Counterpoint Research: Global Smartphone Market Reaches its Lowest Q3 Levels in a Decade
Global sales of smartphones fell 8% in the third quarter from a year earlier amid a “slower-than-expected recovery in consumer demand,” with both Apple and Samsung losing market share to competing brands during the period, according to Counterpoint Research. Highlights:
- Global smartphone sell-through declined 8% YoY but grew 2% QoQ in Q3 2023.
- Samsung led the market but declined YoY to reach its lowest quarterly level in the last decade.
- A shorter period of iPhone 15 availability in Q3 led to a shift in demand to the next quarter.
- The top five brands’ cumulative share declined in Q3 as challengers’ share grew.
- HONOR, Huawei and Transsion Group were among the only top brands to record YoY growth
The July-September sales figure represented the lowest third-quarter level in a decade, the technology market research firm said, noting that year-over-year global smartphone sales have now fallen for nine consecutive quarters.
However, Counterpoint expects that trend of declines to come to a “halt” in the fourth quarter, as sales benefit from the full impact of the recently launched iPhone 15, the festival season in India, the 11.11 Singles’ Day holiday in China, Christmas, and end-of-year promotions later in the quarter. Counterpoint noted that third-quarter sales were up from the second quarter and that a good performance in September despite the limited availability of the new iPhones provides reason for optimism.
Global market leader Samsung saw its share of the global smartphone market drop to 20% in the third quarter from 21% a year earlier, as sales fell 13%. Apple’s share of the global smartphone market also fell 1 percentage point, to 16%, as its sales declined 9%.
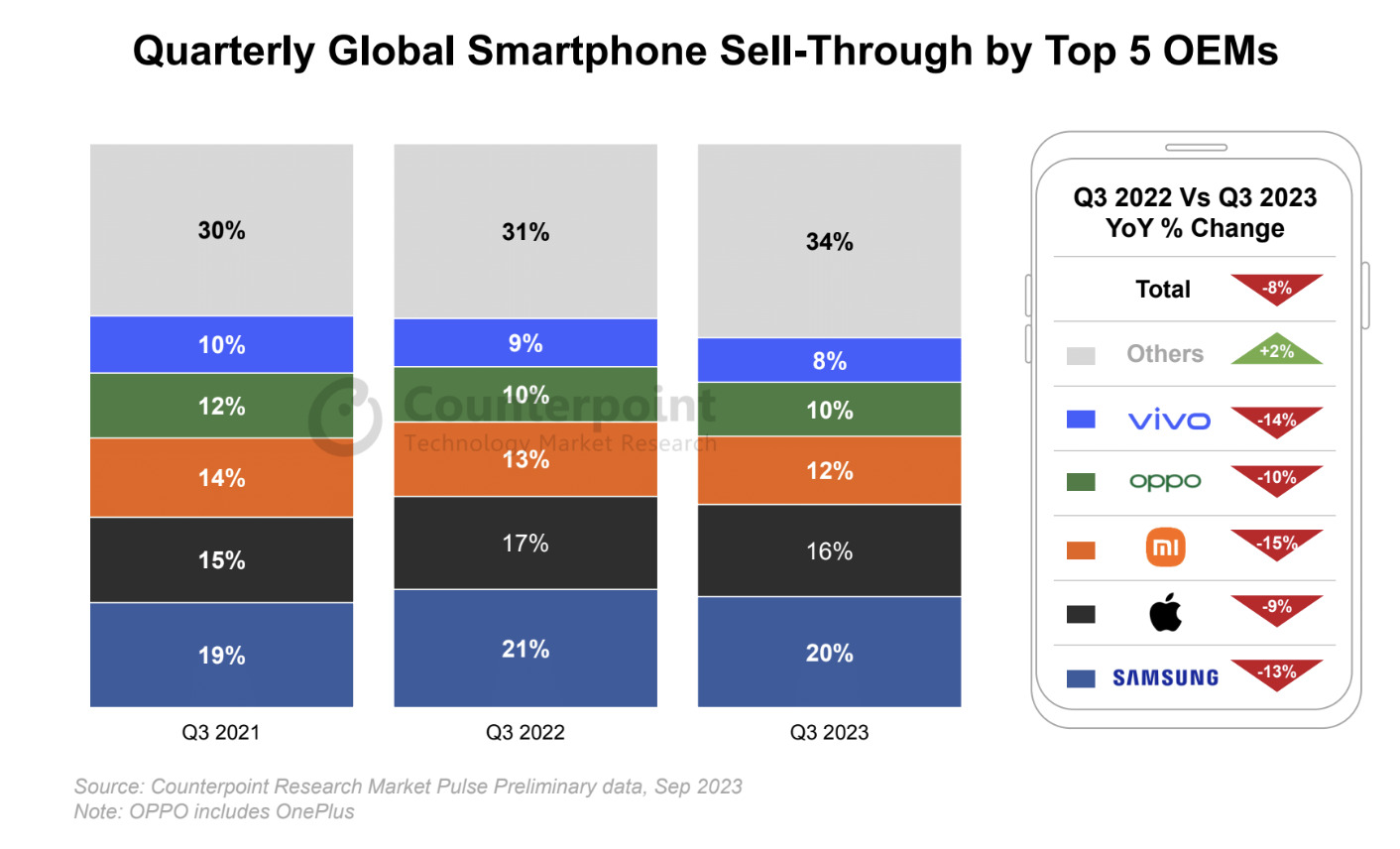
The top five global brands — which also include Chinese smartphone makers Xiaomi, OPPO, and Vivo — made up a combined 64% of the global smartphone market in the third quarter of 2023, down from about 68% in 2022 and 2021, according to Counterpoint’s data. The Chinese companies recorded even steeper smartphone sales declines than Samsung and Apple as they “worked towards strengthening their positions in key markets like China and India while continuing to slow down expansionary efforts in overseas markets,” the report noted.
HONOR, Huawei and Transsion Group gained share and were among the only brands to record YoY growth in Q3. Huawei grew driven by the launch of the Mate 60 series in China, while HONOR’s growth was led by strong overseas performance. Transsion brands continued to expand while also benefiting from the recovery in the Middle East and Africa (MEA) market.
MEA was the only region to record YoY growth in Q3, owing to improvements in macroeconomic indicators. Most developed markets, like North America, Western Europe and South Korea, recorded steep declines. However, we expect most developed markets to grow in Q4 largely due to the delayed effect of the iPhone launch.
Following a strong September, we expect the momentum to continue till the year-end, beginning with the full impact of the iPhone 15 series along with the arrival of the festive season in India, followed by the 11.11 sales event in China and ending with the Christmas and end-of-year promotions across regions. In Q4 2023, we expect the market to halt its series of YoY declines.
However, the market is expected to decline for the full year of 2023, reaching its lowest level in the decade largely due to a shift in device replacement patterns, particularly in developed markets. Notably, the recovery of emerging markets before the global market and the growth of brands outside of the top five indicate the shifting dynamics and opportunities in the global smartphone market.
About Counterpoint Research:
Counterpoint Technology Market Research is a global research firm specializing in products in the TMT (technology, media, and telecom) industry. It services major technology and financial firms with a mix of monthly reports, customized projects, and detailed analyses of the mobile and technology markets. Its key analysts are seasoned experts in the high-tech industry.
References:
Global Smartphone Market Reaches its Lowest Q3 Levels in a Decade; Apple’s Share at 16%
Omdia: Global smartphone shipments decline in 2Q23 for 8th consecutive quarter
GfK: Global telecom market (x-North America) posts 9.7% revenue drop; smartphone revenues -10.2% in 2022
IDC: Global smartphone market will remain challenged through 1st half of 2023
Dish Wireless with Qualcomm Technologies and Samsung test simultaneous 5G 2x uplink and 4x downlink carrier aggregation
Dish Wireless collaborated with Qualcomm Technologies and Samsung to successfully test simultaneous 5G 2x uplink and 4x downlink carrier aggregation (CA) using FDD spectrum. DISH achieved 200 Mbps uplink peak speeds with just 35 MHz of 5G spectrum. The DISH 5G network executed 1.3 Gbps downlink peak speeds with just 75 MHz of 5G spectrum, both across FDD bands n71, n70 and n66. Boost Mobile and Boost Infinite subscribers will soon benefit with even faster download and upload speeds on America’s Smart Network™.
This test was completed in both DISH labs and the field using a mobile phone form-factor test device powered by Snapdragon® X75 5G Modem RF System from Qualcomm Technologies [1.] and Samsung’s 5G vRAN solution as well as dual- and tri-band radios across the DISH 5G network.
Note 1. Qualcomm’s Snapdragon X75is currently sampling to customers with commercial devices expected to launch later this year.
“It’s been a pleasure to work closely with DISH Wireless and support their expanding cloud-native Open RAN virtualized network as 5G services are now live across several markets, clearing the path for even lower latency and faster speeds,” said Mark Louison, executive vice president and general manager, Networks Business, Samsung Electronics America. “We are committed to pushing the boundaries to advance network capabilities to meet growing consumer demands for our customers.”
“We look forward to continued collaborative efforts with industry partners such as DISH and Samsung to enable faster 5G around the world,” said Sunil Patil, vice president, Product Management, Qualcomm Technologies, Inc. “As consumers demand increases for uplink heavy applications, carrier aggregation on FDD spectrum is crucial to bring faster upload speeds to more consumers across markets and networks.”
