Big tech firms target data infrastructure software companies to increase AI competitiveness

- Meta announced Friday a $14.3 billion deal for a 49% stake in data-labeling company Scale AI. It’s 28 year old co-founder and CEO will join Meta as an AI advisor.
- Salesforce announced plans last month to buy data integration company Informatica for $8 billion. It will enable Salesforce to better analyze and assimilate scattered data from across its internal and external systems before feeding it into its in-house AI system, Einstein AI, executives said at the time.
- IT management provider ServiceNow said in May it was buying data catalogue platform Data.world, which will allow ServiceNow to better understand the business context behind data, executives said when it was announced.
- IBM announced it was acquiring data management provider DataStax in February to manage and process unstructured data before feeding it to its AI platform.
Hutchison Telecom is deploying 5G-Advanced in Hong Kong without 5G-A endpoints
Hutchison Telecom-Hong Kong is deploying 3GPP’s 5G-Advanced (5G-A) in high-traffic venues in Hong Kong, including the HK Exhibition Center, the West Kowloon Cultural District and the new $3.9 billion Kai Tak Sports Park. However, 5G-A end points [1.] (like smartphones and tablets) aren’t likely to arrive until next year, according to Hutchinson Executive Director and CEO Kenny Koo. Therefore, the 5G-A Hong Kong deployment is mostly symbolic. However, Hutchison is doing some commercial business with 5G-A hotspots.
Hutchinson used the 5G-A modems to provide coverage for the annual Art Basel visual arts fair in March, enabling organizers to offer free Wi-Fi for visitors. It’s also found a little niche in pop-up stores. 5G-A modems registered download and upload speeds of 3.1 Gbit/s and 370 Mbit/s respectively in a demo earlier this month.
Note 1. Only a handful of 5G-A endpoint devices are available in mainland China, where operators are reporting 5G-A commercial networks in hundreds of cities – in the 3.5GHz, 4.9GHz and 2.1GHz bands.
“2025 marks the 5th anniversary of 5G launch. In December 2024, our 5G customer penetration rate reached 54%. At this important stage, we are comprehensively enhancing our 5G coverage and capacity while continuously optimizing user experience. Limited-time upgrade offers are also tailored to encourage customers to upgrade to 5G. Together, we are advancing into the new era of 5.5G (aka 5GA). In support of the development of the Northern Metropolis, we have taken the initiative to actively enhance 5G network coverage in the district as the flow of people and vehicles surges. This ensures that commuters travelling between the northwest New Territories and Kowloon can enjoy a smoother network experience at major transportation hubs, including Tai Lam Tunnel and the Kam Sheung Road section of the MTR Tuen Ma Line. In addition, we are helping to boost the mega event economy by activating 5.5G network hotspots at major event venues in Hong Kong including Kai Tak Sports Park, the West Kowloon Cultural District and the Hong Kong Convention and Exhibition Centre. Customers enjoy an improved experience at high-traffic hotspots compared with the original 5G coverage, with enhanced network speed, increased capacity and low latency performance provided by 5G broadband.”
“We try to position ourselves as a market leader in the technology evolution,” Koo told Light Reading. He said the 5G-A ecosystem “was not yet ready” because of the lack of devices that can support the 26 GHz and 28 GHz bands. “iPhone, Samsung and Huawei handsets do not support 5.5G in those bands,” he said, using the company’s preferred branding of 5G-Advanced.
Author’s Note: Koo did not mention that 5G-A has yet to be standardized by ITU-R as part of IMT 2020 RIT/SRIT aka the ITU-R M.2150 recommendation. 5G Advanced is included in 3GPP Release 18 and is expected to be part of M.2150 issue 3, now being developed by ITU-R WP 5D.
Hutchinson’s subscriber base grew 17% to 4.6 million, mostly due to prepaid gains, while 5G penetration increased 8 percentage points to 54%. Koo said the company has been able to sustain the growth this year because of demand from inbound travelers from mainland China. “They like our prepaid cards,” he added. Last year, Hutchinson’s roaming revenue increased 30% to 684 million Hong Kong dollars (US$87 million) and now accounts for nearly a fifth of total service revenue.
eSim is also a growing market for Hutchinson. There are a lot of travel SIM portals selling eSIM solutions right to consumers,” Koo said. The popularity of its eSIM product means Hutchison’s addressable market has expanded way beyond Hong Kong to reach mobile customers worldwide.
About Hutchison Telecommunications Hong Kong:
Hutchison Telecommunications Hong Kong Limited (“HTHK”) has launched 5G broadband services in both the consumer and enterprise markets, providing high-speed indoor and outdoor internet access. Leveraging a robust 5G network, HTHK has also extended the deployment of 5G solutions including 5G 4K live broadcasting, virtual reality and real-time data transmission to various verticals. HTHK plays a prominent role in developing a new economy ecosystem, channeling the latest technologies into innovations that set market trends and steer industry development.
……………………………………………………………………………………………………………………………………………………………
References:
https://www.lightreading.com/5g/hutchison-joins-5g-advanced-race
https://doc.irasia.com/listco/hk/hthkh/press/p250529.pdf
5G Advanced offers opportunities for new revenue streams; 3GPP specs for 5G FWA?
What is 5G Advanced and is it ready for deployment any time soon?
Huawei pushes 5.5G (aka 5G Advanced) but there are no completed 3GPP specs or ITU-R standards!
Nokia exec talks up “5G Advanced” (3GPP release 18) before 5G standards/specs have been completed
ITU-R recommendation IMT-2020-SAT.SPECS from ITU-R WP 5B to be based on 3GPP 5G NR-NTN and IoT-NTN (from Release 17 & 18)
Nile launches a Generative AI engine (NXI) to proactively detect and resolve enterprise network issues
Nile is a Nile is a private, venture-funded technology company specializing in AI-driven network and security infrastructure services for enterprises and government organizations. Nile has pioneered the use of AI and machine learning in enterprise networking. Its latest generative AI capability, Nile Experience Intelligence (NXI), proactively resolves network issues before they impact users or IT teams, automating fault detection, root cause analysis, and remediation at scale. This approach reduces manual intervention, eliminates alert fatigue, and ensures high performance and uptime by autonomously managing networks.
