5G private networks
Analysys Mason: few private networks include edge computing, despite the synergies between the two technologies
In a report on Private LTE/5G network deployments, Analysys Mason said that “Only 58 of the 363 private network announcements in our tracker explicitly mention that the private network is working with edge computing.” That’s no surprise as per our recent IEEE Techblog post that edge computing has not lived up to its promise and potential.
The number of announced private networks increased from 256 during the third quarter of last year, to 363 announced deployments during Q3 of this year. Most of that growth is coming from more advanced countries and China “where the IoT markets are mature and are driving demand for private networks.” Private networks using 4G LTE technology continue to dominate the overall market “because it is able to meet the connectivity requirements of most private network applications.” However, 5G is gaining ground with more than 70% of new networks announced this year stating the use of 5G technology.
Private networks and edge computing are complementary as each adds value to the other. When combined, the technologies can support applications that have requirements for low latency and high bandwidth or that need to be located on site for security purposes.
The adoption of edge computing with private networks has been limited thus far due to several factors, such as the relative immaturity of edge technology. The drivers of private network adoption are also different to those of edge computing adoption.
Private LTE/5G networks are often introduced to replace existing Wi-Fi or fibre access networks, and no other changes are made. Nevertheless, the share of private network announcements that mention edge is growing, and more than 20% of the private networks that have been publicly announced in 2022 so far include edge. We expect that more private networks will include edge computing in the next 18–24 months. Some vendors are promoting edge as part of a packaged private network solution (such as Nokia with its NDAC solution).
A few operators, such as Verizon, Vodafone and the Chinese MNOs, are promoting the combination, and many other service providers have trials that combine the technologies.
Verizon Business CEO Sowmyanarayan Sampath who during a recent NSR & BCG Innovation Conference explained that private 5G network momentum was outpacing demand for the carrier’s mobile edge computing (MEC) services.
“On the MEC, what we are finding is demand is taking a little longer to go,” Sampath said. “And part of that is we are having to work back and integrate deeper into their operating system. So it’s going to be much stickier when it does happen [but] it’s going to take a little longer. We’ve got loads of proof of concepts and early commercial deployments, but we shouldn’t see revenue till the back half of next year and into 2024.”

References:
https://www.sdxcentral.com/edge/definitions/what-multi-access-edge-computing-mec/
Has Edge Computing Lived Up to Its Potential? Barriers to Deployment
Juniper Research: 5G Fixed Wireless Access to Generate $2.5 Billion in Operator Revenue by 2023
Global telco revenues from 5G Fixed Wireless Access (FWA) will rise from $515 million in 2022 to $2.5 billion next year, according to a new report from Juniper Research. FWA includes services that provide high-speed Internet connectivity through cellular‑enabled CPE (Customer Premises Equipment) for uses including broadband and IoT networks.
The research predicts that operators’ 5G FWA revenue will reach $24 billion globally by 2027. It identified the consumer market as the sector generating the highest revenue for network operators, representing 96% of global 5G FWA revenue. However, it warns that operators must provide a compelling user proposition for FWA solutions through the bundling of services such as video streaming, gaming and smart home security to enrich user experience and gain competitive advantage against incumbent high‑speed connectivity technologies, such as FTTP (Fibre‑to‑the‑Premises).
| Key Market Statistics | |
| Market size in 2022: | $515m |
| Market size in 2023: | $2.5bn |
| 2022 – 2027 Market Growth: | 480% |
Juniper Research author Elisha Sudlow-Poole remarked: “The benefits of FWA are now comparable with services using fibre-based networks. Operators have an immediate opportunity to generate revenue from broadband subscriptions directly to end users by providing last-mile solutions underpinned by their existing 5G infrastructure.”
Juniper Research notes that the increase in 5G subscribers will be driven mainly by “the accelerating migration of cellular subscriptions to 5G networks, owing to operator strategies that minimize or remove any premium over existing 4G subscription offerings,” and that 600 million additional 5G subscriptions are expected be created next year, “despite the anticipated economic downturn in 2023.”
The report predicts that the growth of 5G networks will continue, and over 80% of global operator‑billed revenue will be attributable to 5G connections by 2027. The telecommunications industry demonstrated its robustness against the impact of the COVID-19 pandemic, and the report forecasts that the growth of 5G will also be resilient against this economic downturn due to the vital importance of mobile Internet connectivity today.
Juniper Research co-author Olivia Williams noted: “Despite the growth of the Internet of Things, revenue from consumer connections will continue to be the cornerstone of 5G operator revenue increase. Over 95% of global 5G connections in 2027 will be connected personal devices such as smartphones, tablets and mobile broadband routers.”
Private 5G Networks Represent a Key Opportunity for Operators:
In addition, the report predicts that the ability of standalone 5G networks to offer ‘network slicing’ will act as the ideal platform for the growth of 5G private network revenue. 5G Standalone (SA) uses 5G core networks supporting network slicing technology, which can be used to take a ‘slice’ of public 5G infrastructure and provide it to private network users. In turn, this helps mitigate the cost of private 5G network hardware and increase its overall value proposition, all against a background of deteriorating macro-economic conditions.
The report recommends that operators use 5G FWA to facilitate the last mile-solution by treating the relationship between FWA and fibre networks as wholly collaborative to maximize network performance and return on investment.
References:
https://www.juniperresearch.com/whitepapers/how-operators-will-capitalise-on-5g-fixed-wireless
5G Service Revenue to Reach $315 Billion Globally in 2023 | TelecomTV
Understanding security threats for telco edge and private 5G networks
Author: Adil Baghir (edited by Alan J Weissberger)
Introduction:
Telcos and enterprises realize the need to move toward the network edge to deploy cloud-like solutions to leverage the massive advances in transmission offered by 5G. Benefits such as speed, low latency, and capacity will drive major transformation for telcos and enterprises, opening new revenue opportunities from new business models. We’ll examine several 5G deployment scenarios and security threats in this article.