……………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………
DISH claims its “Open RAN cloud-native 5G network is changing the way the world communicates,” but we don’t believe that is happening and we are not proponents of OpenRAN.
“The DISH 5G Open RAN network now covers over 73% of the U.S. population 5G broadband coverage and more than 100 million Americans 5G voice service – VoNR – with more markets going live each month,” said Eben Albertyn, EVP and CTO, DISH Wireless. “By successfully delivering 5G 2x uplink and 4x downlink carrier aggregation for FDD spectrum, DISH is now poised to deliver a better customer experience across our 5G standalone network. We look forward to continuing to pave the way to fully harness the power of 5G.”

……………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………
According to Daryl Schoolar, analyst and director at Recon Analytics, this achievement is significant for Dish because while operators have been able to do downlink CA using multiple FDD bands, uplink CA is very new. DISH’s announcement comes just a little over a month after Qualcomm and Samsung announced that they had completed the world’s first simultaneous 5G 2x uplink and 4x downlink CA for FDD spectrum. Qualcomm and Samsung noted at the time that this development was important because it gives operators with fragmented FDD spectrum assets more flexibility and makes it possible for them to deliver faster upload and download speeds. Traditionally, uplink CA has been accomplished by combining FDD+TDD or TDD+TDD configurations.
Uplink capacity is becoming more critical as more consumers use uplink-heavy applications such as social media posting and video conferencing. Indeed, the possibility of delivering peak uplink speeds of 200 Mbps is quite a sizable increase from typical uplink speeds that are measured on wireless networks today. In Ookla’s Q3 2023 report on U.S. wireless networks, it reported that T-Mobile had the fastest median upload speed in the U.S. with speeds of just 11.31 Mbps.
……………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………
About DISH Wireless:
DISH Wireless, a subsidiary of DISH Network Corporation (NASDAQ: DISH), is changing the way the world communicates with the Boost Wireless Network. In 2020, the company became a nationwide U.S. wireless carrier through the acquisition of Boost Mobile. DISH continues to innovate in wireless, building the nation’s first virtualized, O-RAN 5G broadband network, and is inclusive of the Boost Infinite, Boost Mobile and Gen Mobile wireless brands.
For company information, go to about.dish.com
……………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………
References:
https://www.fiercewireless.com/wireless/dishs-technical-breakthrough-means-faster-speeds-customers
https://en.wikipedia.org/wiki/5G_NR_frequency_bands
Dish says its 5G network now covers 70% of the U.S. population
Dish Network to FCC on its “game changing” OpenRAN deployment
Dish Network & Nokia: world’s first 5G SA core network deployed on public cloud (AWS)
WSJ: Has 5G Lived Up to Expectations?
Hundreds of billions of dollars have been invested worldwide in 5G. What was the return on that huge investment? As we forecasted five years ago and ever since then, 5G hasn’t revolutionized whole swaths of the economy the way past mobile technologies did.
…………………………………………………………………………………………………………………………….
Opinion: Network operators and 5G vendors promised too much and under delivered. 3GPP and ITU-R WP 5D are partially to blame for the commercial failure of 5G.
In particular, URLLC- the key 5G use case- could not be realized because 3GPP Release 16 spec for Enhancements for URLLC in the RAN wasn’t complete and so could not be implemented. Those enhancements were to enable URLLC end points to realize ITU-R M.2410 performance requirements, e.g. <1 ms latency in the data plane and <10 ms latency in the control plane.
Also, the 3GPP specs for 5G Architecture did not include implementation of 5G SA Core network, but instead provided many options. Hence, there are many versions of 5G SA Core networks, with many major network operators, e.g. AT&T and Verizon, still using 5G NSA (with LTE infrastructure for everything but the RAN).
ITU-R M2150, the terrestrial 5G RIT/SRIT recommendation, did not meet the M.2410 URLLC performance requirements (due to absence of 3GPP Rel 16 URLLC in the RAN spec), Also, it was not accompanied by the companion recommendation M.1036 issue 6 IMT Frequency Arrangements, which could not be agreed upon till a few months ago (it’s expected to be approved by ITU-R SG 5 meeting this November). As a result, there were no standard frequencies for 5G. That resulted in a “frequency free for all” where administrations like the FCC chose frequencies for 5G that were not agreed upon at WRC’19 and assigned to ITU-R WP 5D to specify the frequency arrangements.
For sure, the U.S. wireless carriers offering 5G service have not had anywhere near a good ROI. That’s indicative of the decline in their stock prices this year. Despite an 8.67% dividend, Verizon (VZ) stock has lost -16.39% YTD through Friday Oct 13th. AT&T (T) stock has performed slightly worse with a -16.74% YTD total return. The Dow Jones U.S. Telecommunications Index is -17.34% YTD through Friday.
…………………………………………………………………………………………………………………………….
In markets with widespread 5G, cellphone users often fail to notice a difference in service compared with 4G-LTE. This author has had a 5G Samsung Galaxy phone for over one year and does not notice any difference from 4G-LTE.
A key growth opportunity for 5G—businesses installing private networks in places such as manufacturing plants and arenas—has yet to take off.
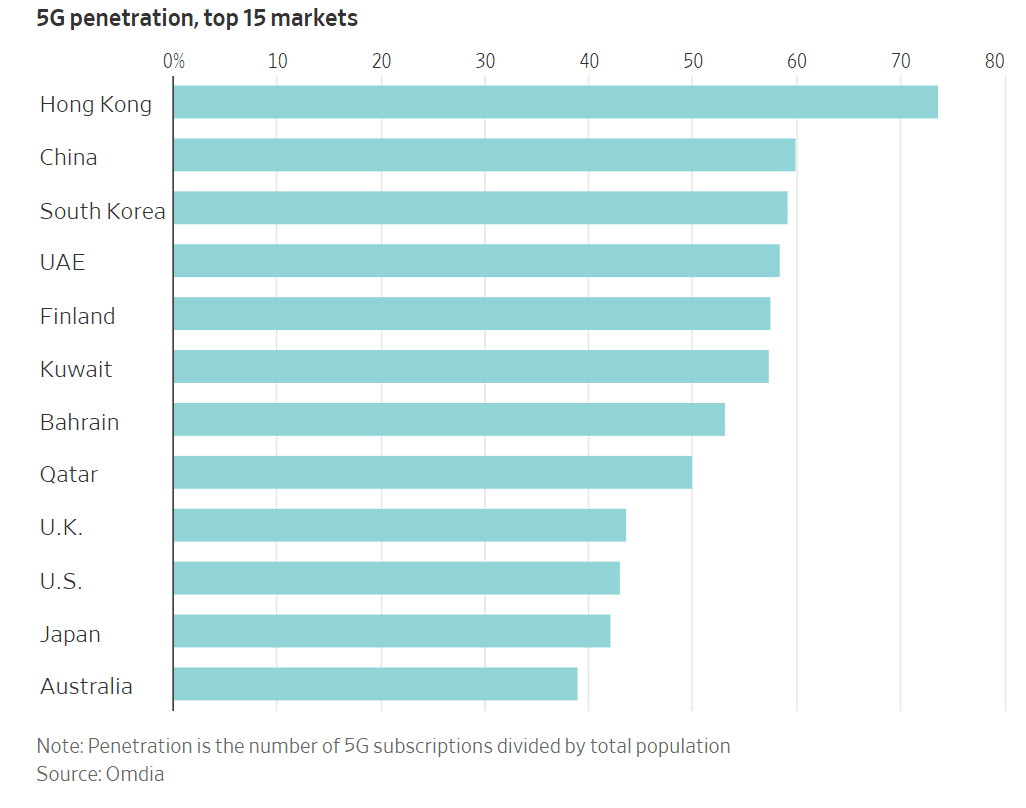
In the U.S., about 43% of people had 5G mobile subscriptions as of June, ranking 10th worldwide, according to estimates from research firm Omdia. Hong Kong had the world’s highest 5G penetration rate, with 74% of its population subscribed to the mobile service. Ranked second- and third-highest in the world were mainland China and South Korea, which registered 5G mobile-subscription rates of 60% and 59%, respectively.
The high uptake in China and its neighbors is no accident. Smartphone users in several Asian countries have benefited from affordable next-generation devices, strong fiber-optic infrastructure and government policies that encouraged broad 5G cellular coverage. China and South Korea also host technology giants like Huawei and Samsung that are spearheading the wireless technology’s advancement.
Finland had the highest 5G penetration rate in Europe, at 58%, while the United Arab Emirates led the Middle East, also with 58%.
Getting “4G for all, not 5G for few,” has been the mantra for the past two years at Veon, a network operator that serves cash-strapped markets from Ukraine to Bangladesh.
The Amsterdam-based company has already covered 90% of the six countries it serves with 4G signals. Some areas lack the fiber-optic-cable infrastructure to support 5G-capable cellphone towers, and roughly half of the population in those markets lacks even a smartphone, let alone one capable of picking up 5G connections. Some countries also impose high taxes on smartphones, which puts the devices out of reach for many consumers, says Veon Chief Executive Kaan Terzioğlu.
“This is really matching the needs of the markets with the technologies that are available,” Terzioğlu told the WSJ. Spending money on 5G infrastructure before the people it covers are ready to tap it “would be irresponsible,” he added.