Significant Innovations Include:
-
Automated site surveys and network design using AI and machine learning
-
Digital twins for simulating and optimizing network operations
-
Edge-to-cloud zero-trust security built into all service components
-
Closed-loop automation for continuous optimization without human intervention
Today, the company announced the launch of Nile Experience Intelligence (NXI), a novel generative AI capability designed to proactively resolve network issues before they impact IT teams, users, IoT devices, or the performance standards defined by Nile’s Network-as-a-Service (NaaS) guarantee. As a core component of the Nile Access Service [1.], NXI uniquely enables Nile to take advantage of its comprehensive, built-in AI automation capabilities. NXI allows Nile to autonomously monitor every customer deployment at scale, identifying performance anomalies and network degradations that impact reliability and user experience. While others market their offerings as NaaS, only the Nile Access Service with NXI delivers a financially backed performance guarantee—an unmatched industry standard.
………………………………………………………………………………………………………………………………………………………………
Note 1. Nile Access Service is a campus Network-as-a-Service (NaaS) platform that delivers both wired and wireless LAN connectivity with integrated Zero Trust Networking (ZTN), automated lifecycle management, and a unique industry-first performance guarantee. The service is built on a vertically integrated stack of hardware, software, and cloud-based management, leveraging continuous monitoring, analytics, and AI-powered automation to simplify deployment, automate maintenance, and optimize network performance.
………………………………………………………………………………………………………………………………………………………………………………………………….
“Traditional networking and NaaS offerings based on service packs rely on IT organizations to write rules that are static and reactive, which requires continuous management. Nile and NXI flipped that approach by using generative AI to anticipate and resolve issues across our entire install base, before users or IT teams are even aware of them,” said Suresh Katukam, Chief Product Officer at Nile. “With NXI, instead of providing recommendations and asking customers to write rules that involve manual interaction—we’re enabling autonomous operations that provide a superior and uninterrupted user experience.”
Key capabilities include:
- Proactive Fault Detection and Root Cause Analysis: predictive modeling-based data analysis of billions of daily events, enabling proactive insights across Nile’s entire customer install base.
- Large Scale Automated Remediation: leveraging the power of generative AI and large language models (LLMs), NXI automatically validates and implements resolutions without manual intervention, virtually eliminating customer-generated trouble tickets.
- Eliminate Alert Fatigue: NXI eliminates alert overload by shifting focus from notifications to autonomous, actionable resolution, ensuring performance and uptime without IT intervention.
Unlike rules-based systems dependent on human-configured logic and manual maintenance, NXI is:
- Generative AI and self-learning powered, eliminating the need for static, manually created rules that are prone to human error and require ongoing maintenance.
- Designed for scale, NXI already processes terabytes of data daily and effortlessly scales to manage thousands of networks simultaneously.
- Built on Nile’s standardized architecture, enabling consistent AI-driven optimization across all customer networks at scale.
- Closed-loop automated, no dashboards or recommended actions for customers to interpret, and no waiting on manual intervention.
Katukam added, “NXI is a game-changer for Nile. It enables us to stay ahead of user experience and continuously fine-tune the network to meet evolving needs. This is what true autonomous networking looks like—proactive, intelligent, and performance-guaranteed.”
From improved connectivity to consistent performance, Nile customers are already seeing the impact of NXI. For more information about NXI and Nile’s secure Network as a Service platform, visit www.nilesecure.com.
About Nile:
Nile is leading a fundamental shift in the networking industry, challenging decades-old conventions to deliver a radically new approach. By eliminating complexity and rethinking how networks are built, consumed, and operated, Nile is pioneering a new category designed for a modern, service-driven era. With a relentless focus on simplicity, security, reliability, and performance, Nile empowers organizations to move beyond the limitations of legacy infrastructure and embrace a future where networking is effortless, predictable, and fully aligned with their digital ambitions.
Nile is recognized as a disruptor in the enterprise networking market, offering a modern alternative to traditional vendors like Cisco and HPE. Its model enables organizations to reduce total cost of ownership by more than 60% and reclaim IT resources while providing superior connectivity. Major customers include Stanford University, Pitney Bowes, and Carta.
The company has received several industry accolades, including the CRN Tech Innovators Award (2024) and recognition in Gartner’s Peer Insights Voice of the Customer Report1. Nile has raised over $300 million in funding, with a significant $175 million Series C round in 2023 to fuel expansion.
References:
https://nilesecure.com/company/about-us
Does AI change the business case for cloud networking?
Networking chips and modules for AI data centers: Infiniband, Ultra Ethernet, Optical Connections
Qualcomm to acquire Alphawave Semi for $2.4 billion; says its high-speed wired tech will accelerate AI data center expansion
AI infrastructure investments drive demand for Ciena’s products including 800G coherent optics
NGMN: 6G Key Messages from a network operator point of view
As 3GPP prepares for its Release 20 [1.], the Next Generation Mobile Networks Alliance (NGMN) has issued a 6G Key Messages statement saying that 6G can’t be just “another generational shift” and that lessons must be learned from “the mistakes of 5G.” NGMN says that 6G must demonstrate clear, tangible benefits within a realistic techno-economic framework. Network Architecture needs to meet MNOs criteria for modularity, simplicity, openness, operational simplification, compatibility and interoperability, and trustworthiness while delivering economic and social sustainability. These factors are crucial to enable fast deployment and to support the development of market-aligned services that meet user demands.
“6G standards must be globally harmonized. It is expected to be built upon the features and capabilities introduced with 5G, alongside new capabilities to deliver new services and value. Such technological evolutions should be assessed with respect to their benefits versus their associated impact. 6G standards must learn from the mistakes of 5G, including multiple architecture options, features that are never used and use cases that have no market pull.”