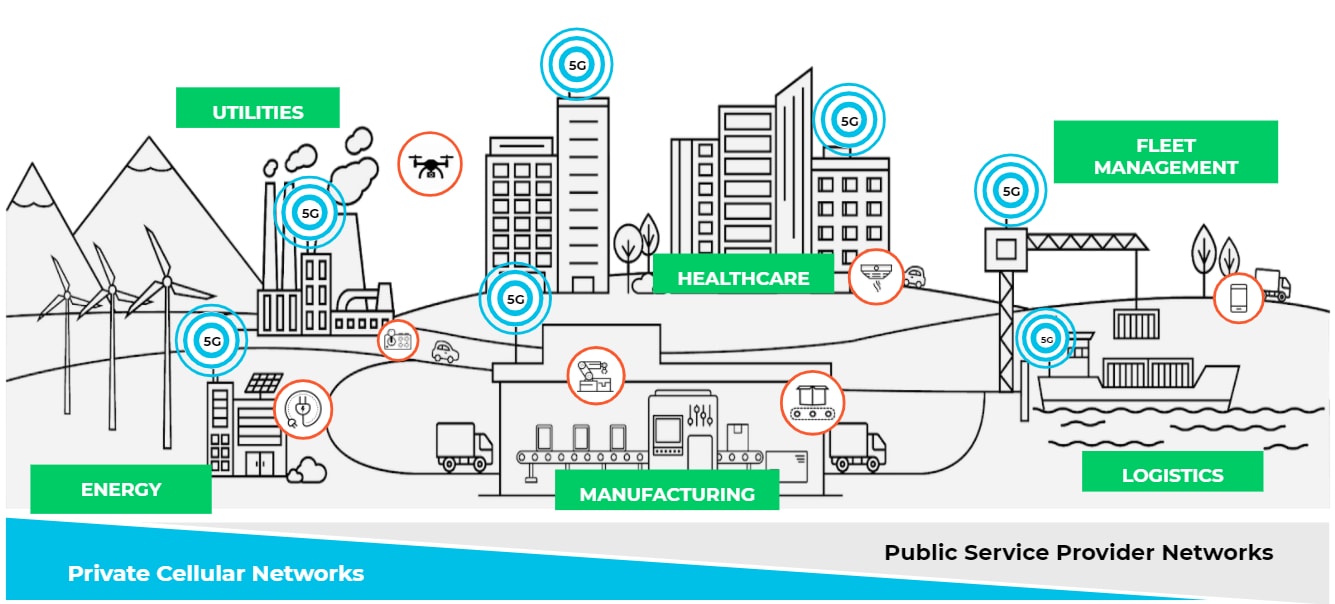
Image Credit: Palo Alto Networks
……………………………………………………………………………………………………………………………………………………………………….
Discussion:
Telcos and enterprises are exploring new use cases by deploying edge clouds and bringing content and applications closer to the users and billions of IoT devices to meet the low-latency requirements. The Ericsson 2022 Mobility Report forecasts that over 30 billion Internet of Things (IoT) devices will be connected by 2027.
The 5G core network functions could be deployed as a microservice in a private data centre of the communications service provider (CSP) and enterprise network or in a public cloud (like AT&T-Microsoft Azure and Dish Network-Amazon AWS).
The shift to the edge and deploying telco cloud edge services and enterprise hybrid private 5G networks introduce new security threats associated with the 5G and edge deployment.
Even though there are security risks with 3G/4G, these risks are mainly associated with external attacks. However, with 5G/MEC/IoT architecture, these risks become more serious. 5G core and edge sites can be attacked from the internal network in an “inside-to-outside” approach. Considering that 5G provides high-speed internet broadband, connecting a massive number of consumer and IoT devices, this can be viewed as a new point of attack for the 5G cloud edge architecture.
Such massive transformation forces telcos and enterprises are deploying cloud edge and private 5G services to rethink their security and network protection. There are many challenges in how telcos and enterprises deploy security solutions today as they cannot provide integrated 5G core and security solutions to adapt with cloud-edge use cases. For example, moving to the edge will require a low footprint, automation, scaling and simplified lifecycle management (LCM). Given the increase in the number of edge sites deployed, it will be very complex to manage and scale different security solutions manually. The typical deployments of security solutions are not optimised for distributed and cloud-edge architectures.
The impact of security compromise on an operator or enterprise edge network could be massive because edge sites usually have less capacity than core sites and host mission-critical applications to accommodate low latency requirements, including IoT use cases. For example, a 10/20G volumetric DDoS attack could have a major impact on the network availability and low-latency requirements, and it would lead to a critical service interruption and result in brand damage.
The shift to cloud and edge for telcos and enterprises is an evolved approach to deploying and delivering services and solutions, and introducing a more dynamic environment. The security measures in place today are not aligned with the cloud-edge requirements for the footprint for physical security solutions, increasing number of edge sites, cloud-native strategy and other required capabilities to improve TCO.
DDoS-based IoT Botnet
Most IoT devices have limited computing resources to provide security functionality and typically are not securely coded. MOZI is an example of a DDoS-focused IoT botnet that utilises a large set of remote code executions (RCEs) to leverage common vulnerabilities and exposures (CVEs) in IoT devices for infection. These devices include network gateways, CCTVs, DVRs, etc. Once the IoT device is successfully infected, the botnet uses protocols/apps, such as TCP/UDP/HTTP, to send and receive configuration updates and attack commands. Eventually, the infected IoT nodes begin generating attack traffic, leading to a massive and sudden spike in UDP traffic going back and forth with peer-to-peer networks. Such volumetric attacks from compromised IoT devices will make it very challenging to guarantee a level of service and maintain low-latency requirements.