 Business owners and executives in many poorer countries say they wouldn’t plan around ultrafast wireless connections in places where 2010 technology is still the norm. “There’s not enough coverage or towers here,” says Nicholas Lutchmiah, retail manager at Topbet, a licensed gambling bookmaker and sports-betting company in South Africa, which has most of its shops in poorer townships and rural areas. “That’s the biggest problem that we face. In rural areas and townships, we get 3G, which is rather slow.”
Business owners and executives in many poorer countries say they wouldn’t plan around ultrafast wireless connections in places where 2010 technology is still the norm. “There’s not enough coverage or towers here,” says Nicholas Lutchmiah, retail manager at Topbet, a licensed gambling bookmaker and sports-betting company in South Africa, which has most of its shops in poorer townships and rural areas. “That’s the biggest problem that we face. In rural areas and townships, we get 3G, which is rather slow.”
Despite the limitations, some developing countries have invested heavily in 5G technology. Indian telecom companies have committed tens of billions of dollars to the latest network technology and making a push for ultracheap smartphones, for instance. Domestic conglomerate Reliance Industries has led much of its country’s aggressive telecom investments through its Jio brand, the spearhead of leader Mukesh Ambani’s ambition “to connect everyone and everything, everywhere.”
The wireless companies that invested in 5G technology early paid handsomely to refresh their networks. and they have the balance sheets to prove it. The world’s biggest wireless companies—excluding China’s state-backed operators—carried $1.211 trillion of corporate debt at the end of 2022, up from $1.072 trillion four years earlier, according to Moody’s Investors Service.
The credit-rating service said that those companies spent more than in past years building up their wireless networks and issued more debt to finance big spectrum purchases. The price of that spectrum has varied but generally risen. One auction raised $19 billion in India while another group of licenses fetched $81 billion in the U.S.
Debt is nothing new to big telephone networks. The capital-intensive companies have historically run through cycles of heavy upfront spending on new equipment and installation before paying down the tab over time through reliable subscription fees; phone and internet service is a modern necessity, after all.
But securing airwaves for new 5G signals has forced companies to speed up their borrowing. “There’s a lot of debt on these companies,” Moody’s analyst Emile El Nems says. “We’re not ringing the alarm bells, but we’re saying there’s limited flexibility for an accident.”
Executives at telecom companies that borrowed the most to amass 5G-friendly spectrum licenses have said that they made prudent investments to meet customers’ demand for mobile bandwidth, and that their biggest spending is behind them, at least in the near term.
China moved early to enhance its national infrastructure, blanketing the country with 5G base stations as soon as manufacturers started making them. The country’s three major mobile-phone carriers anchored those transmitters to a dense network of fiber-optic cables and encouraged a range of businesses from seaports to coal mines to use the ultrafast connections. It has also provided subsidies and regulatory support to telecom operators and tech companies, facilitating their growth and enabling them to compete on a global scale.
At the end of June, 5G base stations in the country connected 676 million 5G phones and more than 2.12 billion Internet of Things devices, China’s central-government officials said in a press conference in July.
U.S. officials offered their national cellphone carriers fewer direct subsidies than their Beijing counterparts, but policy makers granted many requests on the companies’ wish lists. Trump administration appointees fast-tracked auctions of 5G-capable wireless frequencies and consolidated the wireless sector by approving T-Mobile’s takeover of rival Sprint, a deal that the company and government leaders said would accelerate long-planned network upgrades.
At the same time, the U.S. has tried to persuade other countries to not buy Chinese gear—an effort that prompted some governments to ban its telecom equipment. But China’s homegrown supplier, Huawei, has weathered the U.S. efforts and played a pivotal role in both the domestic and global 5G markets. At the same time, they have turned away from Western suppliers like Qualcomm for some components and are now relying on domestic suppliers.
Huawei remains the world’s largest seller of telecom equipment, commanding about a third of the global market, with sales about twice those of the second- and third-ranked suppliers, Nokia and Ericsson, according to market-research firm Dell’Oro Group.
What happened to businesses being big 5G consumers?
One of 5G’s most alluring promises remains the private network: a system built to the same standard as a high-speed cellphone service but tailored for a business operating in a smaller area like an office, farm or factory. Those networks can connect a range of computers, sensors and robotics without the hassle and cost of hooking them up with wires.
For now, though, companies have been slow to adopt private networks. Consider “the factory of the future” that Ford and Vodafone previewed outside London in 2020. The companies detailed plans for a swarm of mobile robot welders receiving orders over superfast 5G connections, so they could assemble electric cars more quickly and precisely than traditional equipment.
Three years later, the factory of the future is still just a concept. Ford doesn’t use the high-tech wireless standard on its production line, and Vodafone says it ended its proof-of-concept project with the American automaker. A Ford spokesman didn’t respond to a request for comment.
In total, organizations have built more than 750 private cellular networks around the world, according to Besen Group, a private-network consultancy. Installations run the gamut from college campuses to open-pit mines, though many of them use less-advanced 4G gear instead of the latest-generation electronics.
That is partly because of a chicken-or-the-egg problem with private networks. A device maker might not want to create 5G gear for factories until more factories have installed cellular networks. But factory owners don’t want to invest in those networks unless there are enough 5G-ready devices on the market to justify the upgrade.
“This is actually fairly typical for new network equipment,” says Vodafone cloud and private-network chief Jenn Didoni. “The devices will certainly come, but there aren’t as many as in 4G, and they aren’t as tested and understood.”
Dell’Oro estimates that private networks make up less than 1% of the market for the relevant 5G equipment, but the research firm predicts that early revenue will grow, on average, at a 25% annual rate over the next five years as more connected gadgets hit the market.
“In the beginning, a lot of the conversations used to be about feasibility,” says Durga Malladi, a senior vice president at chip maker Qualcomm. “If I am interested in moving robots and overhead cranes using 5G, can I even get the same level of reliability and latency that I have expected from just wired? And the answer to that is, in almost all instances, absolutely yes.”
Many industries have yet to experience the market disruption that 5G’s boosters promised. A notable exception: Some telecom companies are enjoying a windfall from wireless bandwidth improvements at the expense of their cable-internet rivals.
Mobile network carriers like T-Mobile and Verizon have used new high-speed wireless equipment to beam internet service straight into customers’ homes, racking up more than five million new subscriptions altogether in under three years. The over-the-air service has dented cable-industry revenue and forced companies to compete in areas where they were once the only game in town.
Telecom companies have long known how to beam internet connections into people’s homes without the considerable expense of new wires and equipment. But wireless companies faced an uphill fight against their hard-wired competitors until 5G improvements brought advances such as more-efficient signals that could run through the same cell-tower antennas that companies were already installing to connect cellphones.
That helped mobile-network operators quickly rack up home-internet customers at much lower variable costs, especially in America, where cable companies’ dissatisfied customers offer a juicy target.
“The U.S. is very unusual because we pay so much for home broadband,” says Jeff Heynen, an analyst for Dell’Oro. “The way T-Mobile and Verizon are addressing the service, clearly you know who they’re going after.”
Markets with many far-flung customers, like Australia and Saudi Arabia, could soon follow the U.S. lead in 5G home-internet service, Heynen adds. Industry experts warn that the booming wireless-broadband business isn’t going to replace cable soon, however.
Capacity is the main factor holding back wireless internet services. A single cellular tower can only handle so many videogames, TV streams and Zoom calls at once, even after 5G upgrades offer those towers more bandwidth to go around.
T-Mobile CEO Mike Sievert has even played down his company’s booming home-internet business, telling investors at a Goldman Sachs conference in September that the service would eventually reach a customer base in the single-digit millions. That is a sliver of the more than 100 million U.S. households that could use broadband service. “It’s a very mainstream offer, but we don’t think it’s going to take over cable and fiber,” Sievert said.
Omdia forecasts weaker 5G market growth in near term, 4G to remain dominant
5G is a big letdown and took a “back seat” at CES 2023; U.S. national spectrum policy in the works
Another Opinion: 5G Fails to Deliver on Promises and Potential
3GPP Release 16 5G NR Enhancements for URLLC in the RAN & URLLC in the 5G Core network
WSJ: 5G in South Korea has not lived up to expectations
Four years ago, South Korea led the world’s biggest rollout of 5G, promising a huge increase in network speeds that would help usher in a flurry of new technologies such as autonomous cars, augmented reality and remote surgeries. South Koreans are still waiting for that to happen.
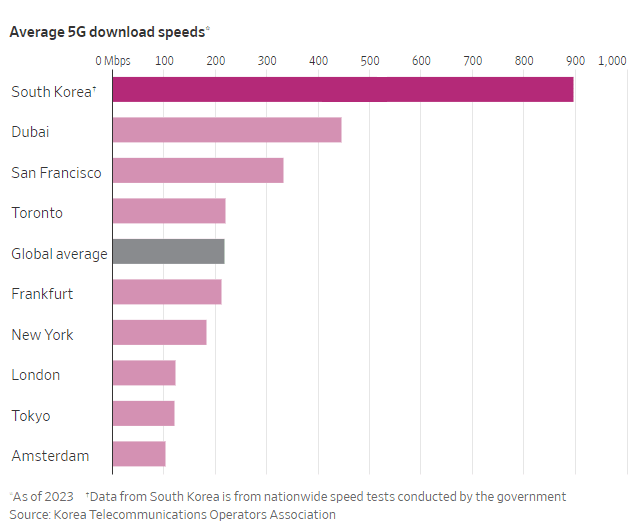
In 2022, South Korea’s average 5G download speed was 896Mbps -roughly six times that of the country’s average 4G download speed and more than double the 5G speeds of the United Arab Emirates and the U.S., according to the Korea Telecommunications Operators Association, a trade group. Despite those achievements, the network has fallen short of what was promised.
