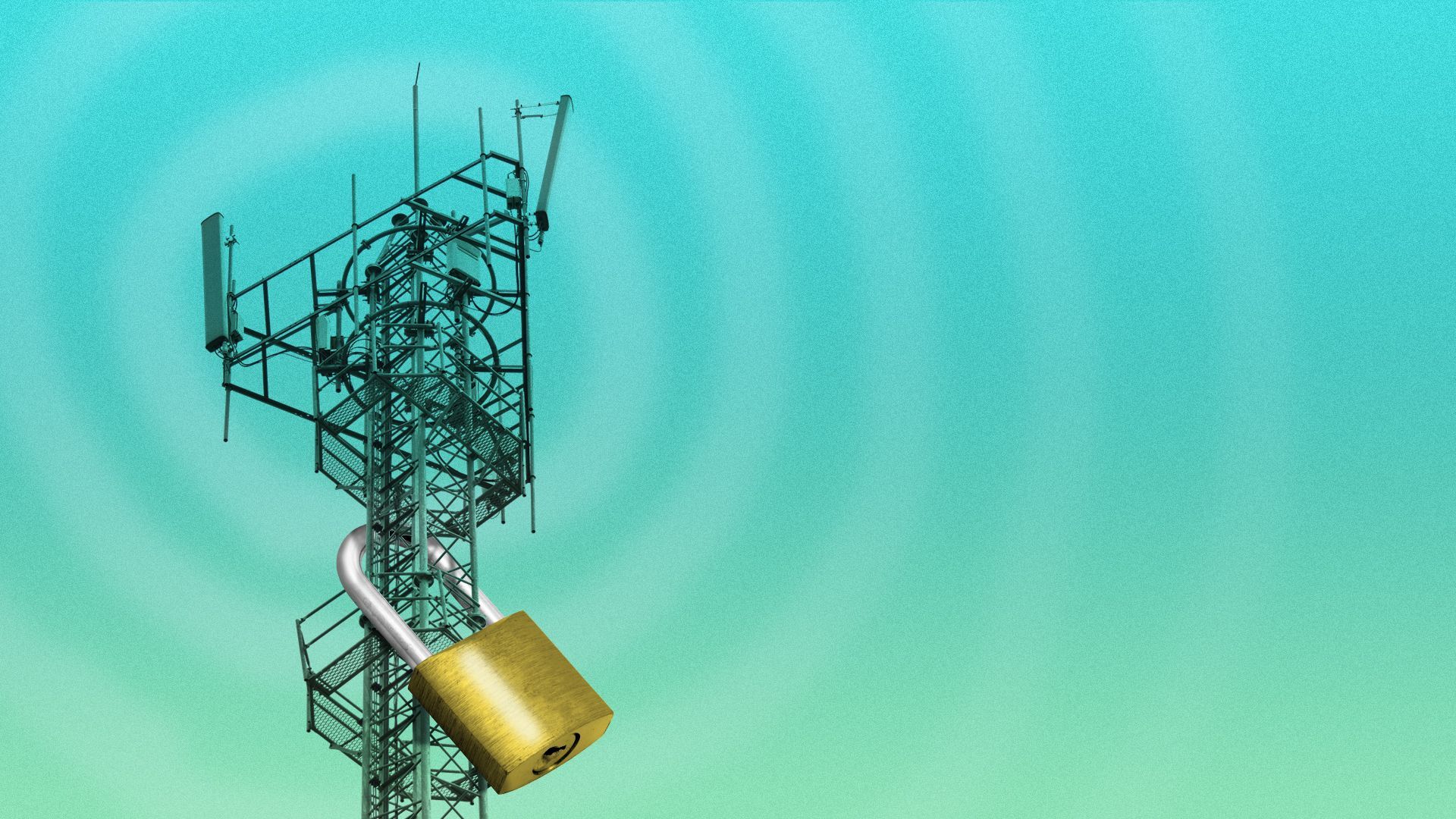
Illustration: Sarah Grillo/Axios
……………………………………………………………………………………………………………………………
Legacy network equipment and years of acquisitions have made it particularly difficult for telcos to patch every access point on their networks, Cliff Steinhauer, director of information security and engagement at the National Cybersecurity Alliance, told Axios.
- Many of the systems in question are nearly 50 years old — like landline systems — and they were “never meant for the type of sensitive data and reliance that we have on them right now,” he said.
- During an acquisition, a company could also miss a server when taking stock of all its newly acquired equipment, Steinhauer said. Network engineers are often inundated with security alerts that are hard to prioritize, he added.
- U.S. telecommunications carriers are required to provide a way for law enforcement to wiretap calls as needed — providing another entry point for adversaries.
Many of the security problems telcos face require simple fixes, like implementing multifactor authentication or maintaining activity logs.
- Even CISA’s recent guidance for securing networks focuses on the security basics.
- But to keep China out, telcos would have to make sure that every device — including their legacy physical equipment, online servers and employees’ computers — is patched.
Most high-profile cyberattacks across industries come down to the basics: a compute server that didn’t have multifactor authentication turned on or an employee who was tricked into sharing their password. Even if a company invests all of its resources in cybersecurity, it may not be enough to fend off a sophisticated nation-state like China.
- These actors are skilled at covering their tracks: They could delete activity logs, pose as legitimate users, and route their traffic through compromised computers in the U.S. so they aren’t detected.
- “You’ve got a persistent, motivated attacker with vast resources to poke and prod until they get in,” Mr. Steinhauer said.
References:
https://docs.fcc.gov/public/attachments/DOC-408015A1.pdf
https://www.axios.com/2024/12/06/telecom-cybersecurity-china-hack-us
WSJ: T-Mobile hacked by cyber-espionage group linked to Chinese Intelligence agency
WSJ: T-Mobile hacked by cyber-espionage group linked to Chinese Intelligence agency
According to the Wall Street Journal, T-Mobile’s network was hacked in a damaging Chinese cyber-espionage operation that successfully gained entry into multiple U.S. and international telecommunications companies.