Even though it’s always recommended to keep the IoT devices running the latest firmware with all the necessary security patches applied. However, we can’t rely entirely on securing or updating IoT devices. Therefore the network should also be equipped with modern security solutions like DDoS baselining techniques to see anomalous behaviour versus historical norms, and AI/ML techniques, for detection and zero-day attack prevention.
Mobile Edge Cloud and Private 5G Requires New Security Approaches
Security for mobile cloud edge and enterprise hybrid private 5G must be measured carefully to align with the new and increasing security threats. This requires securing the mobile core infrastructure and modern network protection to deliver mission-critical applications while maintaining low latency requirements. Ultimately, this will help telcos and enterprises achieve their desired business outcomes.
In addition, the security implementation for telcos should consider security-as-a-service so that operators may offer secure IoT services leveraging network slicing and provide the flexibility for end customers to manage their security policies with complete network isolation. This requires security integration with the 5G ecosystems to ensure subscriber and device awareness for more agile security control.
Enterprises that deploy private 5G networks may lack the telco experience and knowledge to secure that mobile infrastructure. They might rely entirely on the MNO or their mobile network equipment providers (NEPs) to ensure the infrastructure is fully secured and protected. However, enterprises must extend their network and IT security standards and take all the necessary considerations when they move their critical systems and applications to the edge.
Although 5G comes with embedded security standards, it also introduces potential security risks associated with the deployment model and communications systems. In this post, I have focused on one of the security risks associated with 5G deployment: a DDoS-based IoT botnet. In Part II, I will cover other potential security areas:
- 5G deployment in Hyperscale Cloud Providers (HCP)
- HTTP/2 and exposure of API
- Inert-PLMN
Resources:
Threat Intelligence Report, A10 Global State of DDoS Weapons, H1 2021
Ericsson 2022 Mobility Report, June 2022
Evolving 5G Security for the Cloud, 5G Americas White Paper, Sept 2022
Lockheed Martin, AT&T Demonstrate High Speed Transfer of Black Hawk Data on AT&T 5G Private Network and 5G.MIL® Pilot Network
Lockheed Martin and AT&T securely and rapidly transferred UH-60M Black Hawk health and usage data through an AT&T 5G private cellular network and Lockheed Martin’s 5G.MIL® multi-site pilot network in a test conducted Aug. 4 at Lockheed Martin’s Sikorsky headquarters in Stratford, Connecticut.
The test demonstrated that wireless 5G technologies on the flight line can support accelerated maintenance operations and improved aircraft readiness to support our service members. It also proved highly secure interoperability between the AT&T millimeter wave 5G private cellular network and the 5G.MIL pilot network.
- Technology reduced data transfer time for military helicopters by more than 80%
- Using 5G capabilities, network engineers transfer health and usage data from a Sikorsky UH-60M Black Hawk to Waterton, Colorado, for real-time analysis
“These 5G capabilities deployed at scale are expected to enable high-speed, secure-data transfer on virtually any flight line, providing another example of how we’re advancing our 21st Century Security vision by improving customer readiness and operations,” said Dan Rice, vice president of 5G.MIL Programs at Lockheed Martin. “In collaboration with commercial 5G leaders, an interoperable 5G.MIL multi-site, multi-vendor network is another step closer to reality.”
The AT&T 5G millimeter wave private cellular network wirelessly transferred data to the 5G.MIL network through ground support equipment from the Black Hawk’s Integrated Vehicle Health Management System (IVHMS). The data was then routed to local Sikorsky networks for processing and distribution through the secure Lockheed Martin 5G.MIL pilot network to the Waterton, Colorado, 5G test range site.
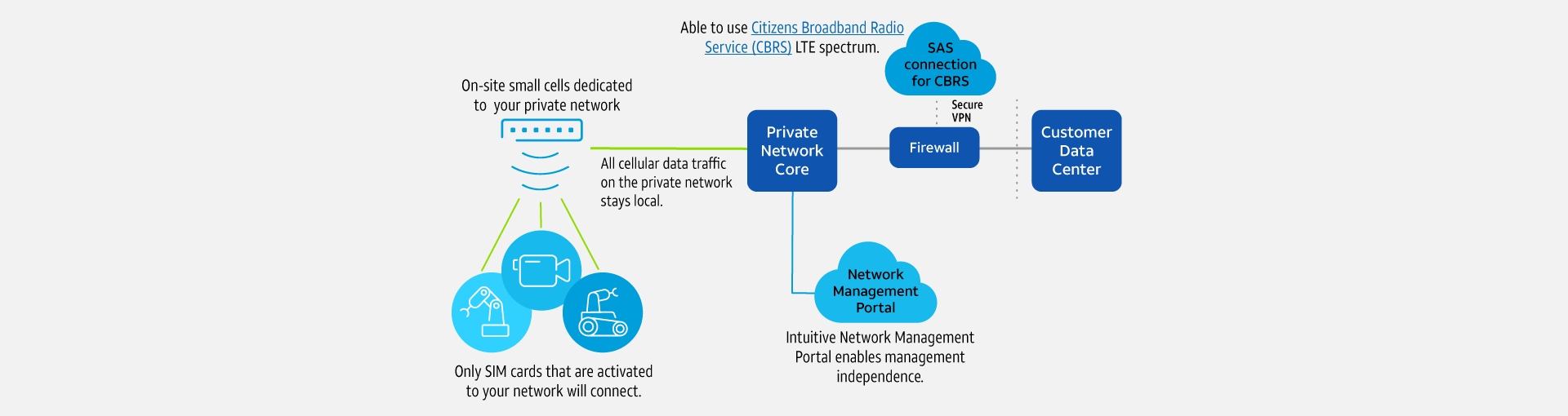
Image Credit: AT&T
Currently, it takes Black Hawk crews about 30 minutes to remove the IVHMS data cartridge from the helicopter, transport it to an operations center and extract the data for analysis. Lockheed Martin used AT&T 5G private cellular technologies to reduce the time required to less than 5 minutes including cartridge removal, demonstrating the potential benefits in time and cost for military and commercial helicopter operations.