NGMN insists that the introduction of 6G should not cost network operators more than necessary:
“The introduction of 6G should not necessitate a forced hardware refresh. While new radio equipment is required for deployment in new frequency bands, the evolution toward 6G in existing bands should primarily occur through software upgrades, ensuring a smooth transition.”
Note 1. According to 3GPP’s current planning, Release 20 will include a study phase, gathering technical input on potential 6G features, use cases, and architectural shifts. These discussions are intended to inform later specification work, likely in Release 21, aligned with the IMT-2030 submission process. See Editor’s Note below for relationship between 3GPP’s 6G work and ITU-R IMT 2030.
THE NGMN 6G KEY MESSAGES PUBLICATION HAS BEEN ENDORSED BY THE NGMN BOARD OF DIRECTORS IN JUNE 2025:
Laurent Leboucher, Chairman of the NGMN Alliance Board and Orange Group CTO and EVP Networks, explained “6G should be viewed as a seamless evolution — fully compatible with 5G and propelled by continuous software innovation. The industry must move beyond synchronised hardware/software ‘G’ cycles and embrace decoupled roadmaps: one for hardware infrastructure, guided by value-driven and sustainable investments, and another — faster and demand-led — for software-defined business capabilities addressing real needs from society.”
“Along with presenting this consolidated view to 3GPP, this publication serves as a foundation for engaging with the broader industry, driving collaboration, innovation, and strategic direction in the evolving 6G landscape,” said Anita Döhler, CEO of NGMN . “A core tenet of our message is that 6G is not treated as another generational shift for mobile technology – it must be evolutionary.”
“Network evolution is essential for addressing ever-changing societal needs. To achieve this, we need to work collectively as an industry to ensure all future networks are secure, environmentally sound, and economically sustainable,” said Luke Ibbetson, Head of Group R&D at Vodafone and NGMN Board Director.
Key Categories:
• Enhanced Human Communications includes use cases of enriched communications, such as immersive experience, telepresence and multimodal interaction. Voice services must evolve in a business sustainable manner.
• Enhanced Machine Communications reflects the growth of collaborative robotics, requiring reliable communication among robots, their environment and humans.
• Enabling Services gather use cases that require additional features such as high accuracy location, mapping, or sensing.
• Network Evolution describes aspects related to the evolution of core technologies including AI as a service, energy efficiency, and delivering ubiquitous coverage.
Requirements and Design Considerations:
• Sustainability: Minimising environmental impact, securing economic viability, and ensuring social sustainability is the key goal of 6G design.
• Trustworthiness: Ensure that security and privacy are intrinsically embedded in the 6G system to protect against threats and provide solutions that measurably demonstrate this attribute.
• Innovation: A new radio interface should demonstrate significant benefits over and above IMT-2020, as mentioned in the Radio Performance Assessment Framework publication, while considering the practical issues related to deployments in a realistic techno-economical context. It is also critical for innovation that the entirety of the upper 6 GHz band would be available to mobile networks.
Radio Performance Assessment Framework (RPAF) includes guidance for new 6G Radio Access Technologies (RAT). It emphasises that any proposed solutions must be assessed against a reasonable baseline to demonstrate meaningful performance gains.
Editor’s Note: ITU-R WP5D is the official standards body for 6G, which is known as IMT 2030. Like for 5G (IMT 2020), WP 5D sets the requirements while 3GPP develops the Radio Interface Technology (RIT and SRIT) specs which are then contributed to WP 5D by ATIS.
About the MGMN Alliance:
Next Generation Mobile Networks Alliance – is a global, operator-driven leadership network established in 2006 by leading international mobile network operators (MNOs). Its mission is to ensure that next-generation mobile network infrastructure, service platforms and devices meet operators’ requirements while addressing the demands and expectations of end users.
NGMN’s vision is to provide impactful industry guidance to enable innovative, sustainable and affordable mobile telecommunication services. Key focus areas include Mastering the Route to Disaggregation, Green Future Networks and 6G, while continuing to support the full implementation of 5G.
As a global alliance of nearly 70 companies and organisations—including operators, vendors, and academia—NGMN actively incorporates the perspectives of all stakeholders. It drives global alignment and convergence of technology standards and industry initiatives to avoid fragmentation and support industry scalability.
References:
https://www.ngmn.org/wp-content/uploads/2506_NGMN_6G-Key-Messages_An-Operator-View_V1.0.pdf
NGMN calls for harmonised 6G standards to drive seamless mobile evolution on behalf of global MNOs
NGMN issues ITU-R framework for IMT-2030 vs ITU-R WP5D Timeline for RIT/SRIT Standardization
ITU-R WP 5D reports on: IMT-2030 (“6G”) Minimum Technology Performance Requirements; Evaluation Criteria & Methodology
ITU-R: IMT-2030 (6G) Backgrounder and Envisioned Capabilities
ITU-R WP5D invites IMT-2030 RIT/SRIT contributions
Highlights of 3GPP Stage 1 Workshop on IMT 2030 (6G) Use Cases
https://unidir.org/wp-content/uploads/2024/12/241211_ITU-R-Update-on-WRC-and-IMT-2030.pdf
https://www.itu.int/dms_pubrec/itu-r/rec/m/R-REC-M.2160-0-202311-I%21%21PDF-E.pdf
Draft new ITU-R recommendation (not yet approved): M.[IMT.FRAMEWORK FOR 2030 AND BEYOND]
IBM to Build World’s First Large-Scale, Fault-Tolerant Quantum Computer – Starling
IBM is building the world’s first large-scale quantum computer capable of operating without errors. The computer, called Starling, is set to launch by 2029. The quantum computer will reside in IBM’s new quantum data center in Poughkeepsie, New York and is expected to perform 20,000 more operations than today’s quantum computers, the company said in its announcement Tuesday.