South Korea’s three major mobile carriers—SK Telecom, KT, and LG Uplus—advertised speeds up to 20 times faster than 4G LTE as they rolled out the new service, one of the world’s first commercial 5G networks, in April 2019. But, so far, such speeds can be achieved only on localized networks with limited coverage, and aren’t being pursued for wider use. Many consumers in South Korea were left underwhelmed by the minor improvements in speed and spotty connections. The network’s quality and speed have since improved with technologies such as “standalone 5G” (5G SA) that runs on its own network infrastructure rather than relying in part on those of 4G. Still, subscriber growth for 5G service has been slower than it was for 4G, and many of the visionary services talked about in the country haven’t come around.
South Korea’s nationwide 5G network experience has improved since the new network’s introduction, and driven more data usage. But technical hurdles and cost constraints have limited the ability to offer on a wide scale the type of 5G capable of even faster speeds, according to industry analysts and some of the South Korean carriers themselves.
Some of the difficulties stem from the frequencies at which radio waves travel. Countries around the world have enabled their 5G networks on different frequency bands, with most choosing low- or mid-frequency bands. South Korea’s main telecom firms developed their public 5G networks on the 3.5-gigahertz band, a mid-frequency band.
At the same time, 5G can be enabled on the high-frequency bands supporting millimeter wave, the type touted at 5G’s inception that can provide more-extreme boosts in speed. But a significant downside is that millimeter waves don’t travel well across long distances and through obstacles such as trees, buildings and glass. Thus, networks with the highest speeds are more challenging and expensive to deploy at scale.
South Korean telecom firms chose not to use the 28-gigahertz band, a high-frequency band supporting millimeter waves, in deploying nationwide 5G networks. Under this network environment, the latest smartphones currently sold in the country also do not come with the antenna system supporting this band.
The three telecom firms recently lost their licenses for the 28-gigahertz band after they didn’t meet the mandatory set number of 5G base stations using that band that needed to be built in order to keep the licenses. Now, the government is looking to grant 28-gigahertz licenses to nontelecom entities looking to use the band for 5G services in locations they deem as fit.
In May, South Korea’s Fair Trade Commission collectively fined the country’s three carriers about $24.8 million for allegedly using misleading advertising that exaggerated the speed of their 5G networks at their launch. The promoted speeds were a target that couldn’t be achieved in everyday usage environments, the South Korean FTC said in its decision.
South Korea’s apparent retreats in millimeter-wave 5G development put the country’s 5G leadership at risk, says a recent report from OpenSignal, a mobile-analytics company that monitors and analyzes the global telecom industry.
- LG Uplus says that the 28-gigahertz band’s properties made it costly and technologically difficult to deploy at a mass scale, and that the company would continue to work on improving the quality of its 5G services.
- SK Telecom says it will continue improving its 5G services, though it notes that South Korea boasts the world’s top 5G services in terms of speed and coverage and that consumers are using more data at lower costs.
- KT declined to comment.
This doesn’t mean the millimeter-wave band has lost its commercial appeal. Today, it is being used around the world—albeit in only a handful of cases—to enable ultrafast 5G in a fixed area, such as a sports arena, airport or smart factory, industry analysts say. Major telecom operators in the U.S. and Japan are using high-frequency mmWave bands for Fixed Wireless Access (FWA) or as one of the ways of enabling their 5G networks in dense urban locations, though coverage made available through these bands is limited to small areas and line of sight communications.
In South Korea, meanwhile, the 28-gigahertz band is being used to support some private 5G networks serving specific needs. One network, for example, supports autonomous robots at a local tech company and another assists augmented-reality technologies in surgery. Special licenses were issued in both cases. The 28-gigahertz band also is being used inside parts of Seoul’s subways, a government-led project that involved the three telecom companies. But whether that network will continue to operate, given the revocation of the three carriers’ 28-gigahertz licenses, remains to be seen.
At its beginnings, 5G was touted as a technology that would usher in a new era of smart cities, autonomous driving and holograms. But even in South Korea, where 5G adoption is higher than elsewhere, those new services are being pursued but haven’t taken off widely. Low market demand, the limited availability of devices that would support 5G as well as regulatory barriers all made it difficult for related services to go mainstream, said SK Telecom, the largest of South Korea’s three telecom firms, in a rare 6G white paper that outlined some key takeaways from 5G.
That is partly a chicken-and-egg problem, says Julian Gorman, head of Asia-Pacific for GSMA, a trade association for mobile carriers. Developers are often reluctant to invest in new products for a developing technology like 5G, especially the type using millimeter waves on the high-frequency bands. In turn, telecom providers see a weaker business rationale for investing aggressively in widespread millimeter-wave 5G coverage, he says.
The usage scenarios presented at 5G’s inception were more of a demonstration of the technology rather than solid proof that there was a business need to do so, Gorman says, adding that the 5G ecosystem is still trying to determine what types of new services and technologies are wanted in the market.
The lack of 5G killer apps also feeds into a bigger trend: 5G has been a harder sell than 4G. That’s mainly because URLLC does not meet the advertised ITU-R M.2410 performance requirements. So there are no mission critical, ultra low latency/real time applications that can use 5G.
In South Korea, the number of 5G subscribers surpassed 30 million in April this year, roughly four years after 5G’s initial introduction. But with 4G, that same milestone was reached after about 2½ years, according to data from the Ministry of Science and ICT (information and communication technology).
That is a trend echoed globally as well. As of 2022, about 32% of smartphones in circulation worldwide were 5G-capable, but just 45% of those phones were activated on a 5G network, down from 55% a year earlier, according to Omdia. This partly shows that more people are upgrading to 5G phones without necessarily choosing a 5G plan, in addition to 5G not being available yet in some places, it said.
“People are simply not ready to pay more for 5G, because they’re totally content with 4G,” which many consider sufficient for doing things like streaming video, says De Renesse of Omdia. “Many still ask, why would I pay more for doing the same thing?” he says.
References:
https://www.wsj.com/business/telecom/south-korea-5g-what-happened-9790b873
South Korea has 30 million 5G users, but did not meet expectations; KT and SKT AI initiatives
South Korea government fines mobile carriers $25M for exaggerating 5G speeds; KT says 5G vision not met
Omdia: ARPU declining or flat for South Korean 5G network operators
Opensignal: South Korea leads in 5G download speed; Philippines posts highest improvement in 5G video experience
Starlink’s Direct to Cell service for existing LTE phones “wherever you can see the sky”
Satellite internet provider Starlink, owned by SpaceX, has quietly started advertising its “Direct to Cell” service on its website, promising connectivity to existing LTE phones “wherever you can see the sky.”
No changes to hardware, firmware, or special apps are required, providing seamless access to text, voice, and data. Starlink will offer text services in 2024, followed by voice, data and IoT connectivity in 2025.
Subscribers will be able to use their existing LTE phone to tap into the satellite service, the obvious benefit being if you are out in the wilderness somewhere without terrestrial coverage.
Source: Starlink
…………………………………………………………………………………………………………………………………………………………………………
Direct to Cell satellites will initially be launched on SpaceX’s Falcon 9 rocket and then Starship. On orbit the satellites will immediately connect over laser backhaul to the Starlink constellation to provide global connectivity.
Starlink satellites with Direct to Cell capability are loaded with an eNodeB modem that acts like a cellphone tower in space, ‘allowing network integration similar to a standard roaming partner.’
In August last year, at SpaceX’s launch facility, Elon Musk and T-Mobile CEO Mike Sievert announced ‘Coverage Above and Beyond’ a joint project which promised to ‘bring cell phone connectivity everywhere.’
The project appears to have experienced a name change in the intervening time, and additional operator partners are now listed on the new webpage as Optus in Australia, Rogers in Canada, One NZ in New Zealand, KDDI in Japan, and Salt in Switzerland.
As was the case with that initial launch, the details of what level of connectivity might be possible using this method remains vague – there was no actual announcement or press release for service which might have yielded such specifics.
Peter Kibutu, Advanced Technology Lead – NTNs at TTP told Telecoms.com: “Starlink continues to set ambitious targets for its satellite network, however, its plans to deliver a direct-to-cell service requires scrutiny. Offering connectivity supported by unmodified 4G handsets might only result in low-bandwidth data and voice services, falling short of contemporary data demands and user experience.
“Delivering satellite connectivity akin to what we can experience today on 4G and 5G devices will require the 3GPP-compliant 5G NR NTN waveform, which is continuously optimised to maximise the performance of direct to handset services over LEO satellite constellations. Starlink has made it clear that it will continue to use its own proprietary technology which, while providing it with speed to market, could present roadblocks in years to come as it struggles to support high-performance connectivity services and use cases that will be readily available via other satellite operator’s 5G NTN networks. It will be interesting to see if Starlink will also be looking to develop services that leverage industry best practices and incorporate a wider ecosystem.”