The IVHMS provides monitoring and diagnostic capabilities to ensure a more reliable aircraft. It monitors, captures and evaluates detailed aircraft-generated data as a result of flight maneuvers. It also captures aircraft limit exceedances on airframe and dynamic components and monitors temperature and vibration of key components on the aircraft. It does this through hundreds of on-board sensors that report the status of the aircraft by monitoring the airframe, engines, and other dynamic components. Operators assess these thousands of data points to ensure the aircraft is safe, reliable and ready to fly.
“Timely and secure transfer and analysis of mission and operations data are critical to military readiness and effectiveness,” said Lance Spencer, client executive vice president, Defense, AT&T Public Sector and FirstNet. “This is one of many areas of commercial 5G innovation we are exploring to support defense, commercial aviation, and related fields where our 5G-related services can modernize legacy processes and help deliver truly transformational benefits.”
Lockheed Martin and AT&T also are working with other leading companies in networking and defense to modernize and transform communications capabilities for defense purposes. Future demonstrations are expected to further enhance 5G wireless technology communications solutions for flight lines, aiming to continually shorten aircraft turnaround times to reduce costs and improve military operational readiness. These capabilities deployed at scale can support high-speed, secure-data transfer on both commercial and military flight lines.
AT&T’s 5G and private cellular Multi-access Edge Computing (MEC) capabilities are deployed together by multiple industrial customers in factories nationwide where they enable ultra-fast, highly secure wireless processing and information transfer.
References:
https://www.business.att.com/products/att-private-cellular-networks.html
For additional information about Lockheed Martin, visit www.lockheedmartin.com/5G.
For more information about AT&T’s work in Defense, click here.
Celona’s 5G LAN solution for private 5G now on Google Distributed Cloud Edge
Celona, an innovator of 5G LAN solutions, today announced it has been selected by Google Cloud to accelerate the delivery of private 5G networks in the U.S. by making its 5G LAN solution available through Google Cloud’s recently announced private cellular network solutions running on Google Distributed Cloud Edge (GDC Edge) [1.].Enterprises using Google Cloud will now enjoy unprecedented agility and economies of scale by bringing new private cellular network services closer to users, data, and applications at the mobile compute edge.
Note 1. Google Distributed Cloud Edge is a fully managed product that brings Google Cloud’s infrastructure and services closer to where data is being generated and consumed. Google Distributed Cloud Edge empowers communication service providers to run 5G Core and Radio Access Network (RAN) functions at the edge.
………………………………………………………………………………………………………………………………..
Google Cloud and Celona are working together to offer turnkey enterprise private 5G networks with the ability to run network management, control, and user plane functions on Google Distributed Cloud Edge wherever it resides. The combined solution addresses distinct performance, service-level, and economic needs of key industry verticals by combining dedicated network capabilities with full edge-computing application stacks. Celona’s solution delivers a complete end-to-end 5G LAN developed for enterprise environments.
“We are excited to partner with Celona to help IT professionals improve application connectivity through private 5G,” said Tanuj Raja, Global Director, Strategic Partnerships at Google Cloud. “Deployed on Google Distributed Cloud Edge, Celona’s end-to-end private network solution enables enterprises to simplify and operate private 5G networks at scale and with the flexibility they need.”
“The combination of 5G LANs and edge compute unlocks a new generation of enterprise IT architecture capable of keeping up with the immense rate of digital transformation and automation occurring across almost every industry,” said Rajeev Shah, Celona’s co-founder and CEO. “The intrinsic agility of our edgeless enterprise architecture gives organizations tremendous flexibility and scale by bringing closer together critical network services and mobile edge compute applications.”

Celona’s Edgeless Enterprise architecture is anchored by the Celona Edge, a cloud-native 4G/5G private core network operating system that delivers an all-in-one network service overlay with advanced policy-based routing, QoS, and security segmentation functions. Celona’s unique approach supports the convergence of radio access network (RAN), application, and network service traffic, automatically shifting the delivery route of services based on performance, policy requirements, and network paths’ real-time health. It is the only private 5G solution in the industry that has been purpose-built to help organizations easily deploy, operate, and integrate 5G cellular technology with their existing infrastructure.
Since launching the first fully integrated 5G LAN platform in November 2020, Celona has seen strong demand from a range of enterprises, managed service providers, and mobile network operators looking to satisfy strategic digital business initiatives not adequately addressed today by Wi-Fi or other networking technologies. The company’s diverse customer base includes world-class organizations such as Verizon, NTT Ltd, SBA Communications, St. Luke’s Hospital System, Purdue Research Foundation, Stanislaus State University, and many other brand-named enterprises.
Celona’s 5G LAN platform is used by manufacturers, retailers, hospitals, schools, and supply-chain leaders to drive transformational results for a wide range of mission-critical use cases that require the deterministic wireless connectivity on private & interference-free cellular spectrum and fast mobility for a new generation of highly mobile devices and robotics infrastructures.
ABOUT CELONA:
Celona, the enterprise 5G company, is focused on enabling organizations of all sizes to implement the latest generation of digital automation initiatives in enterprise wireless. Taking advantage of dynamic spectrum sharing options such as CBRS in the United States, Celona’s Edgeless Enterprise architecture is designed to automate the adoption of private cellular wireless by enterprise organizations and their technology partners. For more information, please visit celona.io and follow Celona on Twitter @celonaio.
MEDIA CONTACT:
David Callisch
Celona, Inc.