Hackers linked to a Chinese intelligence agency were able to breach T-Mobile as part of monthslong campaign to spy on the cellphone communications of high-value intelligence targets. It is unclear what information, if any, was taken about T-Mobile customers’ calls and communications records.
“T-Mobile is closely monitoring this industry-wide attack, and at this time, T-Mobile systems and data have not been impacted in any significant way, and we have no evidence of impacts to customer information,” a company spokeswoman said. “We will continue to monitor this closely, working with industry peers and the relevant authorities.”
China’s multipronged spying operations have drawn warnings in the U.S. about their economic implications. Photo: Andy Wong/Associated Press
…………………………………………………………………………………………………………………………………………………………………………..
Salt Typhoon used sophisticated methods to infiltrate American telecom infrastructure through vulnerabilities including Cisco Systems routers, and investigators suspect the hackers relied on artificial intelligence or machine learning to further their espionage operations , people familiar with the matter said. The attackers penetrated at least some of that infrastructure over eight months or more.
In the broader hacking campaign, attackers were able to access cellphone lines used by an array of senior national security and policy officials across the U.S. government, in addition to politicians. The access allowed them to scoop up call logs, unencrypted texts and some audio from targets, in what investigators believe may have significant national-security ramifications.
Additionally, the hackers were able to access information from systems maintained by the carriers to comply with U.S. surveillance requests, raising further counterintelligence concerns. Investigators are still endeavoring to fully understand and have said the attack was carried out by the Salt Typhoon group. At Lumen, which doesn’t provide wireless service, the attackers didn’t steal any customer data or access its wiretap capabilities, according to people familiar with the matter.
Further investigation has revealed that the hackers sought access to data managed under U.S. law enforcement programs, including those governed by the Foreign Intelligence Surveillance Act (FISA). This act authorizes American intelligence agencies to monitor suspected foreign agents’ communications. By targeting these programs, Chinese hackers may have aimed to infiltrate sensitive government communications channels, gaining insights into U.S. surveillance efforts.
Some foreign telecommunications firms were also compromised in the hacks, including in countries that maintain close intelligence-sharing partnerships with the U.S., people familiar with the matter said. Earlier this week, the Biden administration acknowledged in a public statement some details about the nature of the “broad and significant” hack that were previously reported by the WSJ.
Chinese government-linked hackers had compromised networks at multiple telecommunications companies “to enable the theft of customer call records data, the compromise of private communications of a limited number of individuals who are primarily involved in government or political activity, and the copying of certain information that was subject to U.S. law enforcement requests pursuant to court orders,” the statement from the FBI and Cybersecurity and Infrastructure Security Agency (CISA) said. “We expect our understanding of these compromises to grow as the investigation continues,” they added.
References:
https://www.wsj.com/tech/cybersecurity/u-s-wiretap-systems-targeted-in-china-linked-hack-327fc63b
https://www.newsweek.com/fbi-chinese-cyber-espionage-multiple-telecom-networks-1985617
China backed Volt Typhoon has “pre-positioned” malware to disrupt U.S. critical infrastructure networks “on a scale greater than ever before”
FBI and MI5 Chiefs Issue Joint Warning: Chinese Cyber Espionage on Tech & Telecom Firms
Cybersecurity threats in telecoms require protection of network infrastructure and availability
FT: A global satellite blackout is a real threat; how to counter a cyber-attack?
Demythifying Cyber security: IEEE ComSocSCV April 19th Meeting Summary
StrandConsult Analysis: European Commission second 5G Cybersecurity Toolbox report
Cisco to lay off more than 4,000 as it shifts focus to AI and Cybersecurity
Frontier Communications recovering from unknown cyberattack!
Frontier Communications provides fiber optic based gigabit Internet access to millions of consumers and businesses across 25 states. Frontier Communications said on Thursday that it’s ‘experiencing technical issues with our internal support platforms.’ Frontier’s mobile apps are also down, with the same warning message being displayed after launching the application. A company representative did not respond to questions about the situation.
The Texas-based telecommunications company reported a cyberattack to the Securities and Exchange Commission (SEC) on Thursday. Frontier said it detected unauthorized access to its IT systems on April 14th and began instituting “containment measures” that included “shutting down certain of the Company’s systems.” The shutdowns caused operational disruption that the company said “could be considered material.”
“Based on the Company’s investigation, it has determined that the third party was likely a cybercrime group, which gained access to, among other information, personally identifiable information,” the company said in the SEC filing.
“As of the date of this filing, the Company believes it has contained the incident and has restored its core information technology environment and is in the process of restoring normal business operations. Based on the company’s investigation, it has determined that the third party was likely a cybercrime group, which gained access to, among other information, personally identifiable information,” the company said.

Investigations into the incident are ongoing and they have hired cybersecurity experts to help with the incident. Law enforcement agencies have been notified.
Despite saying that the shutdowns could be considered material, Frontier later wrote that it “does not believe the incident is reasonably likely to materially impact the Company’s financial condition or results of operations.”
According to Leichtman Research Group, Frontier is the seventh largest broadband Internet supplier in the US, with almost 3 million customers. The company’s copper and fiber network stretches across large portions of the East and West Coasts.
Light Reading reported on Thursday of warnings from Frontier. “We’re experiencing technical issues with our internal support platforms,” said a message on the company’s website homepage. “Our residential and business networks are not affected by this issue. In the meantime, please call for assistance.”
……………………………………………………………………………………………………………………………
Last week, AT&T reported that more than 51 million people were affected by a recently-disclosed data breach that included troves of customer information including Social Security numbers, AT&T account numbers and AT&T passcodes.
EchoStar’s Dish Network last year reported a “cybersecurity incident” that impacted its ability to install services, take payments and provide customer care for several weeks.
Fierce reported this week about an intentional cable cut in AT&T’s network that interrupted services at Sacramento Airport.
……………………………………………………………………………………………………………………..