There are no details on pricing or any other details, so we really don’t know exactly what Starlink Direct to Satellite service entails and how it compares to rival satellite connectivity ventures.
References:
https://telecoms.com/524273/starlink-indicates-its-satellite-to-phone-service-will-drop-next-year/
https://www.starlink.com/business/direct-to-cell
Comcast’s DOCSIS 4.0 Deployment: Multi-Gig Symmetrical Speeds to be offered across the U.S.
Next week, Comcast will begin to deploy DOCSIS 4.0 technology (described below) which can deliver multi-gigabit symmetrical speeds to customers over the connections that already exist in tens of millions of homes in Comcast markets across the country. Xfinity customers in Colorado Springs will be able to sign up online for the new DOCSIS 4.0-powered Internet plans next week.
As a part of the launch, Comcast will introduce a new portfolio of symmetrical products for residential customers. Comcast will begin rolling out DOCSIS 4.0 to select neighborhoods in Colorado Springs, CO, and will launch new markets throughout the country over the next few years. Select areas of Atlanta, GA and Philadelphia, PA are expected to begin rolling out before the end of this year.
“The ubiquity of our network, which is already accessible to tens of millions of homes, provides us with an incredible opportunity to bring multi-gigabit upload and download speeds to communities across the country with the scale and efficiency that no other provider can replicate,” said Dave Watson, President & CEO, Comcast Cable. “Our connectivity experience, powered by the Xfinity 10G Network, will allow us to deliver speeds up to 10 Gbps over our traditional network to virtually all our customers, plus even better reliability, lower latency, and the best in-home WiFi coverage.”
“We’re entering the next phase of this industry leadership with DOCSIS 4.0 technology to introduce X-Class Internet products that will revolutionize the way our customers get online today and many years into the future,” Watson added.

Symmetrical 10 Gbps service based on fiber-to-the-home (FTTH) technology is already available in all of Comcast’s markets, and as part of its continued network evolution and the introduction of DOCSIS 4.0, multi-gig symmetrical speeds are rolling out.
New and existing residential customers connected via DOCSIS 4.0 will have access to Comcast’s newly introduced next-generation X-Class Internet portfolio. X-Class speed tiers include X-300 Mbps, X-500 Mbps, X-1 Gbps and X-2 Gbps upload and download speeds and low lag for the ultimate live sports streaming experience on Peacock, smooth connections on work calls, and ultra-responsive gaming.
The DOCSIS 4.0 launch is the latest in a long line of world firsts that Comcast has spearheaded in the effort to implement DOCSIS 4.0. In April 2021, Comcast conducted the first-ever live test of full duplex DOCSIS and later that year tested the world’s first 10G connection all the way from the network to a modem. In 2022, Comcast conducted a world-first live trial and connected a business location in the Philadelphia region to its live network including a DOCSIS 4.0-enabled 10G node and multiple cable modems. In February 2023, the company marked another major milestone in the nation’s largest and fastest multi-gig deployment by announcing its latest Xfinity 10G Network upgrade launched to 10 million homes and businesses.
In addition to Comcast’s efforts to deploy DOCSIS 4.0 and other 10G upgrades across its footprint, the company continually invests in delivering a superior connectivity experience that is not only fast but is also reliable with less lag.
- Award Winning Tech – Comcast has lead the industry in deploying technologies within its network to enhance speed, reliability and latency like distributed access architecture (DAA) and a vCMTS, which earned an Emmy® Award for Technology and Engineering.
- Smart Network – Comcast-developed technology like Comcast Octave and Xfinity Fiber Meter (XMF), enables optimized network performance by proactively identifying and even repairing network impairments that impact customers’ services.
- Storm-Ready WiFi – In August 2023, Comcast introduced Storm-Ready WiFi, the first product of its kind offered by an Internet provider designed to maintain a connection during a power or local outage.
- Low Latency – Deployed Active Queue Management (AQM) system nationally and currently trialing the latest CableLabs low latency DOCSIS (LLD) specification.
DOCSIS Technology
Data Over Cable Service Interface Specification (DOCSIS) was first introduced in 1997 as a solution for high-speed data to be transmitted over existing cable wires, replacing dial-up phone lines for an Internet connection. Comcast has been a leader in deploying DOCSIS updates to deliver faster speeds to all the homes and businesses in its service areas. In early 2016, Comcast was the first to introduce DOCSIS 3.1-powered Gigabit Internet service and rapidly expanded Gigabit speeds across the country to more locations than any other provider.

References:
Fiber Connect 2023: Telcos vs Cablecos; fiber symmetric speeds vs. DOCSIS 4.0?
Comcast launches symmetrical 10-Gigabit speeds over Ethernet FTTP
Comcast demos 10Gb/sec full duplex with DOCSIS 4.0; TDS deploys symmetrical 8Gb/sec service
Comcast to roll out DOCSIS 4.0 and Multi-Gig speeds in 2023; Fiber (not FWA) is the real competitor
Precision Optical Technologies (OT) in multi-year “strategic partnership” to upgrade Charter Communications optical network
Rochester, N.Y., based Precision Optical Technologies (OT) has struck a multi-year “strategic partnership” with Charter Communications to upgrade the latter’s optical network. In alignment with Charter’s Distributed Access Architecture (DAA) network expansion and operational enhancement initiatives, this collaboration will see the deployment of nearly all of Precision OT’s active and passive portfolio of solutions; to include 10G DWDM tunable optics, 100G and 400G optics, Bluetooth® DWDM tuning modules, passive connectivity solutions and more. Precision OT didn’t announce the financial terms of the agreement.
Charter plans to upgrade about 85% of its HFC plant using a distributed architecture paired with a virtual cable modem termination system (vCMTS) and “high-split’ upgrades that dedicate more spectrum to the DOCSIS upstream. About 50% of Charter’s HFC plant will be upgraded to 1.2GHz of capacity and 35% will upgrade to 1.8GHz and a full deployment of DOCSIS 4.0. The remaining 15% of Charter’s footprint will be moved to 1.2GHz with a high-split but forgo DAA and a vCMTS.
Greg Mott, SVP Field Operations Engineering at Charter Communications said of the partnership, saying: “The team at Precision OT has a clear understanding of Charter’s broadband network evolution — cost, scale, and speed — and their mix of solutions will help us deliver on our commitments across our 41-state service area.”
Charter has also tapped Harmonic for the vCMTS component and selected Vecima Networks’ DAA platform, including remote PHY nodes. ATX Networks, which recently introduced a 1.8GHz platform that can be used to upgrade legacy Cisco nodes, is also expected to be in the mix at Charter. Teleste, a Finnish supplier that is boosting its investment in the North American cable market as operators push ahead with DAA and D4.0 upgrades, also has projects underway with Charter, according to industry sources.

………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………….
With a global footprint, Precision OT currently serves a diverse range of customers across various industries worldwide. Among its clientele are leading broadband service providers in North America, Europe, Latin America, and beyond. This partnership further solidifies Precision OT’s reputation as a trusted partner and solutions provider in the telecommunications and optical technology sectors.
“We are pleased that Charter Communications has chosen Precision OT as a trusted technology partner to deploy cutting-edge optical networking solutions,” said Keith Habberfield, SVP of Sales & Marketing at Precision OT. “Optics and their components are the integration point that enables networks to communicate. We provide a suite of solutions that work in all of Charter’s identified use-cases; this drives measurable operational simplicity and speeds deployments for their project.”

About Charter Communications:
Charter Communications, Inc. (NASDAQ:CHTR) is a leading broadband connectivity company and cable operator serving more than 32 million customers in 41 states through its Spectrum brand. Over an advanced communications network, the Company offers a full range of state-of-the-art residential and business services including Spectrum Internet®, TV, Mobile and Voice.
For small and medium-sized companies, Spectrum Business® delivers the same suite of broadband products and services coupled with special features and applications to enhance productivity, while for larger businesses and government entities, Spectrum Enterprise® provides highly customized, fiber-based solutions. Spectrum Reach® delivers tailored advertising and production for the modern media landscape. The Company also distributes award-winning news coverage and sports programming to its customers through Spectrum Networks. More information about Charter can be found at corporate.charter.com.
About Precision OT:
Precision OT is a systems integration company focused on end-to-end optical networking solutions, network design services and cutting-edge product development advancements. Backed by our extensive experience and robust R&D efforts, we play an integral role in enabling next-generation optical networks worldwide. For more information, visit www.precisionot.com.
References:
https://www.fiercetelecom.com/broadband/charter-plots-3-year-upgrade-deploy-docsis-40-2025
Charter Communications selects Nokia AirScale to support 5G connectivity for Spectrum Mobile™ customers
T-Mobile and Charter propose 5G spectrum sharing in 42GHz band
Comcast Xfinity Communities Wi-Fi vs Charter’s Advanced Wi-Fi for Spectrum Business customers
Ligado Networks and Ubiik to offer private LTE network using Band 54 spectrum at 1670-1675 MHz
U.S. satellite communications service provider Ligado Networks plans to offer a private LTE network using advanced metering infrastructure (AMI) from Taiwan based Ubiik. Using Band 54 spectrum at 1670-1675 MHz, the private LTE network is intended for the utilities sector and other mission-critical customers. Band 54 is standardized for 3GPP-based cellular technologies; it is available contiguously across the US.