[email protected]
+1 (408)504-5487
References:
https://www.celona.io/resources/celona-partners-with-google-cloud-for-5g-lans
https://www.celona.io/resources/5g-lan-provider-celona-is-named-a-cool-vendor-by-gartner
How organizations are using Google Distributed Cloud Edge with 5G LANs to streamline operations by visiting https://www.celona.io/community-stories/google-distributed-cloud-edge-and-celona-5g-lans
Ericsson focuses on private 5G in China due to national directives
Ericsson will shift its focus towards helping Chinese businesses to build their own private 5G networks, according to an excerpt from a report by Caixin Global. The news outlet cited remarks by Fang Ying, president of Ericsson’s China operations, at a news briefing on 22 June. Fang said there are growth opportunities in the private 5G networks sector after the aggressive pace of construction in 5G infrastructure nationwide over the past three years.

Dell’Oro Group’s Stefan Pongranz explains this increased focus on private 5G in China are stimulated by several key national directives:
(1) The Made in China 2025 Initiative, which pushes for greater usage of industrial robotics and automation in 10 key strategic sectors,
(2) The Internet Plus Plan, an initiative to transform, modernize, and equip traditional industries with more advanced technologies, and
(3) Set Sail Action Plan for 5G Applications, which targets 3,000 private industrial networks and a 35% 5G penetration rate in large industrial enterprises by 2023.
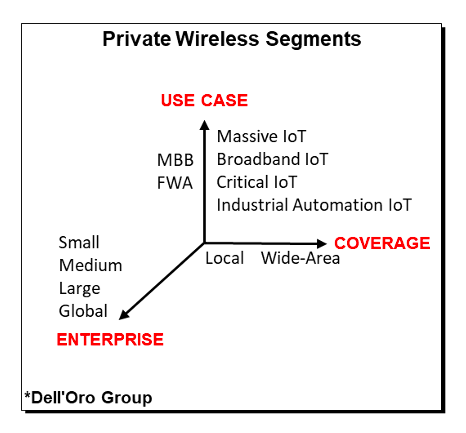
Huawei, Ericsson, and Nokia are all reporting some initial success with private 5G industrial opportunities. Verizon has explored multiple solutions and found that Celona’s 5G LAN technology is easy to scale downward, could be setup in hours, and straight-forward to integrate with the existing LAN.
Perhaps more importantly, the RAN is just one piece of the private 5G puzzle. While there is limited data at this juncture to suggest that the average private RAN network as a share of total cost of ownership (TCO) will be materially different than the public RAN share (10% to 15% of total TCO), it is safe to assume that the value, the role and the importance of the RAN will differ significantly depending on the segment and the use cases.
In short, it is still early days when it comes to private 5G. But the opportunity is large and private 5G is projected to surpass $1 billion by 2025. Optimized private solutions and services will play an important role simplifying and accelerating private LTE and 5G. And if Cisco and AWS are right, it will be interesting to see how the private 5G ramp will impact the RAN vendor dynamics.
References:
Deloitte’s 2022 telecom industry outlook, questions and recommendations for telcos
Executive Summary:
In 2022, the telecom industry will face new opportunities and challenges presented by a dynamic regulatory, technological, and competitive environment. Deloitte’s annual telecom outlook dials into the biggest trends shaping the telecommunications industry, from more competitive broadband markets to cybersecurity in the 5G era.

The telecom sector continued to make progress in augmenting its network capacity with additional fiber and wireless deployments to meet the constant demand for higher-speed networks in 2021. However, as we start the new year, we see an emerging set of issues and opportunities presented by a dynamic regulatory, technological, and competitive environment that may influence the sector’s progress in the coming year:
- The potential for more competitive broadband markets. Faster mobile and fixed wireless connections create more viable alternatives to wired connections and new opportunities for bundled service offerings and business models for service providers. With ever-expanding options for high-quality communication and internet services from telecom, cable, wireless, and satellite internet providers, consumers will enjoy enhanced flexibility in purchasing and consuming services in the new year. However, these trends may also lead to a more competitive environment in 2022.
- A shift to more decentralized government broadband infrastructure funding. The $1 trillion Infrastructure Investment and Jobs Act (IIJA) passed in November earmarks $65 billion for continued broadband adoption and deployment. While government programs dedicated to expanding and improving telecommunication infrastructure and services have traditionally been managed at the federal level, it appears the bulk of the bill’s federally allocated broadband dollars will flow through more decentralized state-based models.
- Rising interest in multi-access edge computing (MEC) and private cellular networks. The enterprise market for private cellular networks and edge computing is gaining momentum. The market is still nascent but promises to be competitive, with many different players vying for their share. Network operators will have to compete against other players, who may prove key partners in delivering their solutions. Ecosystem players will likely begin to stake out and define their role in this emerging but rapidly evolving market in the coming year.
- The need to reassess cybersecurity and risk management in the 5G era. While the widespread adoption of 5G offers many benefits, it also creates new security concerns and challenges. As operators have taken steps to evaluate and minimize threats arising from 5G and software-centric networks in their own organizations, they are in a unique position to offer 5G security services to enterprises seeking to deploy their own advanced wireless networks.
Strategic Questions for telcos to consider:
• With spectrum being a scarce resource, how can operators prioritize its use to maximize its value? • How can operators use FWA to create additional synergies between their wireless and fiber asset deployments to improve their cost structure and benefit customers?
• While telcos may initially benefit as a wholesale provider of wireless capacity, what are the long term consequences if mobile virtual network operators begin using their wireless scale to build out their own networks?
• What should the telco’s role be in developing and delivering 5G private cellular networks and enterprise-oriented edge solutions? Will it take the form of spectrum leases, fiber backbone, and backhaul, or something more?
• What are the telco’s core competencies and value proposition in delivering 5G enterprise networks? Which business models will allow telcos to optimize value?
• What capabilities are required to execute on a given strategy or business model? Can telcos develop new capabilities internally? To what extent should they do so?
• How can telcos use their approach to cybersecurity as an opportunity to differentiate themselves and capture value in the 5G enterprise market?
• Where can telcos switch from reactive security mechanisms to more proactive ones?