Starling will be “fault tolerant,” meaning it would be able to perform quantum operations for things like drug discovery, supply chain optimization, semiconductor design, and financial risk analyses without the errors that plague quantum computers today and make them less useful than traditional computers.
To represent the computational state of an IBM Starling would require the memory of more than a quindecillion (1048) of the world’s most powerful supercomputers. With Starling, users will be able to fully explore the complexity of its quantum states, which are beyond the limited properties able to be accessed by current quantum computers.
IBM, which already operates a large, global fleet of quantum computers, is releasing a new Quantum Roadmap that outlines its plans to build out a practical, fault-tolerant quantum computer.
“IBM is charting the next frontier in quantum computing,” said Arvind Krishna, Chairman and CEO, IBM. “Our expertise across mathematics, physics, and engineering is paving the way for a large-scale, fault-tolerant quantum computer — one that will solve real-world challenges and unlock immense possibilities for business.”
A large-scale, fault-tolerant quantum computer with hundreds or thousands of logical qubits could run hundreds of millions to billions of operations, which could accelerate time and cost efficiencies in fields such as drug development, materials discovery, chemistry, and optimization.

Starling will be able to access the computational power required for these problems by running 100 million quantum operations using 200 logical qubits. It will be the foundation for IBM Quantum Blue Jay, which will be capable of executing 1 billion quantum operations over 2,000 logical qubits.
A logical qubit is a unit of an error-corrected quantum computer tasked with storing one qubit’s worth of quantum information. It is made from multiple physical qubits working together to store this information and monitor each other for errors.
Like classical computers, quantum computers need to be error corrected to run large workloads without faults. To do so, clusters of physical qubits are used to create a smaller number of logical qubits with lower error rates than the underlying physical qubits. Logical qubit error rates are suppressed exponentially with the size of the cluster, enabling them to run greater numbers of operations.
Creating increasing numbers of logical qubits capable of executing quantum circuits, with as few physical qubits as possible, is critical to quantum computing at scale. Until today, a clear path to building such a fault-tolerant system without unrealistic engineering overhead has not been published.
The Path to Large-Scale Fault Tolerance:
The success of executing an efficient fault-tolerant architecture is dependent on the choice of its error-correcting code, and how the system is designed and built to enable this code to scale.
Alternative and previous gold-standard, error-correcting codes present fundamental engineering challenges. To scale, they would require an unfeasible number of physical qubits to create enough logical qubits to perform complex operations – necessitating impractical amounts of infrastructure and control electronics. This renders them unlikely to be able to be implemented beyond small-scale experiments and devices.
A practical, large-scale, fault-tolerant quantum computer requires an architecture that is:
- Fault-tolerant to suppress enough errors for useful algorithms to succeed.
- Able to prepare and measure logical qubits through computation.
- Capable of applying universal instructions to these logical qubits.
- Able to decode measurements from logical qubits in real-time and can alter subsequent instructions.
- Modular to scale to hundreds or thousands of logical qubits to run more complex algorithms.
- Efficient enough to execute meaningful algorithms with realistic physical resources, such as energy and infrastructure.
Today, IBM is introducing two new technical papers that detail how it will solve the above criteria to build a large-scale, fault-tolerant architecture.
The first paper unveils how such a system will process instructions and run operations effectively with qLDPC codes. This work builds on a groundbreaking approach to error correction featured on the cover of Nature that introduced quantum low-density parity check (qLDPC) codes. This code drastically reduces the number of physical qubits needed for error correction and cuts required overhead by approximately 90 percent, compared to other leading codes. Additionally, it lays out the resources required to reliably run large-scale quantum programs to prove the efficiency of such an architecture over others.
The second paper describes how to efficiently decode the information from the physical qubits and charts a path to identify and correct errors in real-time with conventional computing resources.
From Roadmap to Reality:
The new IBM Quantum Roadmap outlines the key technology milestones that will demonstrate and execute the criteria for fault tolerance. Each new processor in the roadmap addresses specific challenges to build quantum computers that are modular, scalable, and error-corrected:
- IBM Quantum Loon, expected in 2025, is designed to test architecture components for the qLDPC code, including “C-couplers” that connect qubits over longer distances within the same chip.
- IBM Quantum Kookaburra, expected in 2026, will be IBM’s first modular processor designed to store and process encoded information. It will combine quantum memory with logic operations — the basic building block for scaling fault-tolerant systems beyond a single chip.
- IBM Quantum Cockatoo, expected in 2027, will entangle two Kookaburra modules using “L-couplers.” This architecture will link quantum chips together like nodes in a larger system, avoiding the need to build impractically large chips.
Media Contacts
Erin Angelini, IBM Communications
[email protected]
Brittany Forgione, IBM Communications
[email protected]
References:
IBM’s path to scaling fault tolerance, read their blog here, and watch BM Quantum scientists in this latest video
Bloomberg on Quantum Computing: appeal, who’s building them, how does it work?
Google’s new quantum computer chip Willow infinitely outpaces the world’s fastest supercomputers
Ultra-secure quantum messages sent a record distance over a fiber optic network
Quantum Computers and Qubits: IDTechEx report; Alice & Bob whitepaper & roadmap
China Mobile verifies optimized 5G algorithm based on universal quantum computer
Qualcomm to acquire Alphawave Semi for $2.4 billion; says its high-speed wired tech will accelerate AI data center expansion
Qualcomm Inc. has agreed to buy London-listed semiconductor company Alphawave IP Group Plc (“Alphawave Semi”) for about $2.4 billion in cash to expand its technology for artificial intelligence (AI) in data centers. The deal is expected to close in the first quarter of 2026, subject to regulatory and shareholder approval.
Alphawave Semi is claimed to be a global leader in high-speed wired connectivity and compute technologies delivering IP, custom silicon, connectivity products and chiplets. It’s products ‘form a part of the core infrastructure enabling next generation services in a wide array of high growth applications’ such as data centers, AI, data networking and data storage, according to the press release.