The Federal Communications Commission (FCC) updated its data breach rules for the first time in 16 years in December, expanding regulations on how telecommunication companies report cybersecurity incidents. FCC Chairwoman Jessica Rosenworcel argued that the rules the agency created more than 15 years ago are no longer compatible with a modern world where telecommunication carriers have access to a “treasure trove of data about who we are, where we have traveled, and who we have talked to.”
References:
https://therecord.media/telecom-giant-frontier-cyberattack-sec
https://www.sec.gov/ix?doc=/Archives/edgar/data/20520/000119312524100764/d784189d8k.htm
https://www.lightreading.com/security/frontier-we-were-probably-hacked
China backed Volt Typhoon has “pre-positioned” malware to disrupt U.S. critical infrastructure networks “on a scale greater than ever before”
On Sunday, FBI Director Christopher Wray said Beijing’s efforts to covertly plant offensive malware inside U.S. critical infrastructure networks [1.] is now at “a scale greater than we’d seen before,” an issue he has deemed a defining national security threat. He said that China backed Volt Typhoon was pre-positioning malware that could be triggered at any moment to disrupt U.S. critical infrastructure. “It’s the tip of the iceberg…it’s one of many such efforts by the Chinese,” he said on the sidelines of the security conference.
Wray had earlier told conference delegates, that China was increasingly inserting “offensive weapons within our critical infrastructure poised to attack whenever Beijing decides the time is right.” The FBI chief said the U.S. is particularly focused on the threat of pre-positioning, which some European officials have described as the cyber equivalent of pointing a ballistic missile at critical infrastructure. “Those attacks are now being amplified by artificial intelligence tools. The word ‘force multiplier’ is not really enough,” Wray added.
Note 1. The FBI Director declined to elaborate on what other critical infrastructure had been targeted, stressing that the Bureau had “a lot of work under way.”

Image Credits: imaginima / Getty Images
Machine learning translation has helped Chinese security operatives to more plausibly recruit assets, steal secrets and rapidly process more of the information they are collecting, the Wray said. “They already have built economic espionage and theft of personal and corporate data as a kind of a bedrock of their economic strategy and are eagerly pursuing AI advancements to try to accelerate that process,” Wray added.
FBI Director Christopher Wray PHOTO: KEVIN DIETSCH/GETTY IMAGES
……………………………………………………………………………………………………………………………
Western intelligence officials say China’s scale and sophistication of cyberattacks has accelerated over the past decade. Officials have grown particularly alarmed at Beijing’s interest in infiltrating U.S. critical infrastructure networks, planting malware inside U.S. computer systems responsible for everything from safe drinking water to aviation traffic so it could detonate, at a moment’s notice, damaging cyberattacks during a conflict.
In California, Wray met with counterparts from the Five Eyes intelligence community—which encompasses the U.S., Australia, New Zealand, Canada and the U.K.—to share respective strategies for cyber defense. He has also traveled to Malaysia and India to discuss China’s hacking campaign with authorities in both countries.
“I am seeing more from Europe,” he said. “We’re laser focused on this as a real threat and we’re working with a lot of partners to try to identify it, anticipate it and disrupt it.”
The Netherlands’ spy agencies said earlier this month that Chinese hackers had used malware to gain access to a Dutch military network last year. The agency, considered to have one of Europe’s top cyber capabilities, said it made the rare disclosure to show the scale of the threat and reduce the stigma of being targeted so allied governments can better pool knowledge.
A report released this month by agencies including the FBI, the Cybersecurity and Infrastructure Agency and the National Security Agency said Volt Typhoon hackers had maintained access in some U.S. networks for five or more years, and while it targeted only U.S. infrastructure directly, the infiltration was likely to have affected “Five Eyes” allies.
Author’s Note:
……………………………………………………………………………………………………………………………
Volt Typhoon, the China-sponsored hacking group, has been targeting U.S. critical infrastructure, including satellite and emergency management services and electric utilities, according to a new report from the industrial cybersecurity firm Dragos. That report outlines how the notorious hacking group is positioning themselves to have disruptive or destructive impacts on critical infrastructure in the U.S.
Robert M. Lee, founder and CEO of Dragos, warned during a media briefing that Volt Typhoon is not an opportunistic group, but is instead targeting specific sites that assist U.S. adversaries “trying to hurt or cripple U.S. infrastructure. It’s hitting the specific electric and satellite communication providers that would be important for disrupting major portions of the U.S. electric infrastructure,” Lee added.
The report comes shortly after the National Security Agency, FBI, and Cybersecurity and Infrastructure Security Agency, revealed that Volt Typhoon has been in some critical infrastructure networks for at least five years. That alert warned of Volt Typhoon operations that targeted the aviation, railways, mass transit, highway, maritime, pipeline, and water and sewage sectors.
……………………………………………………………………………………………………………………………………………………………………………………………………………………………………
The NSA, CISA and FBI said in a joint advisory report that Volt Typhoon has been burrowing into the networks of aviation, rail, mass transit, highway, maritime, pipeline, water and sewage organizations — none of which were named — in a bid to pre-position themselves for destructive cyberattacks, published on February 7th. The release of the advisory, which was co-signed by cybersecurity agencies in the United Kingdom, Australia, Canada and New Zealand, comes a week after a similar warning from FBI Director Christopher Wray. Speaking during a U.S. House of Representatives committee hearing on cyber threats posed by China, Wray described Volt Typhoon as “the defining threat of our generation” and said the group’s aim is to “disrupt our military’s ability to mobilize” in the early stages of an anticipated conflict over Taiwan, which China claims as its territory.
According to Wednesday’s technical advisory, Volt Typhoon has been exploiting vulnerabilities in routers, firewalls and VPNs to gain initial access to critical infrastructure across the country. The China-backed hackers typically leveraged stolen administrator credentials to maintain access to these systems, according to the advisory, and in some cases, they have maintained access for “at least five years.”