• As telcos migrate from legacy networks to modern architectures, do they have appropriate risk management and governance organizations in place?
Recommendations for Telcos:
• Reassess core value proposition in an evolving competitive landscape with more players vying for the same customers.
• Reevaluate how and where to participate in terms of both service offerings and geographies. • Look for ways to differentiate services on non-performance attributes since consumers perceive minor differences among provider offerings.
• Determine organizational effectiveness in monitoring and responding to more distributed, state-based mechanisms for awarding federally allocated broadband funds.
• Monitor ecosystem and business model development in the emerging 5G enterprise edge compute and private cellular network markets.
• Build on the unique position to offer differentiated 5G security and risk management services to enterprises seeking to deploy advanced wireless networks.
References:
BT and Ericsson in partnership to provide commercial 5G private networks in the UK
BT and Ericsson have entered a new multi-million-pound joint partnership to provide commercial 5G private networks for the UK market – the first agreement of its kind. The multi-year contract will enable BT to sell 5G services to businesses and organizations in industries like manufacturing, defense, education, retail, healthcare, transport and logistics. It’s critically important to note that to be effective, a 5G private network requires a 5G Core which facilitates all the 5G features and essentials, e.g. network slicing, automation, MEC, security, etc.
The agreement comes just after BT confirmed it was investing close to £100m over the next three years to accelerate the development of customer solutions which integrate emerging technologies like 5G, IoT, Edge Compute, Cloud and AI.
5G Private Networks provide secure indoor and outdoor 5G cellular coverage, making them suitable for a range of uses – particularly in environments such as factories, education campuses and other large sites where security and ultra-low latency connectivity are important.
New innovative applications and IoT capabilities can be enabled through a private 5G network to improve productivity, optimise operations and drive cost savings, such as asset tracking, predictive maintenance, connected sensors, real-time data processing, automation and robotics.
According to a forecast from MarketResearch.com, 5G Private Networks are predicted to grow at an average rate of 40 per cent a year between 2021 and 2028, by which time the market will be worth $14bn (£10.7bn). Both BT and Ericsson believe there is significant demand from UK businesses looking to take advantage of the benefits the new technology can provide.
From MarketResearch.com:
“Key market players are strategically building partnerships with industry giants to set up a private 5G network to provide high-speed secure connectivity to their customers. For instance, in Feb 2020, Nokia Corporation deployed a private 5G network infrastructure for Lufthansa Technik for virtual inspection of engine parts remotely for its civil aviation clients. Moreover, the rising demand for enhanced bandwidth connectivity for secured enterprise applications is anticipated to fuel the adoption of private 5G services globally.”
Marc Overton, BT’s Managing Director for Division X, Enterprise, said: “This UK-first we have signed with Ericsson is a huge milestone and will play a major role in enabling businesses’ transformation, ushering in a new era of hyper-connected spaces.
“We have combined our skill and expertise at building converged fixed and mobile networks with Ericsson’s leading, sustainable and secure 5G network equipment, to offer a pioneering new proposition that will be attractive to many industries. 5G private networks will also support smart factory processes and the advancement of Industry 4.0 which can realise significant cost savings and efficiencies for manufacturers.
“Unlike a public network, a private 5G network can be configured to a specific business’s needs, as well as by individual site or location. They also provide the foundation to overlay other innovative technologies such as IoT, AI, VR and AR, opening up a multitude of possibilities.”
Katherine Ainley, CEO Ericsson UK & Ireland said: “This ground-breaking agreement with BT means we are together taking a leading role in ensuring 5G has a transformative impact for the UK. The high quality, fast and secure connectivity provided by Ericsson Private 5G can help organisations make all-important efficiency gains that can create safer, more productive, and sustainable business operations and help the country build global leaders in the industries and technologies of the future.”
Case study: BT and Ericsson have already worked together on several major projects incorporating private 5G networks, including Belfast Harbour in Northern Ireland, as they accelerate its ambition to become the world’s best regional smart port.
The partners have installed a 5G private network across 35 acres of operational port. This is helping to drive operational efficiencies and accelerate its digital transformation through optimising processes across transport, logistics, supply chain and shipping, as well as boosting productivity through the smooth-running of the Port’s operations.
Every year more than 1.75 million people and over half a million freight vehicles arrive and depart through the Port every year. While 24 million tonnes of goods are managed and carried by ferries, container ships and cargo vessels.
“With activity on that scale you need smart technology that can really make a difference. And that’s what our standalone private 5G network is enabling at the Port,” added Marc Overton.
“We’re now into phase two of the project and this includes various use cases such as teleoperation of heavy plant machinery, artificial reality (AR) for remote maintenance, as well as enhanced video AI analytics and the use of drones for surveillance and inspections.”
The partnership is also exploring how 5G and other emerging technologies such as AI, IoT and Connected Autonomous Vehicles can be used together to enhance public safety, physical security, and address climate change across the Port and other parts of Belfast City.
Mike Dawson, Corporate Services Director, Belfast Harbour Commissioners, said: “Throughout 2021 and to the end of 2022, we will have completed the implementation of both Public and Private 5G Networks. These are the foundation for several Smart and Green port initiatives, including CCTV cameras, Air Quality Monitors, Drones, MiFi units to maximise operational efficiencies and a Digital Twin. The technologies have supported our data collection on the movement of people and things through our Road Traffic Screens, Wayfinding App and a Community App for Traffic.”
BT Group is the UK’s leading provider of fixed and mobile telecommunications and related secure digital products, solutions and services. We also provide managed telecommunications, security and network and IT infrastructure services to customers across 180 countries.
BT Group consists of four customer-facing units: Consumer serves individuals and families in the UK; Enterprise and Global are our UK and international business-focused units respectively; Openreach is an independently governed, wholly owned subsidiary, which wholesales fixed access infrastructure services to its customers – over 650 communication providers across the UK.