Ubiik gained considerable success in Taiwan, including a $17 million tender from Taiwan Power Company (Taipower) at the start of 2023. The company has developed a private LTE base station for Band 54 spectrum, under the brand goRAN; the 5MHz chunk at 1670-1675 MHz, affording time-division (rather than frequency division) duplexing (TDD), is presented as a useful private network addition for low-power IoT projects.
On October 6th, Ubiik partnered with Electricity Canada with the aim of contributing to Canada’s clean energy future through developments in wireless connectivity. Ubiik will collaborate with Electricity Canada’s members and partners to deliver pLTE networks for utilities in Canada, using its innovative goRAN™ LTE Base Station and LTE-M end devices that support the 1.8GHz, 900MHz, and 1.4GHz spectrum.

The goRAN™ base station integrates a full-software 3GPP Release 15 Radio Access Network (RAN) optimized for private networks, with multi-carrier standalone NB-IoT support as well as standalone LTE-M in 1.4MHz, 3MHz and 5MHz bandwidths, including VoLTE. It can operate as a Base Station connecting to an external Evolved Packet Core (EPC) via the S1 interface, as well as an Access Point with its built-in EPC and integrated HSS (external HSS via S6a is also supported).
…………………………………………………………………………………………………………………………….
It is a “golden opportunity” for critical industries, said Ubiik. TDD separates the uplink and downlink signals by allocating different time slots in the same frequency band, allowing for asymmetric flow for uplink and downlink transmission. Ligado Networks said: “[It] equips utility users with significant flexibility, as different ratios of uplink versus downlink slots may be used to address requirements of mission-critical applications.”
A news release said: “The Band 54 goRAN™ LTE Base Station will be particularly useful for utilities deploying private networks which is why the companies plan to showcase a demonstration version of the device during the 2023 Utility Broadband Alliance (UBBA) Summit & Plugfest Event in Minneapolis next week from October 10-12, 2023.”
Sachin Chhibber, chief technology officer at Ligado Networks emphasized how the announcement represents another building block in the expansion of the ecosystem which utilizes Band 54 frequencies. He stated: “Ubiik’s goRAN base station is a significant enhancement to the opportunities the band affords to the critical infrastructure industry – especially utility and other enterprise organisations planning private networks… By eliminating the requirement to pair channels for uplink and downlink, we will be able to offer partners the flexibility to use the spectrum exactly how they need, and with greater efficiencies.”
Chhibber reiterated how specific attributes of Band 54 – particularly its Time Division Duplex (TDD) capabilities – equip utility users with significant flexibility, as different ratios of uplink versus downlink slots may be used to address requirements of mission-critical applications. “By eliminating the requirement to pair channels for uplink and downlink, we will be able to offer our partners the flexibility necessary to use the spectrum exactly how they need, and with greater efficiencies,” Chhibber noted. He added that uplink-heavy users such as utilities – for monitoring purposes, as an example – will be able to deploy tailormade networks to achieve their priorities.
Tienhaw Peng, chief executive at Ubiik, said: “Given the scarcity of spectrum, being able to secure an optimal 5 MHz slice to build out a private network is a golden opportunity for critical infrastructure customers. Our goRAN base station offers the perfect mix of affordability and ease of deployment combined with the spectral efficiency, interoperability and security brought by LTE. With Ligado, we look forward to providing a solution-in-a-box for building an LTE network – by either utilising a user’s specified core network or one directly built into the base station.”
Peng also explained that the goRAN™ Base Station will integrate with chipsets supporting Band 54 and with a utility-hardened LTE endpoint module currently in development. Ubiik’s recent acquisition of utility networks provider Mimomax Wireless will provide North American utilities with additional expertise in the deployment of multiple large-scale wireless networks.
Ubiik’s recent acquisition of utility networks provider Mimomax Wireless will provide North American utilities with additional expertise in the deployment of multiple large-scale wireless networks, the company said.
References:
Ligado Networks teams up with Ubiik to offer US utilities Band-54 private LTE at 1670-1675 MHz
Nokia Bell Labs claims new world record of 800 Gbps for transoceanic optical transmission
Nokia today announced it has set two new world records in submarine optical transmission, both of which will shape the next generation of optical networking equipment.
The first sets a new optical speed record for transoceanic distances. Nokia Bell Labs researchers were able to demonstrate an 800-Gbps data rate at a distance of 7865 km using a single wavelength of light. That distance is two times greater than what current state-of-the-art equipment can transmit at the same capacity and is approximately the geographical distance between Seattle and Tokyo. Nokia Bell Labs achieved this milestone at its optical research testbed in Paris-Saclay, France.
The second record was achieved by both Nokia Bell Labs and Nokia subsidiary Alcatel Submarine Networks (ASN), establishing a net throughput of 41 Tbps over 291 km via a C-band unrepeated transmission system. C-band unrepeated systems are commonly used to connect islands and offshore platforms to each other and the mainland proper. The previous record for these kinds of systems is 35 Tbps over the same distance. Nokia Bell Labs and ASN broke the record at ASN’s research testbed facility, also in Paris-Saclay.
Nokia Bell Labs and ASN presented the scientific findings behind both records on the 4th and 5th of October at the European Conference on Optical Communications (ECOC), held in Glasgow, Scotland.

Making lasers that blink faster:
Nokia Bell Labs and Alcatel Submarine Networks were able to achieve both world records through the innovation of higher-baud-rate technologies. “Baud” measures the number of times per second that an optical laser switches on and off, or “blinks”. Higher baud rates mean higher data throughput and will allow future optical systems to transmit the same capacities per wavelength over far greater distances. In the case of transoceanic systems, these increased baud rates will double the distance at which we could transmit the same amount of capacity, allowing us to efficiently bridge cities on opposite sides of the Atlantic and Pacific oceans. In the case of C-band unrepeated systems, higher baud would allow service providers connecting islands or off-shore platforms to achieve higher capacities with fewer transceivers and without the addition of new frequency bands.
The research behind these two records will have significant impact on the next generation of submarine optical transmission systems. While future deployments of submarine fiber will take advantage of new fiber technologies like multimode and multicore, the existing undersea fiber networks can take advantage of next-generation higher-baud-rate transceivers to boost their performance and increase their long-term viability.
Sylvain Almonacil, Research Engineer at Nokia Bell Labs, said: “With these higher baud rates, we can directly link most of the world’s continents with 800 Gbps of capacity over individual wavelengths. Previously, these distances were inconceivable for that capacity. Furthermore, we’re not resting on our achievement. This world record is the next step toward next-generation Terabit-per-second submarine transmissions over individual wavelengths.”
Hans Bissessur, Unrepeated Systems Group leader at ASN, said: “These research advances show that that we can achieve better performance over the existing fiber infrastructure. Whether these optical systems are crisscrossing the world or linking the islands of an archipelago, we can extend their lifespans.”
………………………………………………………………………………………………………………………….
According to TeleGeography, there were an estimated 1.4 million km of submarine cables in service globally at the start of 2023 and that number is rapidly increasing.
Recent highlights include Orange and ASN agreeing in July to construct the new Medusa cable system between multiple locations in North Africa and Southern Europe. In late September, Telecom Egypt agreed to extend Medusa all the way to the Red Sea.
On a slightly smaller scale, early last month, Telecom Italia Sparkle began offering commercial services on a stretch of the Blue cable system, linking Palermo with Genoa to Milan. It is part of the larger Blue and Raman system, being built in partnership with Google. Once completed, the Blue part will connect various locations on the Med – including Greece and Israel in addition to Italy – while the Raman part will connect Jordan, Saudi Arabia, Oman and eventually India.
Resources and additional information:
https://telecoms.com/524184/nokia-bell-labs-makes-submarine-cables-go-blinkin-fast/
Analysys Mason: 40 operational 5G SA networks worldwide; Sub-Sahara Africa dominates new launches
According to the latest edition of Analysys Mason’s 5G deployment tracker, 26 new 5G networks have been commercially launched across 22 countries so far in 2023, with an additional 55 5G networks either in deployment or scheduled for launch later this year.
Sub-Saharan Africa (SSA) has dominated 5G launch figures in 2023, with 13 new launches across 10 countries, accounting for over 48% of 5G launches during the period. Emerging Asia–Pacific (EMAP) has recorded 6 new 5G launches in 2023 so far, while Central and Eastern Europe (CEE) recorded 4 new 5G launches, respectively. Additionally, North America (NA) recorded 2 new 5G launches, while Western Europe (WE) and the Middle East and North Africa (MENA) each reported one new 5G launch in the same period. 5G standalone (SA) launches for the last 12 months (August 2022–2023) have continued to grow steadily, with 11 new operators commercially launching 5G SA networks. Five of these launches have occurred in 2023, with 3 operators launching in WE and 2 launching in MENA.
The market research firm’s 5G deployment tracker includes 338 entries from 2018 to 1H 2023, with 274 confirmed launches of 5G networks and 40 commercial launches of 5G SA networks, worldwide.
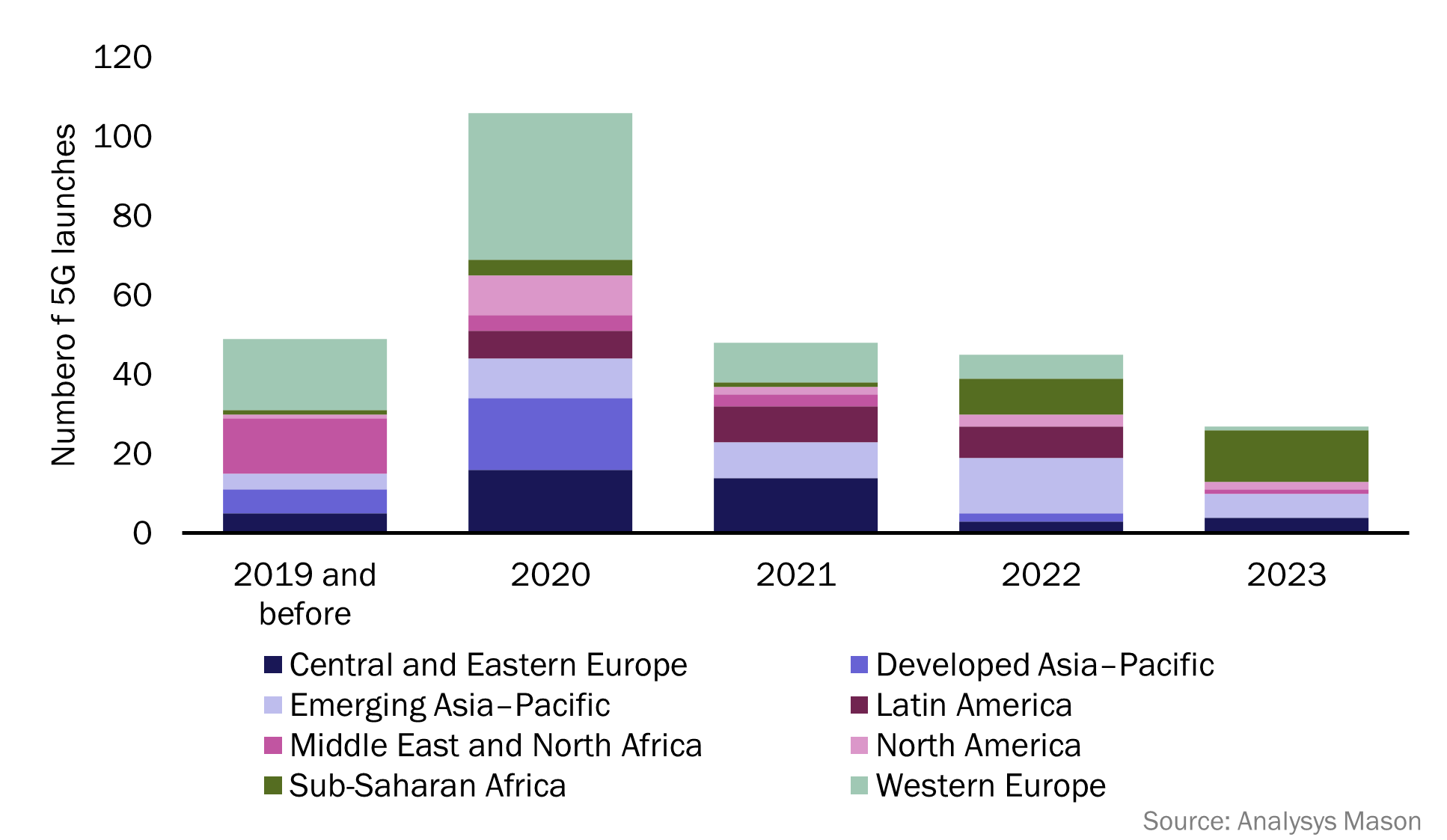
According to the latest edition of Analysys Mason’s 5G deployment tracker, 26 new 5G networks have been commercially launched across 22 countries so far in 2023, with an additional 55 5G networks either in deployment or scheduled for launch later this year.
Sub-Saharan Africa (SSA) has dominated 5G launch figures in 2023, with 13 new launches across 10 countries, accounting for over 48% of 5G launches during the period. Emerging Asia–Pacific (EMAP) has recorded 6 new 5G launches in 2023 so far, while Central and Eastern Europe (CEE) recorded 4 new 5G launches, respectively. Additionally, North America (NA) recorded 2 new 5G launches, while Western Europe (WE) and the Middle East and North Africa (MENA) each reported one new 5G launch in the same period. 5G standalone (SA) launches for the last 12 months (August 2022–2023) have continued to grow steadily, with 11 new operators commercially launching 5G SA networks. Five of these launches have occurred in 2023, with 3 operators launching in WE and 2 launching in MENA.
The 5G deployment tracker includes 338 entries from 2018 to 1H 2023, with 274 confirmed launches of 5G networks and 40 commercial launches of 5G SA networks, worldwide.
Figure 1: 5G network launches, worldwide, 2019 (and before)–2023
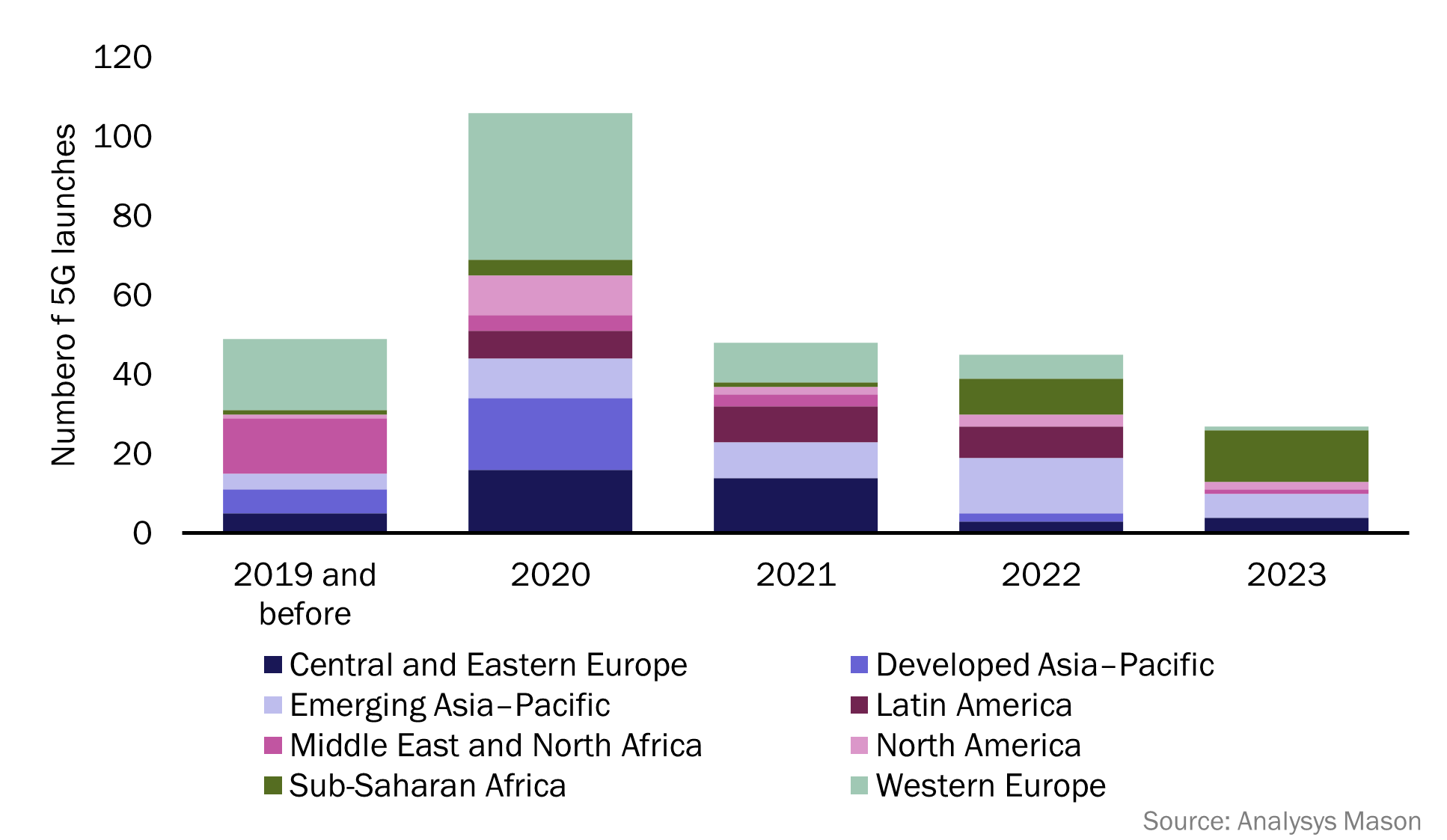
Network operators in SSA have long prioritised investment in 4G networks over 5G. This is due to the lower cost of 4G devices and infrastructure, and the high number of users on legacy networks, such as 2G and 3G, across the region. As a result, operators have prioritised the migration of these users to 4G networks over new 5G deployments. In 2021, 79.8% of all mobile connections in SSA were 2G or 3G connections, and there were only 6 operational 5G networks in the region. This changed in 2022, with operators launching 9 new 5G networks across the region.1 This number has continued to climb so far in 2023, with a total of 13 new 5G network launches since January.
SSA now accounts for over 48% of all 2023 5G launches, with the region now having more operational 5G networks than MENA, NA, Latin America (LATAM) and developed Asia–Pacific (DVAP). Airtel has launched the most 5G networks in SSA so far in 2023, with the group launching 4 new 5G networks in 4 different countries. These include:
- Kenya: Airtel became the second operator to launch a 5G network in Kenya, following Safaricom’s launch in October 2022. Airtel claims coverage across 370 areas including Mombasa, Nakuru, Nairobi and Kakamega.
- Nigeria: Airtel launched its 5G network in June 2023, with coverage in multiple areas including Abuja, Port Harcourt and Lagos. Airtel is the third operator to launch a 5G network in Nigeria, following MTN (2022) and Mafab (January 2023).
- Uganda: Airtel launched its 5G services in various areas of Kampala in August 2023, one month after MTN launched the first 5G network in Uganda.
- Zambia: Airtel became the second operator to launch a 5G network in Zambia in July 2023, following MT’s 5G launch in November 2022.
Other notable launches across SSA include:
- French Guiana: Orange Caraibe and SFR Caraibe both launched their 5G networks in 2023 in the 3.5GHz band. These are the first 5G networks in French Guiana.
- The Gambia: QCell became the first operator to launch 5G in The Gambia in June 2023, launching in selected areas of the capital city, Banjul.
- South Africa: Telkom South Africa launched their 5G network in 2023, becoming the fourth operator to launch 5G in South Africa after Rain, MTN and Vodacom.
…………………………………………………………………………………………………………………………………
There are now 40 operational 5G SA networks worldwide, spanning 24 countries and 34 different operators. In the previous 12 months (from September 2022 to September 2023) there have been 11 new 5G SA launches, with 5 of these occurring in 2023. These 5 launches were spread across WE (3 new launches) and MENA (2 new launches). More 5G SA launches are expected in 2023, as launch figures have historically peaked in the second half of a calendar year. 5G SA launch figures are expected to accelerate over the next few years, and operators that have already launched 5G SA networks are likely to continue to expand their standalone coverage.
Analysys Mason predicts that by 2024, 5G SA will be the main source of revenue for vendors.
…………………………………………………………………………………………………………………………….
Editor’s Note: We strongly disagree with that 5G SA forecast and we don’t know if the “vendors,” like Ericsson, Nokia, Huawai, ZTE, Samsung, NEC, also provide 5G RAN equipment. Other 5G SA core network vendors, don’t make RAN equipment, e.g. Amazon AWS, Microsoft Azure, Cisco, VMware, Parallel Wireless and Mavenir
In the U.S., only T-Mobile and Dish Network have deployed 5G SA core networks. AT&T and Verizon have been talking the talk about 5G SA core networks but have no commercial deployments. UScellular 5G SA is in test mode. UScellular’s CTO Mike Irizarry said it’s now testing Nokia’s 5G SA core, but doesn’t plan to rush headlong into the SA 5G future.
Also, because there are no specification for 5G SA core network interoperability or roaming, 5G SA endpoint mobility will be extremely limited.
…………………………………………………………………………………………………………………………….
With three new launches so far in 2023, WE is beginning to compete with DVAP for the total number of 5G SA network launches. DVAP has led the total 5G standalone network launch figures since 2021 (see Figure 2), with 11 new launches in the last 2 years across Australia, Japan, Singapore and South Korea. Western Europe now accounts for 25% of all 5G SA networks worldwide, 5 percentage points less than DVAP which accounts for 30%. All regions have now launched at least one 5G SA network, excluding CEE (see Figure 2).
Figure 2: 5G SA launches, worldwide, 2019–2023
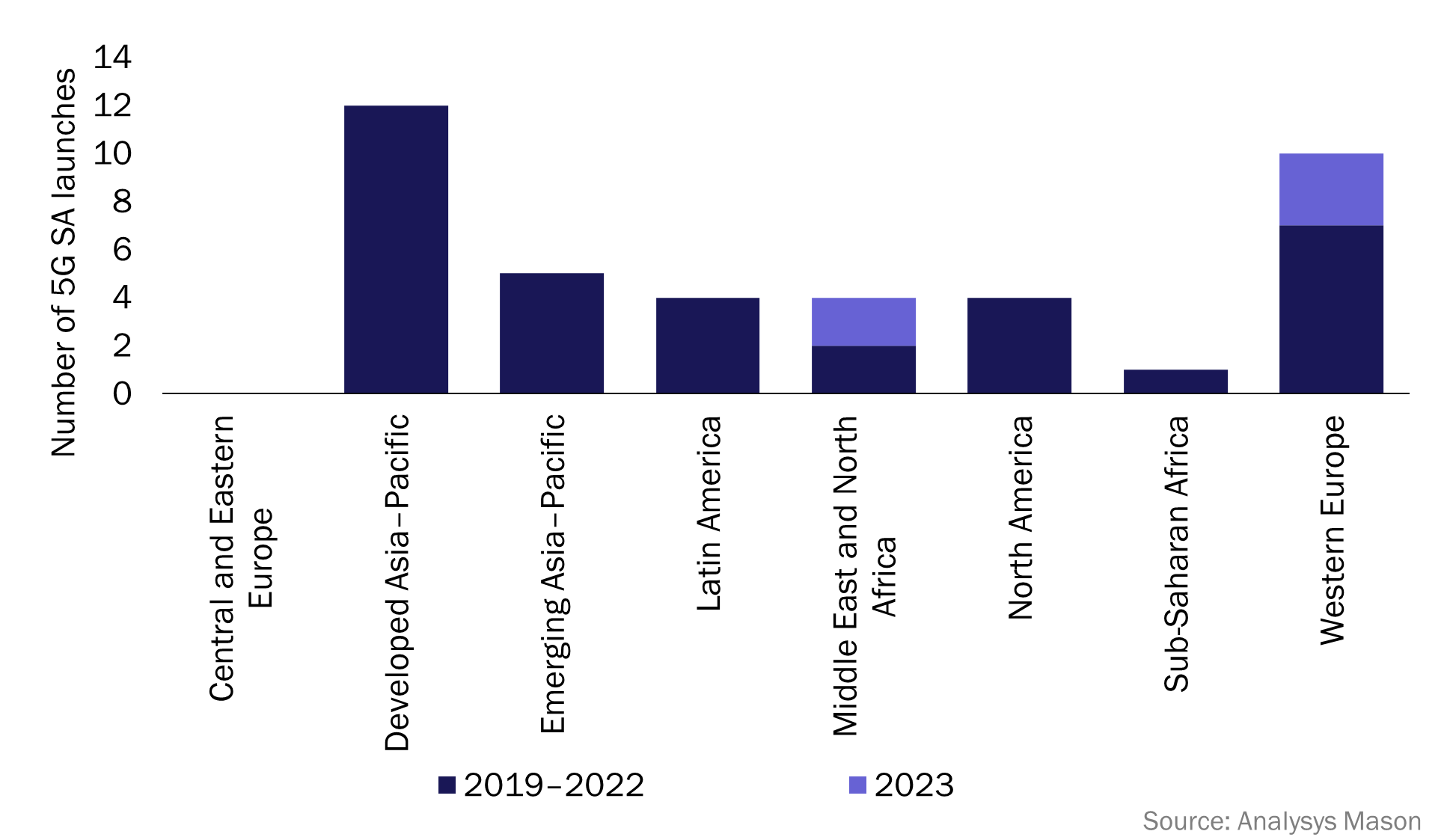
In 2023, notable deployments of standalone networks have included:
- Saudi Arabia: Zain launched the first 5G SA network in Saudi Arabia in March 2023, making Saudi Arabia the third country in MENA to have an operational 5G SA network, after Bahrain and Kuwait.
- Spain: Orange and Telefónica both launched 5G SA networks in 2023. These are the first two 5G SA networks in Spain.
- United Arab Emirates (UAE): E& (formerly Etisalat) launched its 5G SA network in February 2023, becoming the fourth operator to launch 5G SA services within MENA and the first in the UAE.
- United Kingdom: Vodafone launched the first 5G SA network in the UK, in June 2023, with coverage across Cardiff, Glasgow, London and Manchester. Vodafone has branded its 5G SA as ‘5G Ultra’.
References:
https://www.analysysmason.com/research/content/articles/5g-deployment-launches-rma18/
GSA 5G SA Core Network Update Report
ABI Research: Expansion of 5G SA Core Networks key to 5G subscription growth
Counterpoint Research: Ericsson and Nokia lead in 5G SA Core Network Deployments
Tech Mahindra and Microsoft partner to bring cloud-native 5G SA core network to global telcos
Omdia and Ericsson on telco transitioning to cloud native network functions (CNFs) and 5G SA core networks
Dell’Oro: RAN market declines at very fast pace while Mobile Core Network returns to growth in Q2-2023
Dell’Oro: RAN Market to Decline 1% CAGR; Mobile Core Network growth reduced to 1% CAGR
Dell’Oro: Mobile Core Network & MEC revenues to be > $50 billion by 2027
Dell’Oro: Market Forecasts Decreased for Mobile Core Network and Private Wireless RANs
Dell’Oro: Mobile Core Network market driven by 5G SA networks in China
Counterpoint Research – 5G SA Core Deployments Decelerate in H1 2023