This access enabled the state-backed hackers to carry out potential disruptions such as “manipulating heating, ventilation, and air conditioning (HVAC) systems in server rooms or disrupting critical energy and water controls, leading to significant infrastructure failures,” the advisory warned. In some cases, Volt Typhoon hackers had the capability to access camera surveillance systems at critical infrastructure facilities — though it’s not clear if they did.
Volt Typhoon also used living-off-the-land techniques, whereby attackers use legitimate tools and features already present in the target system, to maintain long-term, undiscovered persistence. The hackers also conducted “extensive pre-compromise reconnaissance” in a bid to avoid detection. “For example, in some instances, Volt Typhoon actors may have abstained from using compromised credentials outside of normal working hours to avoid triggering security alerts on abnormal account activities,” the advisory said.
Earlier this year, the FBI and U.S. Department of Justice announced that they had disrupted the “KV Botnet” run by Volt Typhoon that had compromised hundreds of U.S.-based routers for small businesses and home offices. The FBI said it was able to remove the malware from the hijacked routers and sever their connection to the Chinese state-sponsored hackers.
According to a May 2023 report published by Microsoft, Volt Typhoon has been targeting and breaching U.S. critical infrastructure since at least mid-2021.
……………………………………………………………………………………………………………………………………………………………………………………………………………………………..
References:
Volt Typhoon targeted emergency management services, per report
US disrupts China-backed hacking operation amid warning of threat to American infrastructure
https://www.controlglobal.com/home/blog/11293192/information-technology
StrandConsult Analysis: European Commission second 5G Cybersecurity Toolbox report
by John Strand, StandConsult (edited by Alan J Weissberger)
European Commissioner Thierry Breton presented the European Commission’s plan for banning High-Risk Suppliers like Huawei and ZTE from European telecommunications networks. Here is the first portion:
The security of 5G networks is essential. They are critical infrastructures in their own right and for other sectors that depend on them, such as energy, transport, health and finance.
This is why, in January 2020, the EU unanimously adopted a toolbox on the security of 5G networks. The “5G cybersecurity toolbox” defined the risks and the measures to be taken by Member States and telecoms operators to address them.
In particular, it recommended that the use of equipment in the core and access (RAN) parts of the networks should be restricted or prohibited for entities considered to be “high-risk suppliers”, notably because they are subject to highly intrusive third-country laws on national intelligence and data security.
3 years on, almost all Member States have transposed the toolkit’s recommendations into their national law. In other words, they can now decide to restrict or exclude suppliers on the basis of security risk analysis. But to date, only 10 of them have used these prerogatives to restrict or exclude high-risk vendors.
……………………………………………………………………………………………………………………………………………..
The Commission also released a status report on “Member States’ Progress in implementing the EU Toolbox on 5G Cybersecurity.”
Breton’s message is that the member must move more quickly to implement the 5G toolbox.
Here are Breton’s key points with Strand Consult’s assessment (SC):
- All EU member states are committed to implementing the EU´s 5G Toolbox. To date, 24 Member States have adopted or are preparing legislative measures giving national authorities the powers to perform an assessment of suppliers and issue restrictions.
- SC: This means that all EU countries support the 5G Toolbox, the implement of which will work to remove Huawei and ZTE from European networks.
- 10 Member States have imposed such restrictions, and an additional 3 Member States have relevant national legislation underway.
- SC: This is a significant improvement compared to a few months ago when Strand Consult’s released its report The Market for 5G RAN in Europe: Share of Chinese and Non-Chinese Vendors in 31 European Countries. Given the Commission’s communication we the remaining more operators in 14 countries to move more expeditiously to remove Huawei and ZTE equipment.
- The Commission considers that decisions adopted by Member States to restrict or exclude Huawei and ZTE from 5G networks are justified and compliant with the 5G Toolbox.
- SC: This statement is very important to support the member states where Huawei and China attempt to thwart the implementation of the toolbox. China has made unseemly threats in certain members states. Now these states have meaningful European Commission support. For example, in December 2019, Wu Ken, the Chinese ambassador to Germany, was quoted as threatening the German auto manufacturing industry that access to the Chinese market could be restricted should Chinese Huawei be excluded from participating in contracts to build Germany’s 5G networks. The statement dampened Germany’s enthusiasm for opening its EU toolbox and examining its requirements.
- The Commission will take measures to avoid conducting its official communications via mobile networks built with Huawei and ZTE equipment.
- SC: If an EU mobile operator uses Huawei or ZTE equipment in its 5G network, the European Commission will not do business with that operator. In practice EU operators which use Huawei and ZTE will be labeled as “non-trusted operators.” This will likely accelerate the exodus of corporate customers from European operators which don’t want to conduct their business on Chinese networks. Strand Consult described this in its 2019 research note The pressure to restrict Huawei from telecom networks is driven not by governments, but the many companies which have experienced hacking, IP theft, or espionage. This is a needed and important step from the Commission.
- The Commission also intends to reflect this decision in all relevant EU funding programs and instruments.
- SC: The EU will further restrict grants, subsidies, and financing to European entities which use Huawei and ZTE equipment. This will have consequences for rural EU operators which receive EU money and recipients of European Investment Bank (EIB) loans.
Strand Consult is not surprised by today’s announcements. They are consistent with the security analyses and recommendations Strand Consult has published for years.
Some EU countries and operators will find it difficult to implement the EU’s new security and procurement policy. However Strand Consult believes that it is good business for an operator communication that it takes security seriously and backs it up with a clean network free of Huawei and ZTE equipment.
Strand Consult predicts that Huawei will make the road ahead difficult and will attempt to sabotage the European Commission’s efforts. Nations and operators should prepare for pushback by reading Strand Consult’s reports on Huawei’s tactics. Moreover, non-Chinese employees will likely find that working for Huawei has reputational risks.
How foreign network equipment is treated in China.
The foundation of any economy, be it the EU, the US or China, is national security. Some may find the EU approach tough, but it pales in comparison the blockade that China has imposed on foreign technology providers for years.
China restricts these technologies for ideological and economic reasons. Most people take for granted that the websites and media they access everyday are not available in China. These foreign technologies and their operators have been denied access to the world’s single largest online market, hundreds of millions of internet users, and a multi-trillion-dollar opportunity. Moreover, the Chinese people are denied to freedom to engage on an open internet.
Building upon censorship frameworks in traditional media which had been in place for decades in China, its State Council adopted rules and regulations to control internet traffic beginning in 1996.
The media focuses mainly on US and EU network security and associated vendor policies. However few if any investigate the rules in China.
A detailed review is available from White & Chase, February 2022. In general, China’s rules are significantly more rigid than those of the US and EU. These rules do not entail the same process and transparency which are standard and expected in the West.
The New Measures list the following main factors for assessing national security risk during cybersecurity review.
- The risk of any critical information infrastructure being illegally controlled, tampered with or sabotaged after any product or service is used.
- The risk of an interruption in the supply of any product or service endangering the continuity of any critical information infrastructure.
- The security, openness, transparency, diversity of sources and reliability of any supply channel of any product or service, and the risk of its supply being interrupted due to political, diplomatic, trade or other factors.
- The compliance of the provider of any product or service with the laws, administrative regulations, and departmental rules of China.
- The risk of any core data, important data or a large amount of personal information being stolen, leaked, destroyed, illegally used, or illegally transferred abroad.
- The risk of any critical information infrastructure, core data, important data, or a large amount of personal information being affected, controlled, or maliciously used by foreign governments, as well as any network information security risk.
- Any other factor that may endanger the security of any critical information infrastructure, network security or data security.
The effect of these rules is to limit foreign providers from the market from the start and to favor Chinese providers.
While the media sensationalizes cases like Huawei and TikTok, these pale in comparison to the systematic restriction undertaken by China against foreign technology for the last 20 years. Moreover, Chinese technology companies enjoy more freedom abroad than foreign technologies do in China.
Conclusions:
Technological and informational control and restriction are widely practiced across China. This fulfills many political, social, cultural, economic, and religious objectives for the PRC,and is practiced by the government, corporations, and individual themselves. It has increased under General Secretary Xi. This Censorship is coupled with pervasive surveillance of people. Meanwhile PRC has attempted to export this “new world media order.”
Strand Consult addresses Chinas restrictions in its 2020 report You Are Not Welcome: An Analysis of Thousands Foreign Technology Companies Blocked by China Since 1996. It describes how and why China has systematically restricted thousands of foreign internet technologies like online news and media outlets, social media platforms, virtual private networks, content delivery networks, mobile applications, telecommunications equipment, cloud services, and other technologies.
With its new 2023 report The Market for 5G RAN in Europe: Share of Chinese and Non-Chinese Vendors in 31 European Countries, Strand Consult brings valuable evidence of the location, amount, and share of Chinese and non-Chinese equipment in European telecom networks. This report, the second of its kind, describes the respective amounts of 5G equipment from Huawei, ZTE, and non-Chinese vendors in European mobile networks and the share of such in equipment in the 5G Radio Access Network (RAN).
References:
https://ec.europa.eu/commission/presscorner/detail/en/statement_23_3312
StrandConsult: 2022 Year in Review & 2023 Outlook for Telecom Industry
IEEE ComSoc/SCU SoE March 22, 2022 event: OpenRAN and Private 5G – New Opportunities and Challenges. Video: https://www.youtube.com/watch?v=i7QUyhjxpzE
Strand Consult: Open RAN hype vs reality leaves many questions unanswered
O-RAN Alliance tries to allay concerns; Strand Consult disagrees!
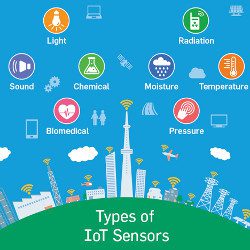
IoT Sensor Standards Are Absolutely Essential for Security
By Logan Kugler (edited by Alan J Weissberger)
Companies making and using IoT sensors can have a high degree of confidence their technology uses the best security features and practices if they adhere to established, credible security standards. There are plenty of security standards that IoT devices can—or should—follow. Some are related to how IoT devices use networks and transmit data. Some are related to the underlying technologies IoT devices rely upon (such as Wi-Fi). Others offer comprehensive guidance on how to create and use IoT devices in a secure way.
One well-known IoT standard is ISO/IEC 30141 which “provides a standardized IoT Reference Architecture using a common vocabulary, reusable designs, and industry best practices.” Another IoT standard, TS 103645 from ETSI aims to create a security baseline for Web-connected devices, including guidelines for password usage, software updates, and user data standards for consumer IoT devices.
In another example, the U.S. National Institute of Standards and Technology (NIST) has created a list of six prescribed security characteristics that manufacturers should incorporate into IoT devices. The list includes security features such as device identification, device configuration features, data protection features, logical access to interfaces, adequate software and firmware updates, and adequate cybersecurity event logging.
There are dozens of organizations that publish helpful standards to guide IoT manufacturers and device customers on how to design, manufacture, and use IoT sensors and sensor-enabled devices in the safest way possible. However, the diversity of organizations and standards also presents problems.
Some standards organizations may aim to publish universal standards across different IoT technologies, while others may only publish standards for certain countries or devices and technologies. While these organizations are usually highly credible and undergo rigorous processes to ensure their standards are comprehensive, many such standards are not legally binding. However, there is no single, well accepted standard for IoT security. The existing standards are not always designed for the unique risks IoT technologies face, says Izzat Alsmadi, a computer science professor at Texas A&M University in San Antonio, who does work on IoT security. Existing standards may not adequately apply to significant numbers of IoT sensors, he explained, and some IoT devices and networks use proprietary technology that does not follow more widely accepted or used industry standards.
“Today’s IoT standards are relevant, but not enough and in some cases not up to date or not up to security challenges,” says Alsmadi. That’s because some of today’s existing security mechanisms were initially designed for desktop computers and are difficult to implement on resource-constrained IoT devices, he says. There also is the problem of compliance. Standards are often voluntary—and many companies do not adhere to them due to business pressures.
“Currently, the IoT segment sacrifices security due to resource allocation and price,” says Marion Marincat, founder and CEO of Mumbli, an IoT company. It is often faster and cheaper to limit security options in order to get to market, he says. As such, the standards for IoT mainly end up being adopted by the companies with deep-enough pockets and wide-enough competitive moats to afford to implement better security in their devices.
“Although there are a lot of methods to design low-cost devices with security in mind, business decisions usually push back the implementation for these solutions in order to speed up the route to market or reduce the price of devices even further,” says Marincat.
The issues with IoT sensor standards have larger implications for the overall security of the Internet of Things.
“The Internet of Things is very vulnerable in comparison with other categories of information systems,” says Alsmadi, because so many IoT applications are publicly visible and can be remotely controlled.
These vulnerabilities become even more pronounced as the adoption of IoT grows, especially as the industrial Internet of Things becomes a growing attack vector.
“The biggest change in operational technology systems over the past decade is that they have recently become more vulnerable to attacks from the outside as they are moving away from isolated, air-gapped environments and embracing more automation and digitally connected devices and systems,” says Fortinet’s Nelson.
Industrial IoT devices often run on hardware with little or no management interface and often are not able to be upgraded in the field. Physically, IoT devices in industrial use-cases frequently are installed in hard-to-reach or publicly inaccessible places (such as on top of a building). As such, they must be able to operate unattended for long periods and be resistant to physical tampering, he says.
“An attack on industrial IoT, especially on a device or system used to monitor critical operations and processes, can have a very significant impact on not only the business itself but also on the environment, even on the health and safety of staff and the public at large,” Nelson says.
Marincat advocates rolling out minimum standards to broad categories of IoT devices, but acknowledges many manufacturers will still see complying with such standards as a luxury in a competitive marketplace.
However, even with smarter standards approaches, making security updates to combined IoT software/hardware can be slower and more complicated than bug fixes and security updates for software alone. One possible fix is having companies adopt smarter risk-mitigation policies in how they use IoT devices, says Nelson. Companies should consider employing a zero-trust access (ZTA) model that verifies users and devices before every application session. “Zero-trust access confirms that users and devices meet the organization’s policy to access that application and dramatically improves the organization’s overall risk posture,” he says.
Nelson also recommends companies use micro-segmentation in their networks. This approach segments and isolates attack surfaces into specific zones. Data flows are then controlled into these zones. The result is companies can limit attacks to a small subset of the business, minimizing the chance bad actors move laterally through networks into other core business functions.
Even basic risk mitigation techniques can help. Other popular risk mitigation techniques employed by businesses include encrypting internet connections, using alternate networks in addition to primary ones, and investing in higher-quality (and more costly) devices from companies that have, in turn, invested in stronger IoT security. Despite all this, however, the vast majority of organizations can still expect at least one cybersecurity attack attempt in a given year. Research from Fortinet found only 6% of organizations experienced no cybersecurity intrusions in 2022.
Putting better cybersecurity measures in place still requires proactive, voluntary compliance from companies—compliance that has not always been forthcoming in the past. While the need for speed may win markets, it is not going away as a major obstacle to safer IoT devices and networks. That leaves experts skeptical about just how much of the problem can be solved by expanded standards—and how much is a result of human nature and incentives in the technology sector. “We tend to rush and enjoy advances in technology, then deal with security problems later on or when they become serious,” says Alsmadi.
References:
Communications of the ACM, June 2023, Vol. 66 No. 6, Pages 14-16
2022 State of Operational Technology and Cybersecurity Report, Fortinet, Jun. 21, 2022, https://bit.ly/3G6HTDO
IoT Standards and Protocols Explained, Behrtech, https://behrtech.com/blog/iot-standards-and-protocols-explained
Number of IoT connected devices worldwide 2019–2021, with forecasts to 2030, Statista, Nov. 22, 2022, https://www-statista-com.libproxy.scu.edu/statistics/1183457/iot-connected-devices-worldwide
Cybersecurity threats in telecoms require protection of network infrastructure and availability
Telecommunications companies have become an attractive target for attackers, as their networks can be used as a back door to other organizations, thereby making it attractive for cybercriminals to gain unauthorized access. These telecoms networks are also used to build, control and operate other critical infrastructure sectors, including energy, information technology, and transportation systems. Given the interconnected nature of telecom networks between critical infrastructure sectors, organizations need to focus on safeguarding network infrastructure and enabling network availability for critical infrastructure communication.
Telecoms face mounting threats due to various factors, such as the absence of technical knowledge, use of legacy systems, presence of sensitive information, inadequate password security, and increasing threat landscape. Operators are also transforming themselves from network infrastructure companies to cloud service companies to improve efficiencies in business operations, roll out new services and applications, and store and distribute content. As telcos are often a gateway into multiple businesses, threats can either target a specific telecom company, its third-party providers, or the subscribers of a telecom service. These attacks can come in various forms.

Trend Micro disclosed that telecoms have a larger cyber-attack surface than most enterprises, often stretching from their base station infrastructure to call centers and home workers’ laptops. The surface area provides ample opportunity for threat actors looking for customer or organizational data, trying to hijack customer accounts, or seeking to disrupt services via DDoS (distributed denial of service) and ransomware. Furthermore, supply chain providers, cloud services, IoT systems and new infrastructure needed to support 5G and network slicing create additional risk.
Industrial Cyber reached out to experts in the telecoms sector to examine the key factors that make the communications sector vulnerable to cyber attacks. They also weigh in on the unique challenges that the communications sector faces when it comes to securing and safeguarding its OT/ICS environments.
Teresa Cottam, the chief analyst at Omnisperience, told Industrial Cyber that in the past, where security was considered in telecoms the focus tended to be how it affected performance – such as minimizing DDoS traffic and attacks. “More recently, as everything has become more interconnected and the threat landscape has evolved, cyberattacks specifically against telecoms firms have increased,” she added.
Cottam pointed out that ultimately four challenges stand out – complexity, exposure, volume and variety, and cost.
On complexity, Cottam said that each individual ‘network’ actually comprises several generations of technology with some of it being decades old, and it might include fixed, mobile, and even satellite infrastructure. “Moving data from one side of the world to another requires multiple networks, each owned by a different company with a different risk profile. The move from 4G to 5G introduces even more complexity. In the 5G era, cloud, data, and IoT are combined – increasing security risks. Breaches now have a company-wide impact from production through supply chains and logistics to corporate systems,” she added.
Cottam also added that “when you consider how much equipment is in public places it’s actually surprising it’s not attacked more often. Malign actors don’t even need to mount a cyberattack, they can simply vandalise equipment to target specific regions or industries.”
Elaborating on volume and variety, Cottam said that the sheer volume of endpoints is staggering and continually increasing. “IoT has already massively increased the number of endpoints and will continue to do so. Many of these so-called smart objects aren’t very smart and are highly vulnerable. Many of the most vulnerable devices are in the home, but wherever they are, each device has the potential to inject malign traffic into the network,” she added.
On cost, Cottam said that the cost of securing a network end-to-end is significant and the reality is that telecoms firms and their customers are having to continually juggle risk versus security.
Turning the question around, Grant Lenahan, partner and principal analyst at Appledore Research, said that one of the huge transitions underway is from fundamentally private data centers and networks to outsourced or managed, secure networks that interconnect distributed enterprise to their digital partners, remote employees, public cloud, and SaaS facilities. Therefore, there is a blurring of public and private targets.
“We certainly can look at those who attack public networks because of the private data and traffic. We can also look at those who attack not an underlying enterprise target per se, but the network infrastructure itself,” Lenahan told Industrial Cyber. “These attacks, rather than going after specific data, or intended either to disrupt, for example, terrorism or to gain control that can later be used to target intellectual property the transit to the network. The very fact that public networks are public, complicates securing them.”
On the other hand, Lenahan added that there is scale and scope, allowing for concentrations of security expertise and automated protections, that might not be possible or affordable by individual enterprises. “We have spent hundreds of pages covering this seismic shift in our security research stream. Some readers might be interested in consulting it,” it added.
Andrei Elefant, CEO of EdgeHawk Security told Industrial Cyber that the key factors that make the communication sector vulnerable to cyber attacks are that the CSPs (communication service providers) face multiple and large attack surfaces. They also have a limited security budget and have to prioritize the security measures they take compared to the cost and priorities.
He also added that security expertise in CSPs is limited. “The various types of attack scenarios, attack methods, the type of data and systems that need to be protected are huge. CSPs cannot build expertise in all the required security domains and have to prioritize focus areas. The CSPs are defined as critical infrastructure and are frequently a target of Nation State Actors, which means higher expertise and more budget on the attackers’ side.”
Elefant added that these challenges are even more noticeable when it comes to protecting the OT/ICS environment. “Attack surfaces grow exponentially with the growth in the number and variety of the endpoints. Many of the OT endpoints have limited inherent protection capabilities (due to resources limitation, legacy devices, etc.,), which means they can be a perfect attack surface to harm CSPs or penetrate their networks. In many cases, these devices are being exploited for DDoS attacks, as they are available in masses with limited protection.”
Addressing the essential components that make cybersecurity in telecoms a vital and fundamental part of protecting the telecommunications landscape, as it also serves much of/all the other critical infrastructure sectors, Cottam said that not having complete visibility of the complexity of the telecoms landscape is one of the biggest challenges. “For example, there could be vulnerabilities in equipment and devices – which is often the focus of analyst reports – but equally there can be vulnerabilities in core processes which were put in place decades ago and haven’t been updated,” she added.
Cottam identified that a typical attack occurs by a criminal convincing the telecoms firm they are the customer and want to move to a new provider. “The telecoms firm – often with only minimal checking – provides the ‘customer’ with the means to do so. In the UK the system is designed to make it as easy as possible for the customer to do this, which also makes it easy for criminals. Such an attack against employees is bad; now consider it targeted at IoT devices. This is a great example of how cybersecurity often focuses on securing equipment (endpoints) but ignores vulnerable processes,” she added.
“Many countries have acted to secure number portability and in this respect, the UK is particularly vulnerable as its current system is so old-fashioned and inefficient,” according to Cottam. “Another problem this causes for IIOT is that the UK system also struggles to port large volumes of numbers such as would need to happen with a large corporate or IoT customer. This has the potential of decreasing competition in the connectivity part of the market since it’s a blocker to switching operators.”
Lenahan said that he doesn’t “believe we need to emphasize how important telecom infrastructure is. Not only is it critical infrastructure and it’s all right, but it is often the control plane for other infrastructure such as water, gas, electricity, emergency services, and many other essential components of both private public, and industrial life. It is, what’s on call, a target rich environment. That said, let’s look at what success looks like,” he added.
Elefant said that the CSPs are becoming a part of the critical infrastructures in any state. “National defense strongly relies on communication availability on the state level, in addition to the fact that these networks provide essential communication infrastructure to many other critical infrastructure facilities,” he added.
The essential components needed to keep CSPs networks available and reliable focus on two main aspects, according to Elefant. “Protecting the network infrastructure from unauthorized access and malicious attacks. This includes implementing firewalls, intrusion detection and prevention systems, and other security measures to prevent unauthorized access.”
He also pointed to protecting network availability for critical infrastructure communication by identifying and blocking attempts to saturate the network and accessibility to specific applications/devices using DDoS attacks.
The telecoms industry has had to reconsider its cybersecurity protocols in light of the digitization and incorporation of Industrial Internet of Things (IIoT) technologies. The executives looked into the main threats posed by increased connectivity techniques and how this shift affects the cybersecurity posture of these communication companies.
Cottam said that often today’s IIoT devices use the same networks as other systems, which presents a double-edged risk. “If a criminal can compromise an IIoT device they could use this as an access point to corporate systems; if they compromise corporate systems or user devices they can hijack IIoT devices. Again, this speaks to the interconnectedness of networks and often the poor understanding of how criminals can utilise connections and access points to compromise industrial customers.”