British Telecommunications plc is a wholly-owned subsidiary of BT Group plc and encompasses virtually all businesses and assets of the BT Group. BT Group plc is listed on the London Stock Exchange.
For more information, visit www.bt.com/about
References:
https://www.marketresearch.com/Grand-View-Research-v4060/Private-5G-Network-Size-Share-14553525/
India Telcos say private networks will kill 5G business
India’s top tier wireless network operators have called on the Telecom Regulatory Authority of India (Trai) – India’s telecom sector regulator – to scrap the proposed move to administratively allocate 5G spectrum on demand for private enterprise networks through a publicized online portal-based process, warning that such a step could destroy the 5G business case in the country.

The businesses have mentioned that such a proposal, if accepted by the federal government, might probably rob telcos of their future 5G enterprise revenues – estimated at round 40% of the whole for 5G. Revenue loss to such an extent won’t justify needed capital expenditure in establishing 5G networks, they’ve argued.
In its newest suggestions on 5G spectrum pricing, the Trai has advised that non-public enterprises straight acquire 5G spectrum from the federal government and set up their very own captive wi-fi non-public community (CWPNs). It has additionally beneficial a “gentle contact’ on-line portal-based regime” for buying such permissions/licences for establishing CWPNs. Trai has additionally advised that non-public enterprises have the choice to lease spectrum from telcos to arrange their very own captive non-public 5G networks.
“By permitting non-public captive networks for enterprises, Trai is dramatically altering the trade dynamics and hurting the monetary well being of the telecom trade reasonably than bettering it,” the Mobile Operators Affiliation of India (COAI) said in an announcement Tuesday, April 12th.
The COAI represents Reliance Jio, Bharti Airtel and Vodafone Thought (Vi). It added that “enterprise companies represent 30-40% of the (telecom) trade’s total revenues…non-public networks as soon as once more dis-incentivises the telecom industry to spend money on networks and in addition proceed paying excessive levies and taxes.”
The COAI has urged Trai to revisit its newest suggestions and disallow non-public enterprise networks to make sure monetary viability and orderly progress of the telecom trade that, it mentioned, is greater than able to delivering these companies to companies.
India’s mobile carriers had earlier advised Trai that any proposal to put aside 5G spectrum for personal enterprise networks for captive use both at no cost or at an administrative worth would even be legally untenable.
Trai has beneficial that the spectrum for personal networks be assigned administratively on demand by way of a extensively publicized on-line portal-based course of in a good and clear method. However the regulator has left it to the telecom division to determine whether or not such administrative allocation can be legally tenable or not, based mostly on DoT’s spectrum allocation coverage.
In its 5G dialogue paper, Trai had mentioned the likes of Germany, Finland, UK, Brazil, Australia, Hong Kong and Japan had put aside spectrum within the mmWave band for personal captive 5G networks, whereas Slovenia, Sweden and Korea deliberate to put aside each mmWave and mid-band 5G spectrum for such captive networks.
Subsequently, Tata Communications (TCL), Larsen & Toubro (L&T) and cigarette maker ITC had strongly countered the telcos’ place, and known as on Trai to again earmarking devoted spectrum non-public captive networks and undertake international practices to create a personal 5G ecosystem for enterprises to drive the federal government’s Make in India imaginative and prescient.
However one other high telco government mentioned that if operators’ potential 5G income flows from the profitable enterprise enterprise vertical dry up, they might see little enterprise sense in bidding aggressively for 5G airwaves within the upcoming sale.
Bulk of the bidding urge for food for 5G airwaves, he mentioned, stems from the sturdy income potential of the B2B enterprise enterprise. But when that income stream disappears, telcos gained’t have a viable enterprise case to splurge huge cash on 5G spectrum, particularly as they’ve sufficient spectrum to proceed their current cellular broadband companies operations.”
Know-how corporations, although, have strongly backed Trai’s name to permit non-public enterprises to straight acquire 5G spectrum from the federal government by way of the executive route.
“By way of non-public networks, Trai’s suggestions handle the pursuits of TSPs (telecom service suppliers), enterprises and the general public as extra non-public networks would result in extra employment alternatives and enterprise, and translate into larger financial output and advantages,” mentioned the Broadband India Discussion board (BIF), which counts Cisco, Amazon, Google, Microsoft, Fb-owner Meta, Qualcomm and Intel amongst its key members.
Earmarking unique spectrum for personal 5G networks, it mentioned, would additionally present an “enchancement over common SLAs (service level agreements) of public networks, moreover guaranteeing full lack of interference between them”.
BIF added that Trai’s name for task of spectrum administratively for personal 5G networks “is most acceptable” because it has thought of that captive wi-fi non-public networks should not public networks and don’t have any market prospects, and are restricted to a selected location.”
Trai chairman PD Vaghela termed the 5G spectrum rates “reasonable”, saying they have been arrived at after considering various factors including quantum of spectrum offered, competition in the market and profitability.
……………………………………………………………………………………………………
April 18, 2022 Addendum:
Spectrum users have started squabbling over the telecom regulator’s recommendation to earmark certain bands for captive wireless private networks.
The cellular operators under the COAI have opposed regulator suggestions of allowing enterprises to build their own private 5G networks for captive purposes.
Technology players such as Facebook, Google, Indian Space Association (ISpA) want the 28.5GHz band spectrum to be reserved and allocated exclusively for satellite communications (satcom) services.
The COAI said “by allowing private captive networks for enterprises, telecom regulator Trai is dramatically altering the industry dynamics and hurting the financial health of the industry rather than improving it”.
“Telecom service providers have and going forward will invest lakhs of crore rupees in network rollouts. Enterprise services constitute 30-40 per cent of the industry’s overall revenues. Private networks once again disincentivises the telecom industry to invest in networks and continue paying high levies and taxes.”
The Broadband India Forum (BIF), the industry body of tech players such as Facebook and Google, welcomed the recommendations to allow private networks.