Regarding connectivity, Alphawave Semi develops industry leading PAM4 and Coherent DSP products in the most advanced technologies for all forms of data center connectivity.
Alphawave (which held an initial public offering in 2021 at 410 pence per share) has consistently traded below that level. The company had struggled with a reliance on large customers and navigating geopolitical tensions between the US and China, where Alphawave decided to cut back its business last year.
Still, the company’s technology has been gaining traction and had reported a surge in orders in the fourth quarter. Chief Executive Officer Tony Pialis said in a statement at the time that orders from North American AI customers were driving the business.
Qualcomm Chief Executive Officer Cristiano Amon is looking to reduce the company’s reliance on the smartphone market, where growth has slowed, and push into new areas. Alphawave makes high-speed semiconductor and connectivity technology that can be used for data centers and AI applications, two growth areas in the chip industry that are being driven by demand for products like OpenAI’s ChatGPT.

Image credit: Qualcomm / Alphawave Semi
“Qualcomm’s acquisition of Alphawave Semi represents a significant milestone for us and an opportunity for our business to join forces with a respected industry leader and drive value to our customers,” said Tony Pialis, president and CEO of Alphawave Semi. “By combining our resources and expertise, we will be well-positioned to expand our product offerings, reach a broader customer base, and enhance our technological capabilities. Together, we will unlock new opportunities for growth, drive innovation, and create a leading player in AI compute and connectivity solutions.”
“Under Tony’s leadership Alphawave Semi has developed leadi
ng high-speed wired connectivity and compute technologies that are complementary to our power-efficient CPU and NPU cores,” said Mr. Amon. “Qualcomm’s advanced custom processors are a natural fit for data center workloads. The combined teams share the goal of building advanced technology solutions and enabling next-level connected computing performance across a wide array of high growth areas, including data center infrastructure.”
References:
https://www.qualcomm.com/news/releases/2025/06/qualcomm-to-acquire-alphawave-semi
https://www.telecoms.com/enterprise-telecoms/qualcomm-to-purchase-alphawave-semi
MediaTek overtakes Qualcomm in 5G smartphone chip market
AI infrastructure investments drive demand for Ciena’s products including 800G coherent optics
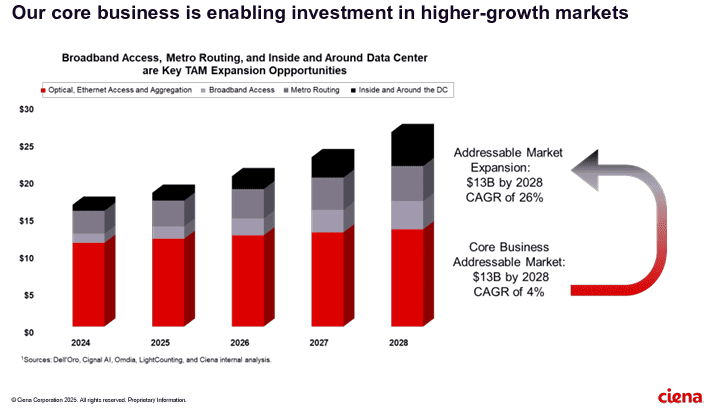
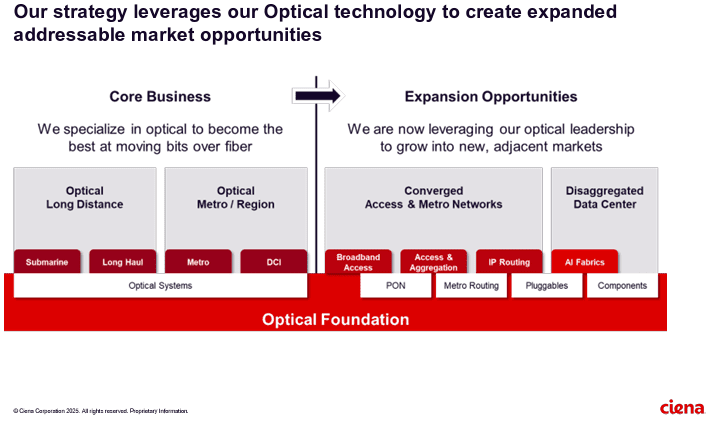
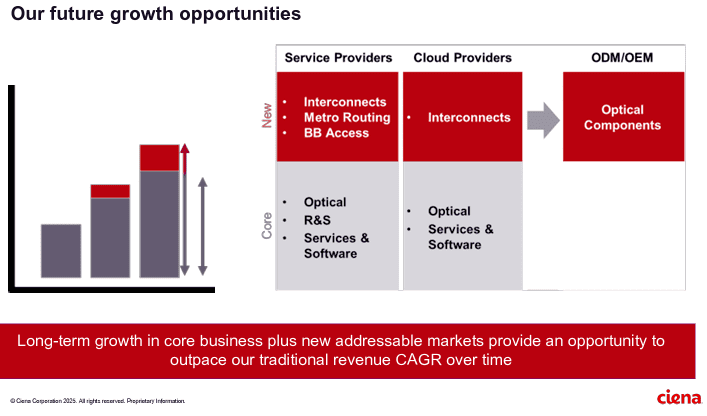
Artificial Intelligence (AI) infrastructure investments are starting to shift toward networks needed to support the technology, rather than focusing exclusively on computing and power, according to Ciena Chief Executive Gary Smith. The trends helped Ciena swing to a profit and post a 24% jump in sales in the recent quarter.
The company enables high-speed fiber optic connectivity for telecommunications and data centers, helping hyper-scalers such as Amazon and Microsoft support AI initiatives via data center interconnects and intra-data center networking. Currently, the company is ramping up production to meet surging demand fueled by cloud and AI investments.
“There’s no point in investing in these massive amounts of GPUs if we’re going to strand it because we didn’t invest in the network,” Smith said Thursday.
……………………………………………………………………………………………………………………………………………………..
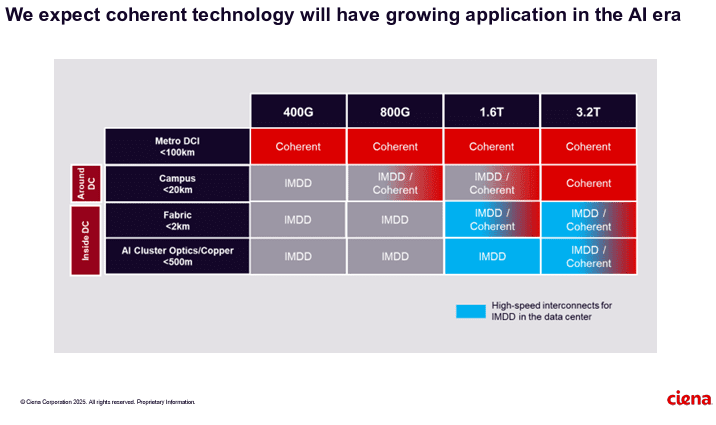
Ciena sees a bright future in 800G coherent optics that can accommodate AI traffic. Smith said a global cloud provider has selected Ciena’s coherent 800-gig pluggable modules and Reconfigurable Line System (RLS) photonics for investing in geographically distributed, regional GPU clusters. “With our coherent optical technology ideally suited for this type of connectivity, we expect to see more of these opportunities emerge as cloud providers evolve their data center network architectures to support their AI strategies,” he added.
It’s still early innings for 800G adoption, but demand is climbing due to AI and cloud connectivity. Vertical Systems Group expects to see “a measurable increase” in 800G installations this year. Dell’Oro optical networking analyst Jimmy Yu noted on LinkedIn Ciena’s data center interconnect win is the first he’s heard of that involves connecting GPU clusters across 100+ kilometer spans. “It was a hot topic of discussion for nearly 2 years. It is now going to start,” Yu said.
……………………………………………………………………………………………………………………………………………………
Ciena’s future growth opportunities include network service and cloud service providers as well as ODM/OEM sales of optical components.
References:
https://www.wsj.com/business/earnings/ciena-swings-to-profit-as-ai-investments-drive-demand-0195f30c
https://investor.ciena.com/static-files/d964ccac-74b3-43d9-a73e-ecf67fab6060
https://www.fierce-network.com/broadband/ciena-now-expects-tariff-costs-10m-quarter
HPE cost reduction campaign with more layoffs; 250 AI PoC trials or deployments
Hewlett Packward Enterprise (HPE) is going through yet another restructuring to reduce costs and to capitalize on the AI use cases it’s been developing. HPE’s workforce reduction program announced in March 2025 was to reduce its headcount of around 61,000 by 2,500 and to have another reduction of 500 people by attrition, over a period of 12 to 18 months, eliminating about $350 million in annual costs when it is said and done. The plan is to have this restructuring done by the end of this fiscal year, which comes to a close at the end of October. The headcount at the end of Q2 Fiscal Year 2025 was 59,000, so the restructuring is proceeding apace and this is, by the way, the lowest employee count that HPE’s enterprise business has had since absorbing Compaq in the wake of the Dot Com Bust in 2001.
The company, which sells IT servers, network communications equipment and cloud services, employed about 66,000 people in 2017, not long after it was created by the bi-section of Hewlett-Packard (with the PC- and printer-making part now called HP Inc). By the end of April this year, the number of employees had dropped to 59,000 – “the lowest we have seen as an independent company,” said HPE chief financial officer of Marie Myers, on the company’s Wednesday earnings call (according to this Motley Fool transcript)– after 2,000 job cuts in the last six months. By the end of October, under the latest plans, HPE expects to have shed another 1,050 employees.
Weak profitability of its server and cloud units is why HPE now attaches such importance to intelligent edge. HPE’s networking division today encompasses the Aruba enterprise Wi-Fi business along with more recent acquisitions such as Athonet, an Italian developer of core network software for private 5G. It accounts for only 15% of sales but a huge 41% of earnings, which makes it HPE’s most profitable division by far, with a margin of 24%.
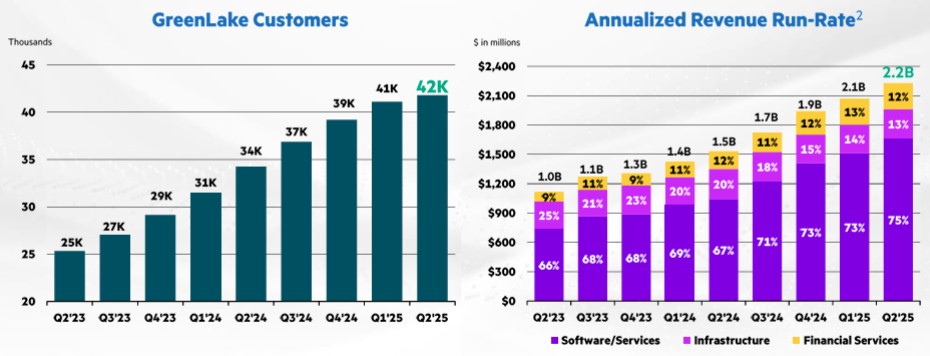
Customer growth is slowing at HPE’s GreenLake cloud services division. Only 1,000 customers added in the quarter, bringing to total to 42,000 worldwide. The annualized run rate for the GreenLake business inched up to $2.2 billion, compared to $2.1 billion in Q1 F2025 and from $1.5 billion a year ago. It is in this area that HPE plans to accelerate it’s AI growth, via Nvidia’s AI/GPU chips.
Source: HPE
With respect to the Juniper Networks acquisition, there is a possibility that the $14 billion deal may collapse. A legal battle in court is due to begin on July 9th, but Neri talked on the analyst call about exploring “a number of other options if the Juniper deal doesn’t happen.”

Photo Credit: HPE
Apparently, artificial intelligence (AI) is allowing HPE to eject staff it once needed. It has apparently worked with Deloitte, a management consultancy, to create AI “agents” based on Nvidia’s technology and its own cloud. Let loose in finance, those agents already seem to be taking over some jobs. “This strategic move will transform our executive reporting,” said Myers. “We’re turning data into actionable intelligence, accelerating our reporting cycles by approximately 50% and reducing processing costs by an estimated 25%. Our ambition is clear: a leaner, faster and more competitive organization. Nothing is off limits.”
HPE CEO Anthony Neris AI comments on yesterday’s earnings call:
Ultimately, it comes down to the mix of the business with AI. And that’s why we take a very disciplined approach across the AI ecosystem, if you will. And what I’m really pleased in AI is that this quarter, one-third of our orders came from enterprise, which tend to come with higher margin because there is more software and services attached to that enterprise market. Then you have to pay attention also to working capital. Working capital is very important because in some of these deals, you are deploying a significant amount of capital and there is a time between the capital deployment and the revenue profit recognition. So that’s why, it is a technology transition, there is a business transition, and then there’s a working capital transition. But I’m pleased with the progress we made in Q2.
The fact is that we have more than 250 use cases where we are doing PoCs (Proof of Concepts) or already deploying AI. In fact, more than 40 are already in production. And we see the benefits of that across finance, global operations, marketing, as well as services. So that’s why we believe there is an opportunity to accelerate that improvement, not just by reducing the workforce, but really becoming nimbler and better at everything we do.
- About Hewlett Packard Enterprise (HPE):
HP Enterprise (HPE) is a large US based business and technology services company. HPE was founded on 1 November 2015 as part of splitting of the Hewlett-Packard company. The company has over 240,000 employees and the headquarters are based in Palo Alto, CA (as of 2016).
HPE operates in 60 countries, centered in the metropolitan areas of Dallas-Fort Worth; Detroit; Des Moines and Clarion, Iowa; Salt Lake City; Indianapolis; Winchester, Kentucky; Tulsa, Oklahoma; Boise, Idaho; and Northern Virginia in the United States. Other major locations are as follows: Argentina, Colombia, Costa Rica, India, Brazil, Mexico, the United Kingdom, Australia, Canada, Egypt, Germany, New Zealand, Hungary, Spain, Slovakia, Israel, South Africa, Italy, Malaysia and the Philippines.
HPE has four major operating divisions: Enterprise Group, which works in servers, storage, networking, consulting and support; Services; Software; and Financial Services. In May 2016, HPE announced it would sell its Enterprise Services division to one of its competitors, Computer Sciences Corporation (CSC).
References:
UK’s CityFibre launches 5.5Gbit/s wholesale broadband service- 3 times faster than BT Openreach
CityFibre, the UK’s largest independent full fiber optic platform, has unveiled a new 5.5Gbit/s wholesale broadband internet service based on 10Gbit/s XGS-PON technology that has already been rolled out across 85% of the company’s network. CityFibre claims its new product is more than three times faster than the highest rate available service from its much larger rival, Openreach (the network access arm of BT). and available at a much lower wholesale cost, CityFibre’s 5.5Gb symmetrical product will enable partners to offer a range of Multi-Gig speed tiers to customers, improving margins whilst providing a valuable customer retention tool for the long term.
Highlights:
- CityFibre’s new 5500/5500Mbps service offers >3x faster downloads, >45x faster uploads than BT Openreach’s fastest full fibre service which is 1800/120Mbps and is delivered over its GPON network.
- CityFibre’s upgraded XGS-PON network provides numerous benefits over GPON technology, including network cost savings, reduced power consumption, improved performance, and enhanced efficiency.
- CityFibre’s launch of its new Multi-Gig products enables the UK to keep pace with countries including France, the Netherlands, New Zealand and the United States of America where consumers are already making the most of affordable Multi-Gig services.

Photo Credit: CityFibre
Greg Mesch, CEO of CityFibre, said: “The UK’s full fibre future is here, thanks to CityFibre’s powerful, 10Gb XGS-PON network. Our ISP partners are already connecting customers with speeds over 2Gb and exceeding expectations when it comes to quality and reliability, but our next generation of full fibre will set a new standard for what’s possible.
“CityFibre started out to challenge the incumbents and bring choice and competition to the UK market. This is another huge step-forward, giving ISPs more power and flexibility than ever before and bringing affordable Multi-Gig speeds and an unrivalled experience to millions of UK consumers.”
Even faster multi-gig services will be launched in 2026 the company promises.
CityFibre’s network now passes more than 4.3 million premises, which the company says means it is more than halfway along its journey towards its “rollout milestone” of 8 million premises. Actual service take-up, however, has reached just 518,000, an increase of around 181,000 customers on its previous total. During the year covered by the earnings statement, CityFibre announced a partnership with Sky that will see the UK’s second-largest broadband provider launch services on CityFibre’s network later this year.
References:
https://cityfibre.com/news/cityfibre-unveils-new-5-5gb-wholesale-product-its-fastest-ever
Nokia and CityFibre sign 10 year agreement to build 10Gb/second UK broadband network
Dell’Oro: Broadband access equipment sales to increase in 2025 led by XGS-PON deployments
Frontier Communications offers first network-wide symmetrical 5 Gig fiber internet service
Frontier Communications fiber growth accelerates in Q1 2025
AT&T grows fiber revenue 19%, 261K net fiber adds and 29.5M locations passed by its fiber optic network
Google Fiber planning 20 Gig symmetrical service via Nokia’s 25G-PON system
STELLAR Broadband offers 10 Gigabit Symmetrical Fiber Internet Access in Hudsonville, Michigan
Dell’Oro: RAN revenue growth in 1Q2025; AI RAN is a conundrum
Dell’Oro Group just completed its 1Q-2025 Radio Access Network (RAN) report. Initial findings suggest that after two years of steep declines, market conditions improved in the quarter. Preliminary estimates show that worldwide RAN revenue, excluding services, stabilized year-over-year, resulting in the first growth quarter since 1Q-2023. Author Stefan Pongratz attributes the improved conditions to favorable regional mix and easy comparisons (investments were very low same quarter lasts year), rather than a change to the fundamentals that shape the RAN market.
Pongratz believes the long-term trajectory has not changed. “While it is exciting that RAN came in as expected and the full year outlook remains on track, the message we have communicated for some time now has not changed. The RAN market is still growth-challenged as regional 5G coverage imbalances, slower data traffic growth, and monetization challenges continue to weigh on the broader growth prospects,” he added.
Vendor rankings haven’t changed much in several years, as per this table:
Additional highlights from the 1Q 2025 RAN report:
– Strong growth in North America was enough to offset declines in CALA, China, and MEA.
– The picture is less favorable outside of North America. RAN, excluding North America, recorded a fifth consecutive quarter of declines.
– Revenue rankings did not change in 1Q 2025. The top 5 RAN suppliers (4-Quarter Trailing) based on worldwide revenues are Huawei, Ericsson, Nokia, ZTE, and Samsung.
– The top 5 RAN (4-Quarter Trailing) suppliers based on revenues outside of China are Ericsson, Nokia, Huawei, Samsung, and ZTE.
– The short-term outlook is mostly unchanged, with total RAN expected to remain stable in 2025 and RAN outside of China growing at a modest pace.
Dell’Oro Group’s RAN Quarterly Report offers a complete overview of the RAN industry, with tables covering manufacturers’ and market revenue for multiple RAN segments including 5G NR Sub-7 GHz, 5G NR mmWave, LTE, macro base stations and radios, small cells, Massive MIMO, Open RAN, and vRAN. The report also tracks the RAN market by region and includes a four-quarter outlook. To purchase this report, please contact us by email at [email protected]
………………………………………………………………………………………………………………………………………………………………………………..
Separately, Pongrantz says “there is great skepticism about AI’s ability to reverse the flat revenue trajectory that has defined network operators throughout the 4G and 5G cycles.”
The 3GPP AI/ML activities and roadmap are mostly aligned with the broader efficiency aspects of the AI RAN vision, primarily focused on automation, management data analytics (MDA), SON/MDT, and over-the-air (OTA) related work (CSI, beam management, mobility, and positioning).
Current AI/ML activities align well with the AI-RAN Alliance’s vision to elevate the RAN’s potential with more automation, improved efficiencies, and new monetization opportunities. The AI-RAN Alliance envisions three key development areas: 1) AI and RAN – improving asset utilization by using a common shared infrastructure for both RAN and AI workloads, 2) AI on RAN – enabling AI applications on the RAN, 3) AI for RAN – optimizing and enhancing RAN performance. Or from an operator standpoint, AI offers the potential to boost revenue or reduce capex and opex.
While operators generally don’t consider AI the end destination, they believe more openness, virtualization, and intelligence will play essential roles in the broader RAN automation journey.
Operators are not revising their topline growth or mobile data traffic projections upward as a result of AI growing in and around the RAN. Disappointing 4G/5G returns and the failure to reverse the flattish carrier revenue trajectory is helping to explain the increased focus on what can be controlled — AI RAN is currently all about improving the performance/efficiency and reducing opex.
Since the typical gains demonstrated so far are in the 10% to 30% range for specific features, the AI RAN business case will hinge crucially on the cost and power envelope—the risk appetite for growing capex/opex is limited.
The AI-RAN business case using new hardware is difficult to justify for single-purpose tenancy. However, if the operators can use the resources for both RAN and non-RAN workloads and/or the accelerated computing cost comes down (NVIDIA recently announced ARC-Compact, an AI-RAN solution designed for D-RAN), the TAM could expand. For now, the AI service provider vision, where carriers sell unused capacity at scale, remains somewhat far-fetched, and as a result, multi-purpose tenancy is expected to account for a small share of the broader AI RAN market over the near term.
In short, improving something already done by 10% to 30% is not overly exciting. However, suppose AI embedded in the radio signal processing can realize more significant gains or help unlock new revenue opportunities by improving site utilization and providing telcos with an opportunity to sell unused RAN capacity. In that case, there are reasons to be excited. But since the latter is a lower-likelihood play, the base case expectation is that AI RAN will produce tangible value-add, and the excitement level is moderate — or as the Swedes would say, it is lagom.
…………………………………………………………………………………………………………………………………………………………………………………………………………………………………………….
Editor’s Note:
ITU-R WP 5D is working on aspects related to AI in the Radio Access Network (RAN) as part of its IMT-2030 (6G) recommendations. IMT-2030 is expected to consider an appropriate AI-native new air interface that uses to the extent practicable, and proved demonstrated actionable AI to enhance the performance of radio interface functions such as symbol detection/decoding, channel estimation etc. An appropriate AI-native radio network would enable automated and intelligent networking services such as intelligent data perception, supply of on-demand capability etc. Radio networks that support applicable AI services would be fundamental to the design of IMT technologies to serve various AI applications, and the proposed directions include on-demand uplink/sidelink-centric, deep edge, and distributed machine learning.
In summary:
- ITU-R WP5D recognizes AI as one of the key technology trends for IMT-2030 (6G).
- This includes “native AI,” which encompasses both AI-enabled air interface design and radio network for AI services.
- AI is expected to play a crucial role in enhancing the capabilities and performance of 6G networks.
…………………………………………………………………………………………………………………………………………………………………………………………………………………………………………….
References:
Dell’Oro: Private RAN revenue declines slightly, but still doing relatively better than public RAN and WLAN markets
ITU-R WP 5D reports on: IMT-2030 (“6G”) Minimum Technology Performance Requirements; Evaluation Criteria & Methodology
https://www.itu.int/dms_pubrec/itu-r/rec/m/R-REC-M.2160-0-202311-I!!PDF-E.pdf