“The main concerns from customers include exposure of their data, compromised network equipment, attacks on devices and network signaling, as well as creating a gateway for further attacks. Network segmentation is a useful technique to limit the scope of such attacks,” according to Cottam. “Reliable security frameworks are built into 3GPP standards to ensure 4G and 5G cellular connections are secure. But as we move to 5G a range of new exciting techniques are also delivered.”
Another technique is to utilize private networks – effectively campus networks within a factory or industrial complex with limited connections to the public network but complex connections within the private network, Cottam said. “Connectivity is only provided to authorised devices (more secure than WiFi, as it can be based on SIM authentication) and data is processed on-site,” she added.
“The simplest way to look at this is that complexity is increasing dramatically in enterprise networks. There will be an order of magnitude more endpoints; applications and data will reside in various clouds; and dynamically changing ecosystems of digital trading partners will continuously evolve,” Lenahan said. “This implies a complex network that crosses ownership boundaries, and is constantly changing.”
Lenahan noted that the only apparent constant throughout this ‘web’ is the telecom CSP that undertakes end-to-end connectivity, orchestration, and in our view, security. “This is a huge opportunity for our industry. However, it also means we need to think completely differently about security. It cannot be a separate island; it must be integrated into network automation. Furthermore, it must be automated, something tacos in security professionals have long been uncomfortable with,” he added.
Elefant identified some of the threats brought by these increased connectivity techniques, including increased attack surface, unsecured devices, protocol vulnerabilities, and DDoS attacks. With “the exponential increase in the number of connected devices, the attack surface of the network has increased, creating more opportunities for malicious actors to gain unauthorized access to the network. Many IoT devices are not designed with security in mind, and may have weak passwords, unpatched vulnerabilities, or lack encryption, making them easy targets for attackers.”
He also pointed out that IoT devices often use proprietary protocols, which may have vulnerabilities that are not well understood and are difficult to patch. IoT devices can be easily compromised and used to launch DDoS attacks, overwhelming the network with traffic and causing availability issues.
Elefant highlighted that the new threats have led to a shift in the cybersecurity posture of CSPs. “Implementing more strict network segmentation, both on their infrastructure and also as a service to their customers. Specifically for the IIoT environment, access control services, delivered by the CSPs, are being applied on a larger scale. Protecting the network from DDoS attacks on the edge and access points became a mandatory consideration. Additionally, there is a need to continuously monitor and assess the security of the network edge and access as more attacks may come from exploited devices connected to the network.”
Like other critical infrastructure sectors, the communications sector has also faced mounting cybersecurity rules and regulations in recent times. The executives address how the communication sector responded to the increase in cybersecurity regulations for critical infrastructure owners and operators, as well as analyze the impact these initiatives have had in enhancing reporting procedures and improving the cybersecurity posture of the telecoms sector.
Cottam said that one of the biggest challenges stems from the ‘democratisation’ of IoT. “As it becomes the norm in manufacturing supply chains, smaller and newer industrial firms are drawn in or adopt IoT to increase their efficiency. These firms often don’t fully understand the importance or complexity of securing their IoT devices and lack the budget and expertise in-house,” she added.
Another challenge is that many enterprises deploy and secure IoT from an IT perspective, according to Cottam. “Traditional IT security largely focuses on end-point and perimeter security. But with hundreds of thousands of IoT endpoints and more permeable boundaries, the emphasis has to shift to securing and managing the network rather than trying to put security into every device – not all of which are designed to be secured,” she added.
“Likewise, while cellular IoT is reasonably secure – and that based on 5G even more so – it is not unhackable. IoT network security isn’t just about securing the network either, it’s about network-based security that can monitor all the connected objects, processes, and applications,” Cottam said. “Neither is it just about hackers anymore. Nation states, protestors, and terrorists are just as likely to want to attack critical infrastructure and their objectives are different and their budgets and expertise are huge. While there has been much talk of bringing together IT/OT/IoT into a single process to make it more manageable and auditable, the risk is that the complexity and volume become overwhelming.”
Lenahan said that details on how telcos are handling critical infrastructure security are hard to get, and in my opinion, rightly so. “That said, we can see many trends in the industry to prepare telecoms to not only be more secure on its own but to be in a good position to secure infrastructure for others. Some things are as simple as the collaborative work in the MEF, on secure transport services — or the transport service in security or considered as one. Similarly, the managed services, with security at their core, that many leading telcos are offering to their enterprise clients, can be applied to protecting public and shared infrastructure as well,” he added.
“One thing we believe they must change is that these ‘managed’ services, which, by definition, are semi-custom, must become more standardized products,” according to Lenahan. “We say this because that is the only way telcos can afford to invest in the level of automation that will truly illuminate errors and omissions and stay ahead of the bad actors. It’s simply a matter of operating a process at scale and concentrating one’s fire, so to speak.”
The CSPs responded in various methods to address the increase in cybersecurity regulations for critical infrastructure, Elefant said. “Increase in network segmentation to protect critical infrastructure, the CSPs designed their networks in a way they can segment their network based on the type of service they need to deliver. Applying more protection capabilities at the edge of the network to protect the network from threats that may come from the access side, in addition to more traditional protection methods they apply on the network core,” he added.
Elefant also suggested adding more secure communication channels, like segmentation and encryption for critical elements, such as the control plane, and adding more monitoring tools to identify security risks in real time. “These initiatives help CSPs to identify security threats in real-time and apply faster response and mitigation, leveraging the new control points, mainly at the edge of the network,” he concluded.
References:
https://www.trendmicro.com/en_se/research/22/b/the-telecoms-cyber-threat-landscape-in-2021.html
Cybersecurity to be a top priority for telcos in 2023
IEEE/SCU SoE Virtual Event: May 26, 2022- Critical Cybersecurity Issues for Cellular Networks (3G/4G, 5G), IoT, and Cloud Resident Data Centers