Telcos flay plan for private 5G networks

Spectrum users have started squabbling over the telecom regulator’s recommendation to earmark certain bands for captive wireless private networks.
The cellular operators under the COAI have opposed regulator suggestions of allowing enterprises to build their own private 5G networks for captive purposes.
The suggestion has been welcomed by the Broadband India Forum (BIF).
Technology players such as Facebook, Google, Indian Space Association (ISpA) want the 28.5GHz band spectrum to be reserved and allocated exclusively for satellite communications (satcom) services.
The COAI said “by allowing private captive networks for enterprises, telecom regulator Trai is dramatically altering the industry dynamics and hurting the financial health of the industry rather than improving it”.
“Telecom service providers have and going forward will invest lakhs of crore rupees in network rollouts. Enterprise services constitute 30-40 per cent of the industry’s overall revenues. Private networks once again disincentivises the telecom industry to invest in networks and continue paying high levies and taxes.”
The Broadband India Forum (BIF), the industry body of tech players such as Facebook and Google, welcomed the recommendations to allow private networks.
The Indian Space Association (IsPA) said “we welcome Trai’s recommendation that calls for coexistence of satellite communications and IMT in the 27.5-28.5GHz band. We also appreciate recommending an exclusion zone for satellite earth stations in the 27.5-28.5GHz band.”
IsPA opposed the inclusion of all spectrum in the 24.25-28.5GHz bands along with low and mid bands in the auction as it was a case of oversupply to the telecom operators at the cost of the satellite industry.
“The 24.25-27.5GHz bands along with 3.3-3.67GHz bands would be more than sufficient for 5G. Therefore, in line with the global best practices, the 28GHz band should be allocated exclusively for satellite communications,” it added.
In its recent recommendations, telecom regulator Trai said spectrum in three bands – 3700-3800MHz, 4800-4990MHz and 28.5-29.5GHz band – could be earmarked for captive wireless private networks which, it felt, could co-exist with non-IMT services.
In the 28.5-29.5 MHz band, Trai said: “A software based transparent system should be built to permit the establishment of private networks and satellite earth Stations based on the geo-coordinates of the proposed location on interference free co-existence basis.”
The regulator added: “DoT should develop a digital map with geographic coordinates of all the existing and future satellite earth stations as well as geographic coordinates of the premises of Private Network locations. Based on this database, permissions for establishment of new installations may be provided to the licensees.”
https://www.telegraphindia.com/business/telcos-flay-plan-for-private-5g-networks/cid/1861119
References:
https://economictimes.indiatimes.com/topic/telecom-regulatory-authority-of-india
Related: IEEE/SCU SoE Panel Session on Open RAN and 5G Private Networks:
Capgemini: Enterprises with spectrum to have better control with 5G Private networks
French technology company Capgemini said that enterprises owning 5G spectrum will give them better control over their plans, thereby reducing dependency. It added that telecom operators will have a role to play for private enterprise networks as managing networks aren’t core competencies of enterprises.
“…even if the spectrum is available with an industry player, I don’t see the situation where the telcos will not be working with the industry in facilitating that. The industry will use 5G as a connectivity, and it’s just not 5G, it is with hybrid cloud, edge computing, IoT, and all other technologies together,” said Monika Gupta – Vice President, Group 5G & Edge lead for Industries & Partnerships, Capgemini.
Industries have key requirements which are very specific including safety, security and the protection of their data. A 5G private network is one solution which ensures that all the data with the connectivity which is there in the particular enterprise campus stays within the campus and doesn’t go out.
Ms Gupta added: “This is not possible in a macro network or in a telco network because in a telco network, it will be ubiquitously available, and anybody can use it or latch it. And hence private networks are one of the key solution offerings with respect to 5G for its adoption towards industries. 5G connectivity is not their [enterprises’] core operations or their core business. And the telcos will always have a role and some contribution to make in this irrespective of whether they own the spectrum, or the spectrum is with the industry. The adoption of 5G for industries is an ecosystem play.”
Capgemini is currently working with Bharti Airtel under a strategic partnership to develop 5G use cases for enterprises. “…two of our use cases have actually been deployed in Airtel Manesar’s lab,” Gupta said.
Capgemini also works with many of the industry clients in India, many of them being our global MNC clients who have large R&D setups, global R&D IT hubs or operations based out of India, she informed.On 5G, she said that while the launch has been delayed, India can still leverage 5G adoption-related learnings from other countries in terms of adopting certain use cases by localizing.
“…the advantage which India has both for telcos and industries is that there is so much learning which can come to India. Capgemini and many of these global MNCs play a crucial role because when we work on similar projects in other countries and in other regions like Europe, America and Asia Pacific, all of this knowledge is then kind of readily available to us in India,” she added.
A lot of 5G projects in other countries have been delivered out of India, she said, adding that the country already has skill sets and people’s capability for 5G deployment.“…the fine tuning which is required is what works for India. The local customization will happen. India has had a very short phase of 5G trials. Now whenever 5G is commercially available India will go straight into a rollout of 5G and will see a quick adoption,” she added.
Capgemini has a global network of labs. It recently opened a 5G lab in a strategic partnership with Swedish telecom gear maker Ericsson to test enterprise use cases.The company also has a similar lab in Paris, which is our headquarters. It has the third lab in Portugal, while the fourth one is coming up in America. Capgemini has developed the 5G Labs to help strategize, build and monetize what 5G brings next for their businesses.

“All of these labs are primarily industry focused labs. With the industry focus lab, we are primarily experimenting with innovating the application of 5G into industrial operations. So these labs actually replicate a lab environment of an enterprise architecture and 5G becomes an integral connectivity piece in that architecture,” Gupta concluded.
……………………………………………………………………………………………………………….
References:
Video of IEEE ComSoc/SCU SoE panel on Open RAN and Private 5G:



